
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity > FBI links cybercriminals to fascinating surge in cargo theft assaults

Apr
FBI links cybercriminals to fascinating surge in cargo theft assaults
OSINT

The U.S. Federal Bureau of Investigation (FBI) warned the transportation and logistics change of a fascinating rise in cyber-enabled cargo theft, with estimated losses within the united states and Canada reaching practically $725 million in 2025.
This represents a 60% surge in losses in comparison to the old year, fueled by criminals increasingly extra using hacking and impersonation tactics to hijack excessive-value freight. Confirmed cargo theft incidents possess risen 18 percent final year on my own, while the common value per theft grew 36 percent to $273,990, due to extra selective concentrated on of excessive-value loads.
The bureau said in a public provider announcement on Wednesday that threat actors had been infiltrating the pc programs of freight brokers and carriers by plot of spoofed emails and counterfeit internet links since a minimal of 2024.
Once inner, criminals post untrue listings on on-line load boards (digital marketplaces outdated by shippers, brokers, and carriers) and impersonate legitimate firms to divert shipments.
Shall we embrace, in February, the typosquatting monitoring platform Dangle I Been Squatted reported that the Diesel Vortex financially motivated threat community became stealing credentials from freight and logistics operators within the U.S. and Europe in phishing assaults that had been working since September 2025 and had been using 52 domains.
“The Federal Bureau of Investigation is publishing this Public Service Announcement (PSA) to warn the public of cyber threat actors increasingly using sophisticated, cyber-enabled tactics to impersonate legitimate businesses to hijack freight, steal high-value shipments, and reroute deliveries, resulting in a surge of strategic cargo theft,” the FBI warned.
“Cyber threat actors target US transportation and logistics sectors, including companies with interests in shipping, receiving, delivering, and insuring cargo.”
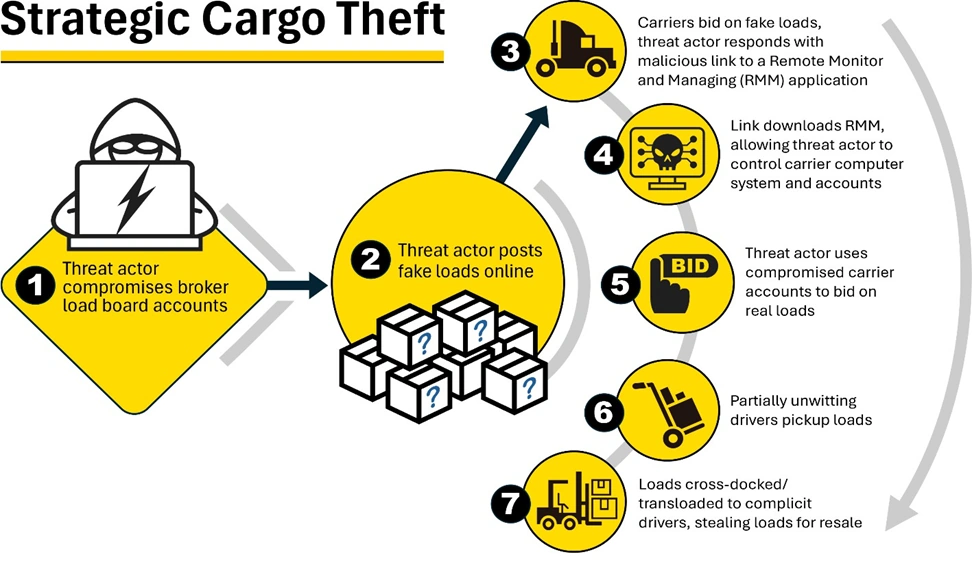
Attackers first compromise broker or provider accounts by luring workers to phishing internet sites that install far off monitoring tool, after which reach undetected entry to the focused firm’s programs.
In the subsequent stage, they post tens of hundreds of counterfeit freight listings, tricking legitimate carriers into downloading malicious info, after which salvage valid shipments below a stolen provider identification. The loads are rerouted to complicit drivers, stolen for resale, and, in some cases, the criminals also predict ransoms for the placement of diverted loads.
Threat actors linked to cyber-enabled cargo theft assaults will also alter the compromised provider’s registration particulars with the Federal Motor Provider Security Administration and update insurance info, thus guaranteeing that legitimate firms will watch they’ve been hacked till brokers describe missing shipments booked in their title with out their info.
To dam cyber-enabled cargo theft makes an are trying, the bureau knowledgeable transportation and logistics firms to possess a look the least bit cargo requests by plot of secondary channels, implement and put in pressure multi-ingredient authentication when seemingly, validate all sudden communications using a two-ingredient authentication process, and withhold detailed info of all vehicles and drivers.
The FBI also knowledgeable victims of cyber-enabled cargo theft schemes to file a criticism with the Web Crime Complaint Center (IC3) as well to submitting police stories for the stolen cargo.
In its 2025 Web Crime File, released earlier this month, the FBI said IC3 got over 1 million complaints final year, linked to practically $21 billion in reported losses from totally different cyber-enabled crimes, at the side of funding scams, tech make stronger fraud, change electronic mail compromise, and info breaches.
OSINT
99% of What Mythos Figured out Is Mute Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of contemporary exploits is coming.
On the Self reliant Validation Summit (Can also 12 & 14), seek how autonomous, context-prosperous validation finds what’s exploitable, proves controls withhold, and closes the remediation loop.
Tags
- cybercrime cybercrimehacker Cybercriminals cybersecurity email-fraud forensics|digital-forensics hacker Investigation links malware malwarephishing-attack online-scam private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker
Recent Posts
- Kash Patel Finds 4 Noncitizens Charged with Illegally Voting in Elections
- Adrian Sutil’s $22million Koenigsegg hypercar goes missing amid alleged blackmail case
- Florida Opens Legal Probe Into Sloth World After Dozens of Animal Deaths
- Trump DOJ Indicts Comey Over That Seashell Picture
- James Comey indicted again, this time over “86 47” photo



