
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Hackers exploit Marimo flaw to deploy NKAbuse malware from Hugging Face

Apr
Hackers exploit Marimo flaw to deploy NKAbuse malware from Hugging Face
Data breach

Hackers are exploiting an vital vulnerability in Marimo reactive Python pocket book to deploy a brand novel variant of NKAbuse malware hosted on Hugging Face Areas.
Assaults leveraging the a long way away code execution flaw (CVE-2026-39987) started final week for credential theft, now not up to 10 hours after technical necessary facets had been disclosed publicly, in accordance to knowledge from cloud-security company Sysdig.
Sysdig researchers persevered to video show process linked to the protection area identified additional attacks, in conjunction with a campaign that started on April 12 that abuses the Hugging Face Areas platform for showcasing AI beneficial properties.
Hugging Face serves as an AI constructing and machine finding out-centered platform, appearing as a hub for AI sources comparable to objects, datasets, code, and tools, shared amongst the neighborhood.
Hugging Face Areas lets users deploy and share interactive internet apps right faraway from a Git repository, most steadily for demos, tools, or experiments around AI.
In the attacks that Sysdig observed, the attacker created a Residence named vsccode-modetx (an intentional typosquat for VS Code) that hosts a dropper script (install-linux.sh) and a malware binary with the name kagent, also an are attempting to mimic a sound Kubernetes AI agent tool.
After exploiting the Marimo RCE, the threat actor ran a curl order to download the script from Hugging Face and kind it. As a end result of Hugging Face Areas is a sound HTTPS endpoint with a trim reputation, it’s miles less at probability of trigger indicators.
The dropper script downloads the kagent binary, installs it in the neighborhood, and objects up persistence by systemd, cron, or macOS LaunchAgent.
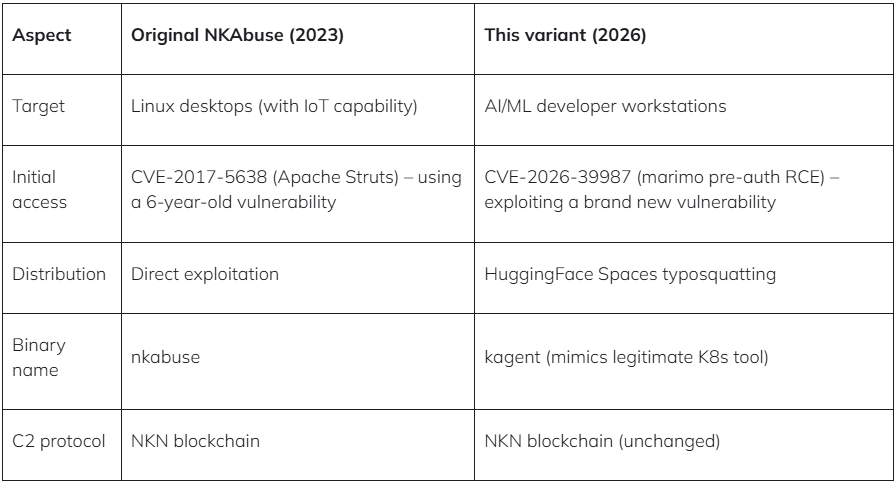
In step with the researchers, the payload is a beforehand undocumented variant of the DDoS-centered malware NKAbuse. Kaspersky researchers reported the malware in gradual 2023 and highlighted its unique abuse of the NKN (Original Form of Network) decentralized glance-to-glance network skills for knowledge alternate.
Sysdig says that the novel variant beneficial properties as a a lot away secure entry to trojan that might per chance well kind shell instructions on the contaminated plan and send the output back to the operator.
“The binary references NKN Client Protocol, WebRTC/ICE/STUN for NAT traversal, proxy administration, and structured order handling – matching the NKAbuse family on the starting achieve documented by Kaspersky in December 2023,” mentions Sysdig in the document.
Sysdig also noticed other indispensable attacks exploiting CVE-2026-39987, in conjunction with a Germany-essentially essentially essentially based operator who attempted 15 reverse-shell ways all over more than one ports.
They then pivoted to lateral circulate by extracting database credentials from ambiance variables and connecting to PostgreSQL, where they quickly enumerated schemas, tables, and configuration knowledge.
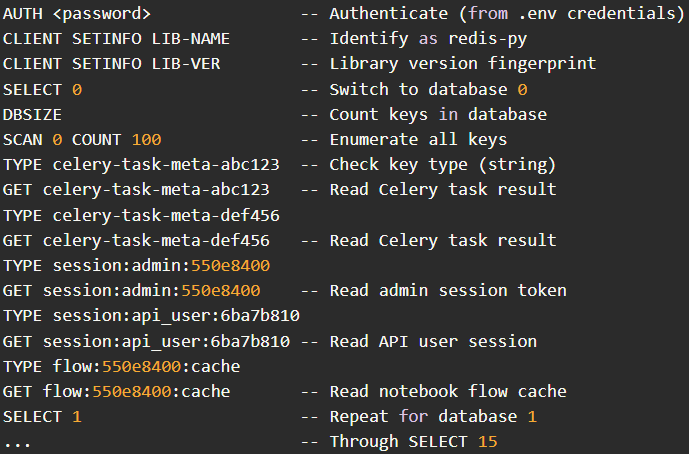
Another actor from Hong Kong feeble stolen .env credentials to focal point on a Redis server, systematically scanning all 16 databases and dumping kept knowledge, in conjunction with session tokens and application cache entries.
The general takeaway is that exploitation of CVE-2026-39987 in the wild has elevated in quantity and ways, and it’s a truly mighty that users upgrade to model 0.23.0 or later immediately.
If upgrading is now not most likely, it’s miles strongly instructed to dam external secure entry to to the ‘/terminal/ws’ endpoint by a firewall, or block it entirely.
Data breach Ninety 9% of What Mythos Stumbled on Is Nonetheless Unpatched.
AI chained four zero-days into one exploit that bypassed every renderer and OS sandboxes. A wave of novel exploits is coming.
On the Self ample Validation Summit (Can also 12 & 14), study how self sustaining, context-prosperous validation finds what’s exploitable, proves controls sustain, and closes the remediation loop.
Recent Posts
- Clippers star Kawhi Leonard, proprietor Steve Ballmer interviewed for position in Aspiration scandal
- South Korea Launches Prison Investigation Into Polymarket Bettors
- Compass Faces Antitrust Probe in Contemporary York After Megamerger With Wherever
- Police Force Enthusiastic In Lego Investigation ‘Hacked,’ YouTuber Claims, As New Footage Is Launched
- Lawmakers name for federal investigation into gambling dysfunction
Recent Comments
Categories
Recent Posts





