
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > TeamPCP hackers promote Mistral AI code repos on the market

May
TeamPCP hackers promote Mistral AI code repos on the market
Cyber investigation

The TeamPCP hacker group is threatening to leak supply code from the Mistral AI mission except a buyer is chanced on for the records.
In a submit on a hacker discussion board, the threat actor is asking $25,000 for a location of practically 450 repositories.
Mistral AI is a French synthetic intelligence firm essentially based by susceptible researchers from Google’s DeepMind and Meta, which offers originate-weight clear language devices (LLMs), both originate supply and proprietary.
In a assertion to BleepingComputer, Mistral AI confirmed that hackers compromised a codebase administration system after the Mini Shai-Hulud instrument provide-chain assault.
The incident started with the compromise of loyal purposes from TanStack and Mistral AI by stolen CI/CD credentials and legit workflows.
Then it unfold to hundreds of an expansion of instrument initiatives on the npm and PyPI registries, including UiPath, Guardrails AI, and OpenSearch.
“They [the hackers] rank some of our SDK purposes for a temporary length,” the firm said.
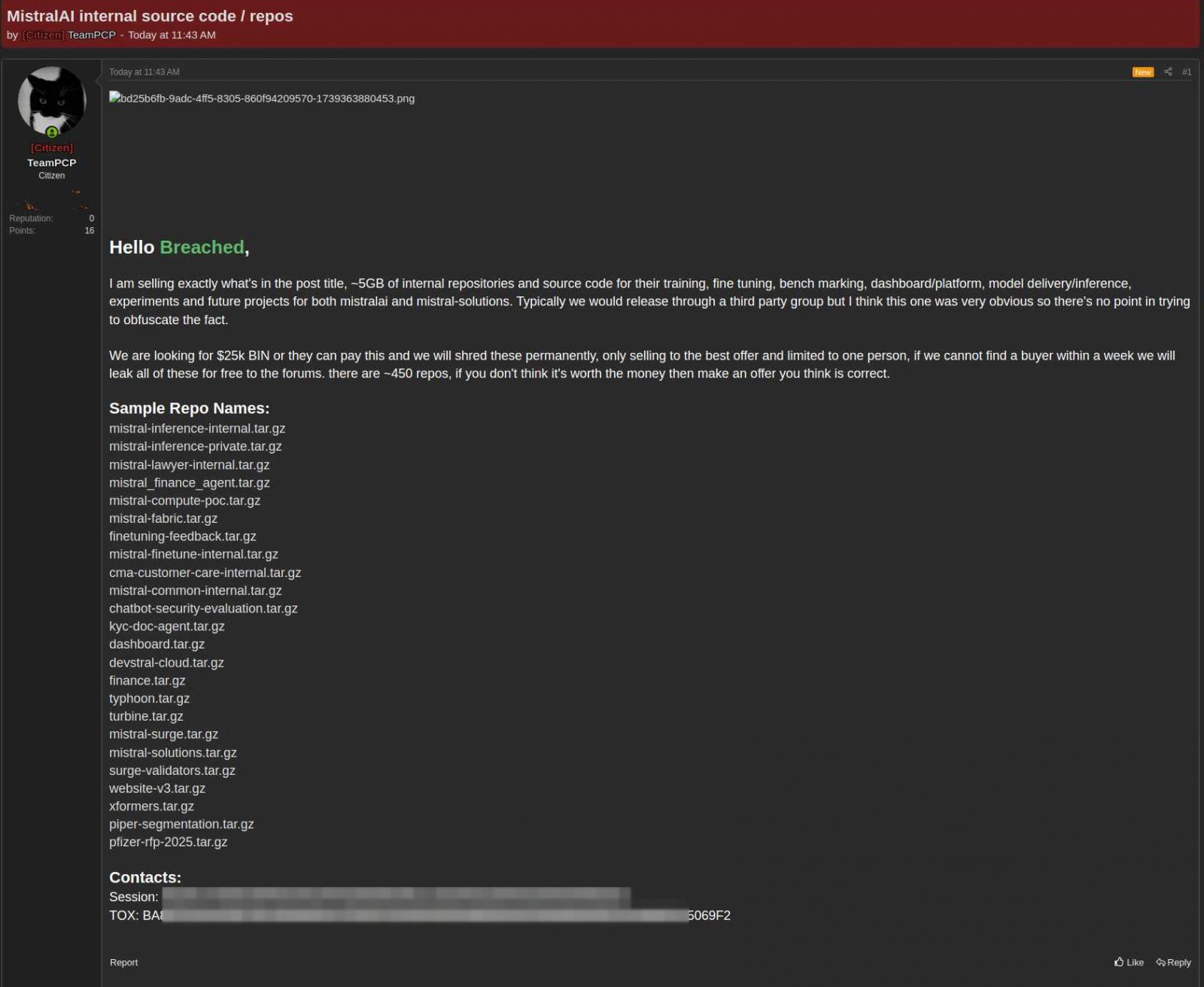
TeamPCP claims to rep stolen practically 5 gigabytes “of inner repositories and supply code” that Mistral makes exercise of for coaching, gorgeous-tuning, benchmarking, model transport, and inference in experiments and future initiatives.
“We’re attempting to acquire $25k BIN or they pays this and we’re going to shred these completely, handiest selling to the glorious offer and limited to one particular person, if we cannot obtain a buyer inner a week we’re going to leak all of these for free to the forums,” the hackers said.
The threat actor appears to be like originate to negotiations, citing that the asking tag is flexible and that merchants are free to submit what they mediate is a beautiful offer for the 450 repositories equipped on the market.
supply: KELA
Mistral AI informed BleepingComputer that the TeamPCP managed to contaminate some of the crucial firm’s instrument construction equipment (SDK) purposes.
In an advisory printed earlier this week, the firm said that the breach passed off after a developer instrument became once impacted by the TanStack provide-chain assault.
On the different hand, Mistral states that the forensic investigation determined that the impacted records became once now now not segment of the core code repositories.
“Neither our hosted services, managed user records, nor any of our learn and attempting out environments had been compromised,” Mistral informed BleepingComputer.
Earlier this day, OpenAI also confirmed that the TanStack provide-chain impacted methods of two of its workers who had access to “a limited subset of inner supply code repositories.”
A limited location of credentials became once stolen from the repositories, but the investigation chanced on no proof that they had been passe in extra attacks.
OpenAI spoke back by rotating the code-signing certificates uncovered in the incident and warning macOS customers that they rep to update their OpenAI desktop apps sooner than June 12, or the instrument might well perhaps also merely fail to begin and end receiving updates.
Cyber investigation
The Validation Gap: Automated Pentesting Solutions One Quiz. You Need Six.
Automated pentesting tools speak proper price, but they had been constructed to reply to one question: can an attacker transfer by the network? They weren’t constructed to test whether your controls block threats, your detection rules fire, or your cloud configs protect.
This handbook covers the 6 surfaces you and not utilizing a doubt desire to validate.
Recent Posts
- Nigerian con men Olalekan Bashiru, Emma Okereke, others convicted in $215 million FBI-led cyber web fraud bust
- TeamPCP hackers promote Mistral AI code repos on the market
- Hackers exploit auth bypass flaw in Burst Statistics WordPress plugin
- Crypto losses from North Korea hackers in 2025 rose 51% YoY: File
- NEET UG 2026 cancelled: Total arrests upward push to 7, role of many NTA officers under scanner — 5 facets
Recent Comments
Categories
Recent Posts




