
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Tag: private-eye phishing|phishing-attack
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > private-eye phishing|phishing-attack
Ultra-Life like AI Face Swapping Platform Utilizing Romance Scams…
Internet investigation Internet investigation One extra step Internet investigation Please total the protection check to access Internet investigation Why form I in actuality want to total a CAPTCHA? Finishing the CAPTCHA proves you are a human and gives you non permanent access to the web property. Internet investigation What can I form to prevent this […]

Dec
Pam Bondi is likely to be convicted of obstruction of justice over partial commence of redacted Epstein recordsdata, Massie says – live
Internet investigation Internet investigation Ro Khanna says this ‘file dump doesn’t modify to’ regulation to compel fats commence of Epstein recordsdata “The justice department’s file dump this afternoon doesn’t modify to Thomas Massie and my Epstein Transparency Act,” Ro Khanna, the California Democratic congressman who co-wrote the regulation requiring fats disclosure of all of the […]
Dec
One in every of the few revelations within the Epstein recordsdata is a duplicate of the earliest known crimson flag about the sex culprit: a document taken by the FBI in 1996
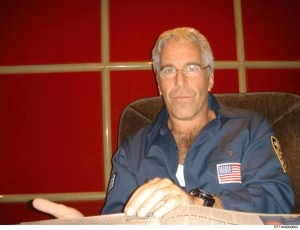
Cybercrime The Justice Department launched thousands of recordsdata Friday about convicted sex culprit Jeffrey Epstein, however the incomplete document dump did no longer shatter indispensable ground about the long-running prison investigations of the financier or his ties to neatly off and strong folk. The recordsdata integrated photos of neatly-known of us that frolicked with Epstein within […]

Dec
Trump news at a behold: Division of Justice releases heavily redacted cache of Epstein recordsdata
Internet investigation The Division of Justice on Friday released a protracted-awaited and monumental tranche of documents detailing its investigations into the convicted intercourse perpetrator Jeffrey Epstein, a well-known pattern in the lengthy saga that grew to change into into regarded as one of the greatest political setbacks Donald Trump has suffered since his re-election final […]
Dec
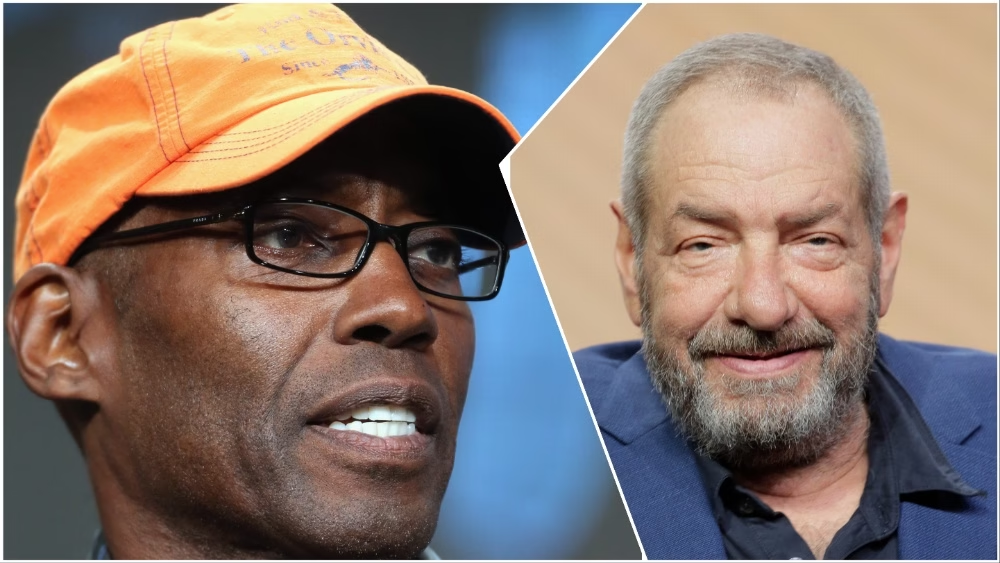
Dick Wolf Leads Tributes To His ‘Composed York Undercover’ Co-Creator Kevin Arkadie
Online fraud Dick Wolf has paid tribute to Kevin Arkadie, with whom he co-created landmark cop drama Composed York Undercover. Arkadie died this week on the age of 68. Wolf, the particular person within the support of Regulation & Expose and the Chicago and FBI franchises, labored with Arkadie on the screen that ran on […]

Dec
Indiana Man Accused of Killing 81-365 days-Frail Dad, Severely Injuring Mother
Cybersecurity expert An Indiana man has been accused of killing his 81-yr-outdated father and making an are attempting to raze his mom. Indianapolis Police spoke back to the residence of John and Olanna Pedigo slack final week and came upon John Pedigo uninteresting and Olanna with serious accidents, WISH reported. The investigation started when the […]

Dec
Reserve Cop, Bus Driver Charged With Abuse of seven Young of us
Cybersecurity expert A reserve police officer and his valuable other had been arrested and charged with subjecting their natural and foster younger of us to “merciless and uncommon punishment.” Branch County prosecutors Zachary W. Stempien talked about that Matthew and Cassandra Boatrite, 34 and 32, had been charged after a joint investigation by Michigan Youngster […]

Dec
Justice Department appeals desire’s dismissal of indictments in opposition to James Comey and Letitia James
Internet investigation WASHINGTON — The Justice Department is appealing a federal desire’s rulings that tossed out criminal prices in opposition to extinct FBI Director James Comey and New York Attorney Odd Letitia James. The need brushed off the indictments on Nov. 24 after figuring out that Trump loyalist and first-time prosecutor Lindsey Halligan used to […]

Dec
DOJ begins releasing documents tied to Epstein sex trafficking investigation
Private investigator The Justice Division has begun releasing records tied to Jeffrey Epstein, with officers announcing loads of hundreds more recordsdata are expected within the arrival weeks. (12/19/25…Read More
Recent Jersey spiritual activists call for investigation after ICE detainee’s death
Data breach NEWARK, N.J. (RNS) — The death of Jean Wilson Brutus marks the principle recorded death at Delaney Corridor — the supreme immigrant detention facility on the East Fly — since its reopening in May perhaps perhaps perhaps honest. The put up Recent Jersey spiritual activists call for investigation after ICE detainee’s death seemed […]
Recent Posts
- Prince William Allegedly Vows To Finish ‘Particular Safety’ For Andrew, ‘Secrets’ Ought to In some plan Be Unearthed
- Five Accepted App Vulnerabilities That Security Strategies Can Do away with
- Jimmy Kimmel Quips Hollywood ‘Barely Survived the Writers’ Strike’ After FBI Warns of Iran Risk | Video
- Aleksib doesn’t pull off tax evasion strat effectively, likely going by penalties in court
- BOMBSHELL: Trump Accuser Obtained Payoff from Epstein Estate, Says Dem Lawmaker…


