
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity > Russian hackers turn Kazuar backdoor into modular P2P botnet

May
Russian hackers turn Kazuar backdoor into modular P2P botnet
Digital forensics

The Russian hacker neighborhood Secret Blizzard has developed its prolonged-running Kazuar backdoor into a modular look-to-look (P2P) botnet designed for prolonged-term persistence, stealth, and info series.
Secret Blizzard, whose exercise overlaps that of Turla, Uroburos, and Venomous Maintain, has been linked to the Russian intelligence service (FSB) and is legendary for concentrating on authorities and diplomatic organizations, defense-linked entities, and severe programs across Europe, Asia, and Ukraine.
The Kazuar malware has been documented since 2017, and researchers found that its code lineage goes as a long way succor as 2005. Its exercise has been linked to the Turla espionage neighborhood working for the FSB.
In 2020, researchers exposed its deployment in attacks concentrating on European authorities organizations. Three years later, it became viewed deployed in attacks in opposition to Ukraine.
“Leading” Kazuar
Microsoft researchers analyzed a up to date variant of Kazuar and seen that the malware now operates the usage of three definite modules: kernel, bridge, and employee.
The Kernel module is the central coordinator that manages duties, controls diverse modules, elects a leader, and orchestrates communications and info circulate across the botnet.
The leader is in point of fact one infected arrangement within a compromised ambiance or network section, which communicates with the divulge-and-control (C2) server, receives duties, and forwards them internally to the different infected programs.
Non-leader programs enter “restful” mode and don’t communicate straight with the C2. This ends in better stealth and decreased detection ground.
“The Kernel leader is the one elected Kernel module that communicates with the Bridge module on behalf of the different Kernel modules, cutting back visibility by averting powerful volumes of external traffic from just a few infected hosts,” explains Microsoft.
The course of for deciding on the leader is within and self sustaining, the usage of uptime, reboot, and interruption counts.
The Bridge module acts because the external communications proxy that relays traffic between the elected Kernel leader and the faraway C2 infrastructure the usage of protocols like HTTP, WebSockets, or Commerce Web Companies (EWS).
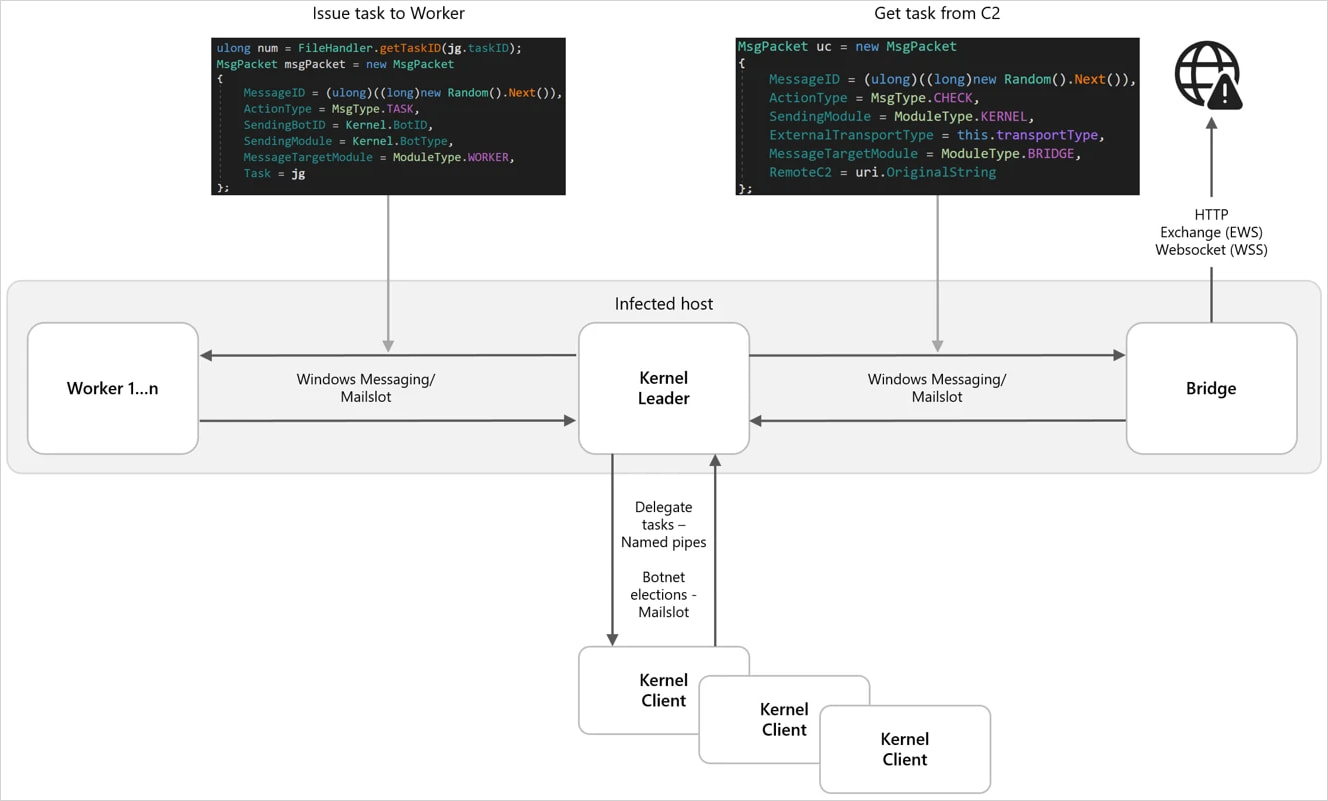
Provide: Microsoft
