
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity > MuddyWater hackers exhaust Chaos ransomware as a decoy in attacks

May
MuddyWater hackers exhaust Chaos ransomware as a decoy in attacks
Private eye

The MuddyWater Iranian hackers disguised their operations as a Chaos ransomware assault, counting on Microsoft Teams social engineering to blueprint bring collectively entry to and fasten persistence.
Even though the assault eager credential theft, persistence, a ways flung bring collectively entry to, knowledge exfiltration, extortion emails, and an entry on the Chaos leak portal, the attackers inclined infrastructure and ways linked with the MuddyWater attacks.
Rapid7 researchers deem that the ransomware part became as soon as seemingly inclined to conceal the exact cyber-espionage operation and to complicate attribution.
“The technique highlights the convergence between convey-sponsored intrusion yell and prison tradecraft, where a mountainous “repeat” lies within the ways that were deployed – and folks that weren’t. This system suggests the principle goal became as soon as not monetary blueprint,” explains Rapid7.
No topic the facade, Rapid7 has life like self belief in attributing the incident to MuddyWater, a menace community additionally identified as Static Kitten, Mango Sandstorm, and Seedworm.
The conclusion is primarily based utterly on infrastructure overlap, a insist code-signing certificates that the convey-sponsored community inclined to signal Stagecomp and Darkcomp malware attributed to the menace actor, and assorted operational tradecraft.
MuddyWater is an Iranian convey-sponsored cyber-espionage community, infamous for long-time-frame network intrusion campaigns that align with the country’s Ministry of Intelligence and Security (MOIS).
The Chaos is a ransomware-as-a-provider (RaaS) operation that emerged in 2025 and is identified for mountainous-sport hunting attacks, double-extortion tactics, and social engineering campaigns largely concentrated on organizations within the United States.
Attack development
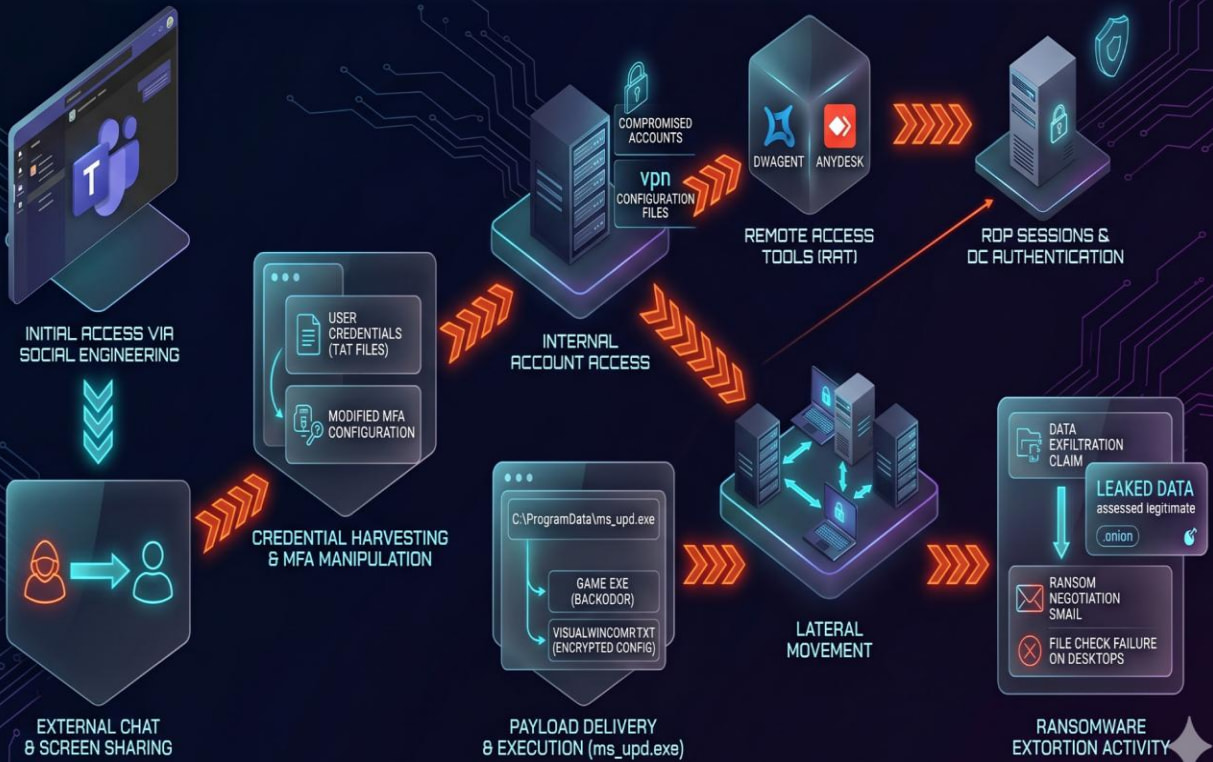
The intrusion Rapid7 examined started by Microsoft Teams social engineering, where the attackers initiated chats with employees, established show camouflage-sharing classes, harvested credentials, manipulated multi-factor authentication (MFA) settings, and, in some cases, deployed AnyDesk for a ways flung bring collectively entry to.
Credential theft occurred either via phishing pages masquerading as Microsoft Swiftly Lend a hand or by tricking victims into typing their passwords into local textual roar files.
After compromising accounts, the attackers authenticated to internal systems, including a website online controller, and established persistence the usage of RDP, DWAgent, and AnyDesk.
Subsequent, they leveraged a malware loader (ms_upd.exe) to drop a customized backdoor (Game.exe), disguised as a Microsoft WebView2 utility.
The malware points anti-prognosis and anti-VM checks, and supports 12 instructions, including PowerShell and CMD recount execution, file add and deletion, and power shell bring collectively entry to.
Supply: Rapid7
Rapid7 notes that MuddyWater has inclined ransomware within the previous to conceal its cyber-espionage operations. In tiresome 2025, the menace actor deployed Qilin ransomware in an assault against an Israeli group.
The researchers indicate that the menace community would possibly perhaps perhaps need pivoted to a particular ransomware branding following the attribution of that tiresome 2025 to MOIS operatives.
Private eye
99% of What Mythos Learned Is Quiet Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of as much as date exploits is coming.
At the Self sustaining Validation Summit (Can also merely 12 & 14), glimpse how self reliant, context-filthy rich validation finds what’s exploitable, proves controls preserve, and closes the remediation loop.
Tags
- cybercrime cybercrimehacker cybercrimephishing-attack cybersecurity email-fraud forensics|digital-forensics hacker hackers Investigation malware malwarefraud MuddyWater online-scam private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker
Recent Posts
- AI overview startup Braintrust confirms breach, tells every buyer to rotate sensitive keys
- Hackers Hate AI Slop Even More Than You Attain
- MuddyWater hackers exhaust Chaos ransomware as a decoy in attacks
- FBI nabs bigger than 350 alleged youngster intercourse abuse offenders
- CNN: Trump Admin Opening Investigation Into Smith School in ‘Most modern Dart to Limit Trans Rights’
Recent Comments
Categories
Recent Posts




