
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Sleek node-ipc npm bundle compromised to take credentials

May
Sleek node-ipc npm bundle compromised to take credentials
Cybersecurity expert

Hackers occupy injected credential-stealing malware into newly published versions of node-ipc, a preferred inter-route of conversation bundle, in a brand fresh provide chain assault targeting npm.
The node-ipc bundle is a Node.js module that enables diversified processes to discuss thru all forms of sockets, including Unix, Windows, UDP, TLS, and TCP.
No matter the maintainer publishing in March 2022 weaponized versions that targeted Russia and Belarus-based systems with an recordsdata-overwriting module, in whisper to the Russian invasion of Ukraine, the bundle quiet has greater than 690,000 weekly downloads on npm.
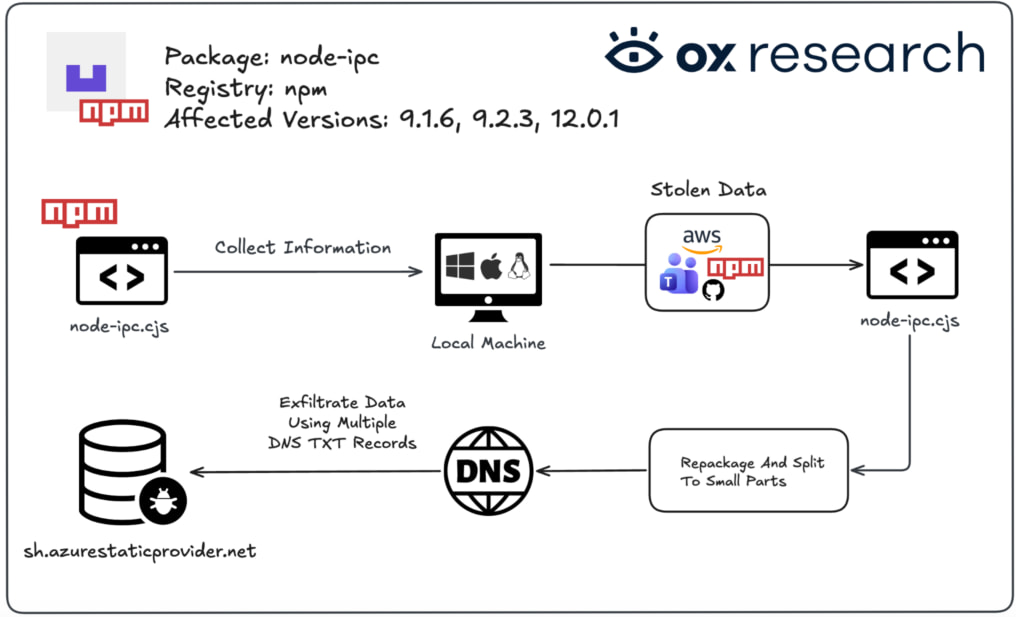
The sizzling provide-chain assault used to be detected by multiple software security companies, including Socket, Ox Security, and Upwind, who confirmed the next three versions as malicious:
- node-ipc@9.1.6
- node-ipc@9.2.3
- node-ipc@12.0.1
The malicious code hides inside of the CommonJS entrypoint (node-ipc.cjs) and executes automatically every time capabilities are loaded.
The malware is heavily obfuscated and fingerprints infected systems, collects ambiance variables and beautiful native recordsdata, compresses the stolen recordsdata into archives, and exfiltrates it thru DNS TXT queries.
Potentially the most contemporary compromise looks to be the work of an exterior actor who compromised the parable of an slothful maintainer named ‘atiertant.’
Essentially based on the researchers, the infostealer injected in the fresh node-ipc versions collects the next forms of recordsdata from compromised systems:
- Cloud credentials from AWS, Azure, GCP, OCI, DigitalOcean, and others
- SSH keys and SSH configs
- Kubernetes, Docker, Helm, and Terraform credentials
- npm, GitHub, GitLab, and Git CLI tokens
- .env recordsdata and database credentials
- Shell histories and CI/CD secrets
- macOS Keychain recordsdata and Linux keyrings
- Firefox profile and key database recordsdata (on macOS)
- Microsoft Teams native storage and IndexedDB paths
The malware skips recordsdata elevated than 4 MiB and avoids scanning .git and node_modules directories to amplify effectivity and lower operational noise on the host.
Source: Ox Learn
A important operational attribute is the utilize of DNS TXT queries as an alternate of feeble HTTP-based repeat-and-adjust (C2) traffic for recordsdata exfiltration. The attackers utilize a incorrect Azure-themed domain (sh[.]azurestaticprovider[.]accumulate:443) as a bootstrap resolver, transmitting the guidelines to ‘bt[.]node[.]js’ with ask prefixes like xh, xd, and xf.
Essentially based on Socket, exfiltrating a 500 KB compressed archive could well generate roughly 29,400 DNS TXT requests, helping the traffic blend into abnormal DNS activity.
Sooner than submission, the malware stores peaceable recordsdata in immediate compressed tar.gz archives, which could well well be deleted after exfiltration to lower forensic traces.
The malware doesn’t build persistence or get any secondary payloads, so the operation looks targeted on mercurial credential theft and exfiltration.
Potentially impacted builders ought to straight away cast off the affected versions, rotate exposed secrets and credentials, and behold lockfiles and npm caches.
Cybersecurity expert
The Validation Gap: Automatic Pentesting Solutions One Search recordsdata from. You Need Six.
Automatic pentesting instruments sing real ticket, but they were built to answer to 1 ask: can an attacker pass thru the network? They weren’t built to check whether your controls block threats, your detection rules fire, or your cloud configs believe.
This handbook covers the 6 surfaces you definitely want to validate.
Recent Posts
- Chinese language hackers inclined to US arrest if they disappear back and forth, FBI educated says
- Sleek node-ipc npm bundle compromised to take credentials
- Cyprus Detains Police Officer, Two Others in Forex-Linked Crime Ring Probe: Story
- Avada Builder WordPress plugin flaws enable space credential theft
- Senator Warren Urges SEC to Study Trump-Linked Crypto Firm WLFI
Recent Comments
Categories
Recent Posts