Inner communications depend on IPC (inter-course of verbal exchange), including Residence windows Messaging, Mailslots, and named pipes, mixing well with normal operational noise. The messages are AES-encrypted and serialized with Google Protocol Buffers (Protobuf).
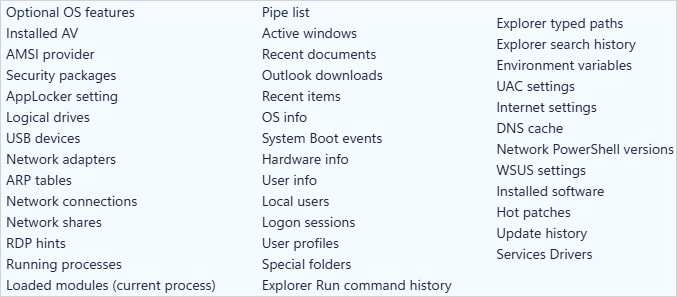
The Employee module performs the precise espionage operations, a lot like:
- keylogging
- capturing screenshots
- harvesting info from the filesystem
- performing arrangement and network reconnaissance
- collecting email/MAPI info (including Outlook downloads)
- monitoring windows
- stealing contemporary info
The light info is encrypted, staged within the neighborhood, and later exfiltrated thru the Bridge module.
Provide: Microsoft
Microsoft underlines Kazuar’s versatility, which now helps 150 configuration choices permitting operators to enable/disable particular security bypasses, save job scheduling, time the info theft and dimension of exfiltration chunks, save course of injection, space up duties and divulge execution, and more.
Relating to the safety bypass choices, Kazuar now affords Antimalware Scan Interface (AMSI) bypass, Event Tracing for Residence windows (ETW) bypass, and Residence windows Lockdown Coverage (WLDP) bypass.
Secret Blizzard usually seeks prolonged-term persistence no longer off note programs for intelligence collections. The actor exfiltrates documents and email convey that has political significance.
Microsoft recommends that corporations focal point their defense on behavioral detection as but any other of static signatures, as Kazuar’s modular and highly configurable nature makes the threat critically evasive.
Digital forensics
The Validation Gap: Automatic Pentesting Answers One Inquire of of. You Need Six.
Automatic pentesting instruments bring precise price, but they had been built to reply to 1 request: can an attacker pass thru the network? They weren’t built to test whether your controls block threats, your detection guidelines fire, or your cloud configs defend.
This info covers the 6 surfaces you no doubt must validate.
Recent Posts
- Union Minister Bandi Sanjay Kumar’s son Bhageerath surrenders amid POCSO investigation
- Russian hackers turn Kazuar backdoor into modular P2P botnet
- Chinese language hackers inclined to US arrest if they disappear back and forth, FBI educated says
- Texas Children’s will accumulate ‘detransition clinic’ to select DOJ and impart investigation – NBC Info
- FBI Director Kash Patel Celebrates Fundamental Victories: Extra than Two Dozen Tren de Aragua Gang Members Arrested



