
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > FBI takedown of W3LL phishing service leads to developer arrest

Apr
FBI takedown of W3LL phishing service leads to developer arrest
Cybersecurity expert

The FBI Atlanta Field Place of job and Indonesian authorities believe dismantled the “W3LL” global phishing platform, seizing infrastructure and involving the alleged developer in what’s described as the essential coordinated enforcement action between the US and Indonesia focusing on a phishing kit developer.
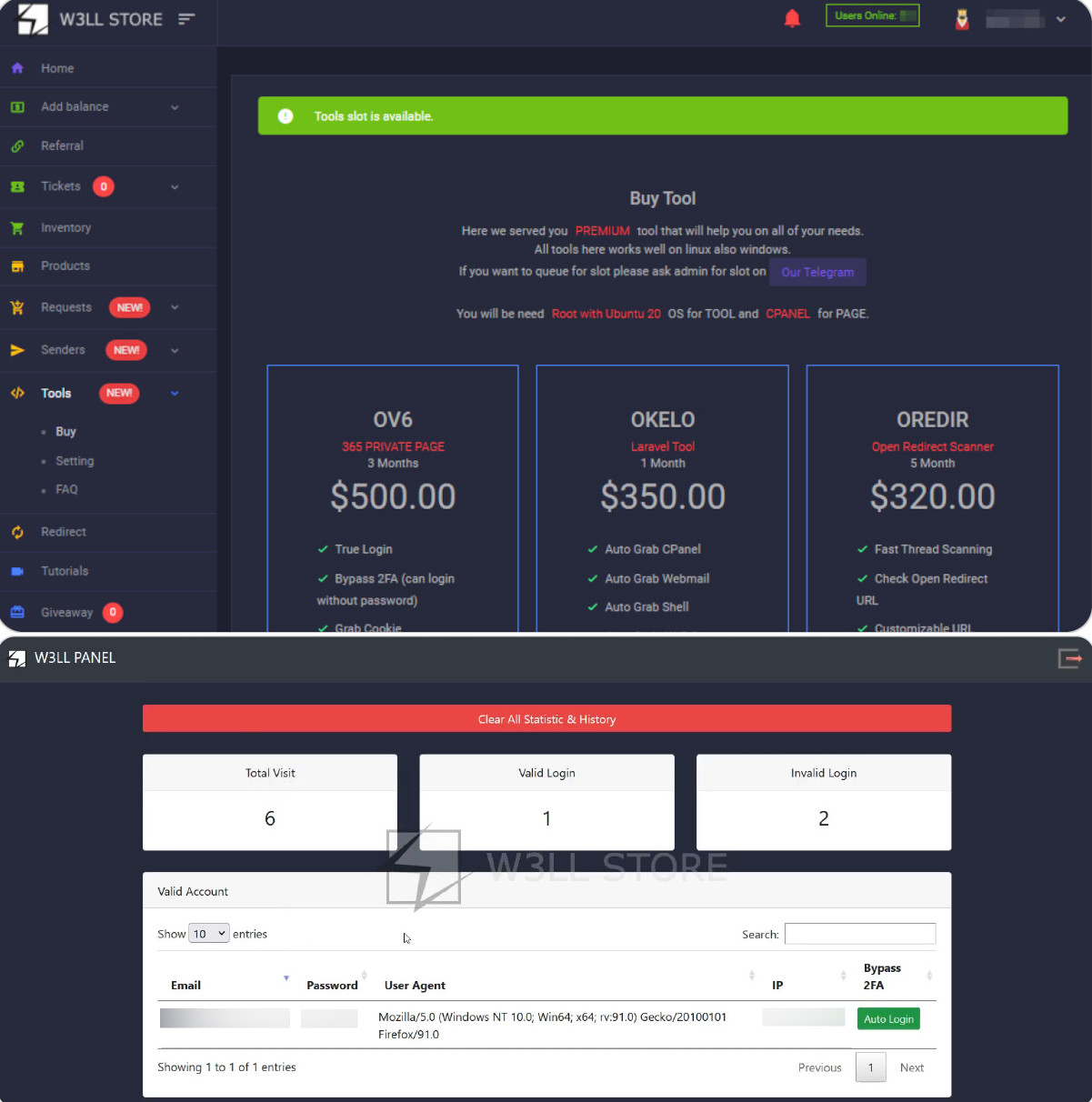
The W3ll Store used to be a phishing kit and online marketplace that enabled cybercriminals to take hundreds of credentials and strive extra than $20 million in fraud.
“This Website Has Been Seized as part of a coordinated law enforcement action taken against W3LL STORE,” reads a seizure message on w3ll[.]retailer web sites.
“The domain for w3ll.store has been seized by the Federal Bureau of Investigation in accordance with a seizure warrant issued pursuant to 18 U.S.C. §§ 981 and 982 by the United States District Court for the Northern District of Georgia as part of a joint law enforcement action by the Federal Bureau of Investigation.”

Source: BleepingComputer
The W3LL phishing kit equipped for $500 and allowed attackers to assemble convincing replicas of corporate login portals to harvest credentials. The kit allowed threat actors to capture authentication session tokens, enabling attackers to bypass multi-impart authentication and to find entry to compromised accounts.
Source: Neighborhood-IB
The threat actor additionally equipped a marketplace called W3LLSTORE, the put stolen credentials and unauthorized community entry were bought and equipped.
“This wasn’t just phishing—it was a full-service cybercrime platform,” said FBI Particular Agent Cost Marlo Graham.
Authorities yelp the marketplace facilitated the sale of extra than 25,000 compromised accounts between 2019 and 2023, and even after W3LLSTORE shut down, the operation persevered through encrypted messaging platforms, the put the toolkit used to be rebranded and equipped to utterly different threat actors.
Between 2023 and 2024, the phishing kit used to be veteran to specialise in extra than 17,000 victims worldwide, with investigators discovering that the developer mute and resold entry to compromised accounts.
The W3LL phishing platform used to be beforehand linked to campaigns focusing on Microsoft 365 corporate accounts and used to be designed to red meat up trade electronic mail compromise (BEC) assaults from preliminary entry through publish-exploitation.
The phishing kit relied on adversary-in-the-heart assaults, which is when official login portals are proxied through an attacker’s infrastructure.
This enables the threat actors to display screen for and intercept credentials, one-time MFA passcodes, and session cookies in proper time. These session cookies could per chance per chance then be veteran to log into the compromised accounts with out triggering MFA authentication challenges.
Once entry used to be obtained, attackers would display screen inboxes, assemble electronic mail rules, and impersonate victims to commit invoice fraud and redirect funds in BEC assaults.
Cybersecurity expert Automated Pentesting Covers Handiest 1 of 6 Surfaces.
Automated pentesting proves the drag exists. BAS proves whether your controls discontinuance it. Most teams crawl one with out the completely different.
This whitepaper maps six validation surfaces, displays the put coverage ends, and presents practitioners with three diagnostic questions for any machine evaluate.
Recent Posts
- Lawmakers name for federal investigation into gambling dysfunction
- James Comey: ‘Justice Can’t Be a Political Force’
- AI Is Handing Hackers Instruments That Once Belonged to Elite Attackers
- Of us Energy Rep collectively protests pollscarcity at Seoul polling stations
- Disabled ACR to your TV? I prepare a router-primarily based VPN for extra protection




