
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Instructure confirms records breach, ShinyHunters claims attack

May
Instructure confirms records breach, ShinyHunters claims attack
Internet investigation

Academic tech big Instructure has confirmed that records turn out to be stolen in a cyberattack, with the ShinyHunters extortion gang claiming duty.
Instructure is a U.S.-based totally education technology company most appealing known for setting up Canvas, a widely outdated discovering out management plot that helps colleges, universities, and organizations manage coursework, assignments, and online discovering out.
On Friday, Instructure disclosed that it suffered a cybersecurity incident and is working with third-birthday party cybersecurity consultants and law enforcement to analyze it.
On Saturday, the corporate issued an exchange declaring that the non-public records of customers turn out to be uncovered in the breach.
“While we continue actively investigating, thus far, indications are that the information involved consists of certain identifying information of users at affected institutions, such as names, email addresses, and student ID numbers, as well as messages among users,” reads the updated assertion.
“At this time, we have found no evidence that passwords, dates of birth, government identifiers, or financial information were involved. If that changes, we will notify any impacted institutions.”
As fragment of the response, Instructure has deployed patches, increased monitoring, and turned around utility keys as a precautionary step.
Customers are required to re-authorize in discovering entry to to Instructure’s API for new utility keys to be issued.
Whereas Instructure has no longer replied to BleepingComputer’s questions about when the breach happened and whether or not they were being extorted, the ShinyHunters extortion gang has now listed the corporate on its records leak location.
“Nearly 9,000 schools worldwide affected. 275 million individuals data ranging from students, teachers, and other staff containing PII,” reads the records leak location.
“Several billions of private messages among students and teachers and students and other students involved, containing personal conversations and other PII. Your Salesforce instance was also breached and a lot more other data is involved.”
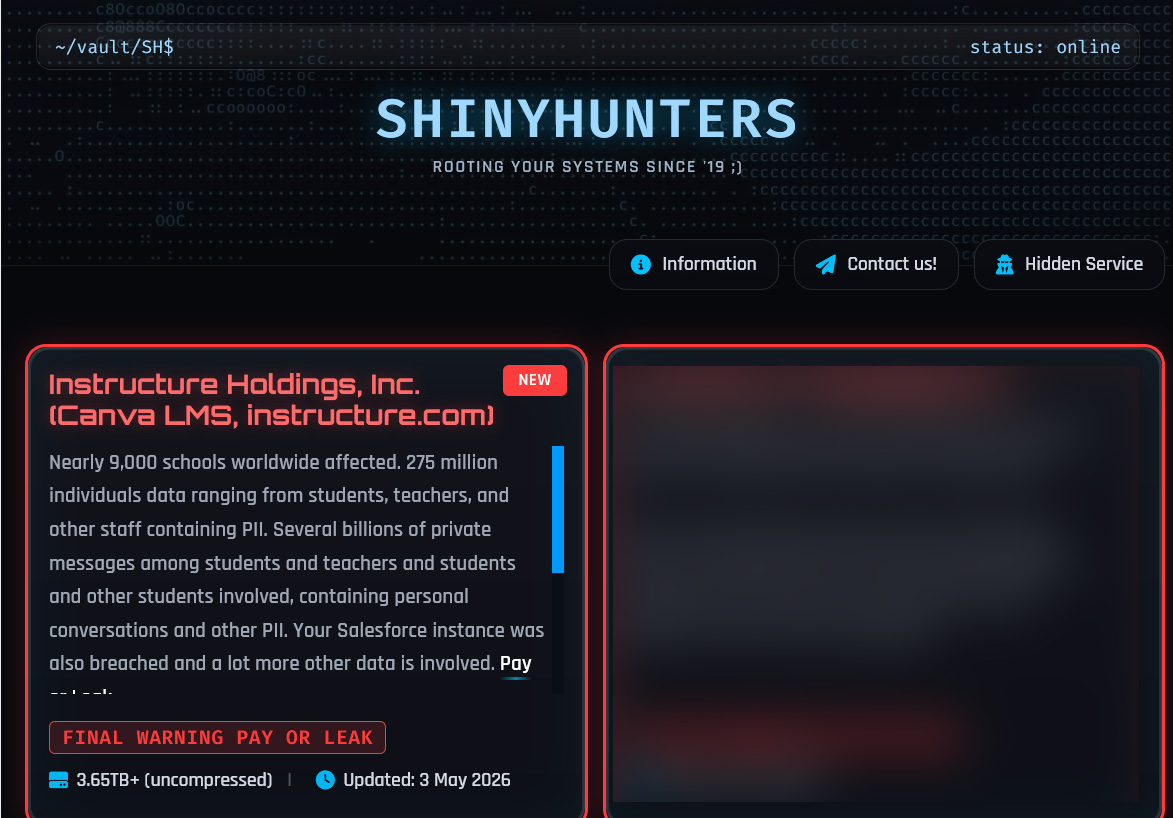
ShinyHunters claimed that the records turn out to be stolen from Instructure by process of a vulnerability in their methods, which has now been patched.
This records allegedly contains over 240 million files tied to varsity students, lecturers, and employees. The threat actor says the records comprises college students’ names, electronic mail addresses, enrolled capabilities, and interior most messages to lecturers.
Files shared by the threat actor means that the alleged dataset spans nearly 15,000 institutions hosted across just a few geographic areas, alongside with North The US, Europe, and Asia-Pacific.
BleepingComputer has no longer been in a discipline to independently ascertain which colleges or how many folks were impacted and has contacted Instructure with extra questions relating to the threat actor’s claims.
Internet investigation
99% of What Mythos Learned Is Restful Unpatched.
AI chained four zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of glossy exploits is coming.
At the Independent Validation Summit (Would possibly maybe maybe maybe also 12 & 14), ogle how self sustaining, context-rich validation finds what’s exploitable, proves controls protect, and closes the remediation loop.
Recent Posts
- Staff are now more unpleasant to their firm than exterior hackers
- The West keeps asking how mighty China subsidises its industries. That is the harmful quiz.
- Instructure confirms records breach, ShinyHunters claims attack
- Pirro appears to be like to fall plans to appeal criminal investigation of Fed Chair Powell
- A Tether-linked billionaire poured £22M into UK politics – Now novel donation suggestions would possibly maybe well moreover close the door



