
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Checkmarx confirms LAPSUS$ hackers leaked its stolen GitHub records

Apr
Checkmarx confirms LAPSUS$ hackers leaked its stolen GitHub records
Online fraud

Utility safety company Checkmarx has confirmed that the LAPSUS$ threat group leaked records stolen from its non-public GitHub repository.
Despite the indisputable fact that the investigation is ongoing, Checkmarx believes that the access vector changed into once the Trivy supply-chain assault attributed to the hacker group diagnosed as TeamPCP. which equipped access to credentials from downstream customers.
The employ of stolen credentials received from the Trivy incident, the threat actor changed into once ready to access Checkmarx’s GitHub repositories and post malicious code on March 23.
“As a result of that access, the attackers were able to interact with Checkmarx’s GitHub environment and subsequently publish malicious code to certain artifacts,” the company explains.
On April 22, as a results of their renewed access or month-lengthy persistence, the attacker printed malicious Docker pictures, VSCode and Open VSX extensions for Checkmarx’s KICS safety scanner, which stole credentials, keys, tokens, and config files.
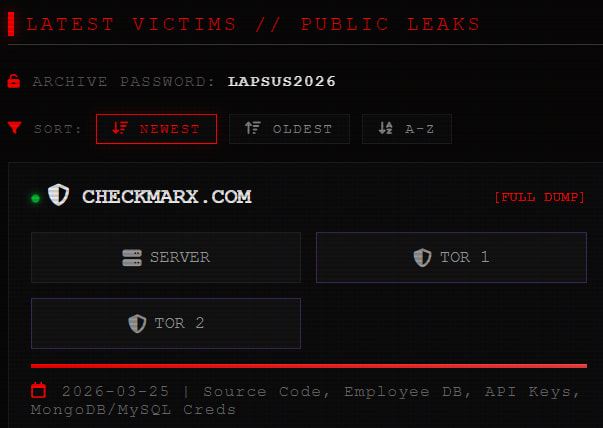
In an replace the day earlier than today, the company confirmed that the records that the LAPSUS$ group printed on their extortion portal belonged to Checkmarx and originated from the March 23 compromise.
“Our investigation, conducted with strengthen from a number one third-celebration forensic company, indicates that a cybercriminal group has printed records linked to Checkmarx to the darkish web,” reads the replace.
“Primarily essentially based solely on contemporary evidence, we judge this records originated from Checkmarx’s GitHub repository, and that access to that repository changed into once facilitated in the course of the preliminary supply chain assault of March 23, 2026.”
Despite the indisputable fact that Checkmarx and varied media stores reported that this records changed into once leaked on the darkish web, BleepingComputer has chanced on that LAPSUS$ has additionally made the 96GB records pack available through clearnet portals.
Source: BleepingComputer
BleepingComputer has no longer examined the yelp material of the leaked records, however Checkmarx assured that it does no longer comprise customer records, as here is no longer kept in the company’s GitHub repository.
A forensic investigation is underway to resolve the actual vogue of records that has been uncovered.
The company states that, if customer records is chanced on in the leaked records, affected other folks will be notified without lengthen.
Procure entry to to the affected GitHub repository has been blocked till the investigation is full. Checkmarx estimates that this will be ready to fragment extra crucial ingredients interior the next 24 hours.
Online fraud
ninety nine% of What Mythos Chanced on Is Aloof Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Independent Validation Summit (Would possibly per chance well 12 & 14), look how self sustaining, context-rich validation finds what’s exploitable, proves controls preserve, and closes the remediation loop.
Recent Posts
- Again, Ex-FBI Director Comey Indicted Over Controversial ‘86 47’ Instagram Post
- Ex-FBI director responds to indictment over seashell photograph
- Hackers reveal private info of hundreds of Marines…
- US glance agencies overview how Tehran would react to victory declaration…
- Trump Aides Leak Fears of Toxic Iran Stalemate…



