
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Tag: malware

Apr
Security businesses tell Chinese hackers the usage of hijacked networks for gigantic-scale cyberattacks
Cybersecurity expert A model of this memoir regarded in the on each day basis Threat Assign of residing newsletter from The Washington Times. Click right here to acquire Threat Assign of residing delivered at as soon as to your inbox every weekday. Chinese hacking groups linked to gigantic-scale cyberattacks and intrusions of primary infrastructure are […]

Apr
Thousands of shady commercials promote paper authorship for money, trim-scale investigation finds
Private detective Outcomes are “only the tip of the iceberg” of sad paper-mill market…Read Extra

Apr
Hackers exploit file upload trojan horse in Bound Cache WordPress plugin
Private detective Hackers are actively exploiting a severe vulnerability within the Bound Cache plugin for WordPress that lets in importing arbitrary details on the server with out authentication. The safety arena is tracked as CVE-2026-3844 and has been leveraged in higher than 170 exploitation attempts by the Wordfence security solution for the WordPress ecosystem. The […]

Apr
Condo Oversight chair says some participants toughen a Ghislaine Maxwell pardon
Identity theft WASHINGTON — The Republican chair of the Condo Oversight Committee acknowledged some participants would toughen a presidential pardon for convicted sex trafficker Ghislaine Maxwell in alternate for her assistance in the committee’s investigation into Jeffrey Epstein. But unbiased appropriate unbiased appropriate fortune getting any of them to admit it. Earn. James Comer (R-Ky.) told Politico […]
Apr
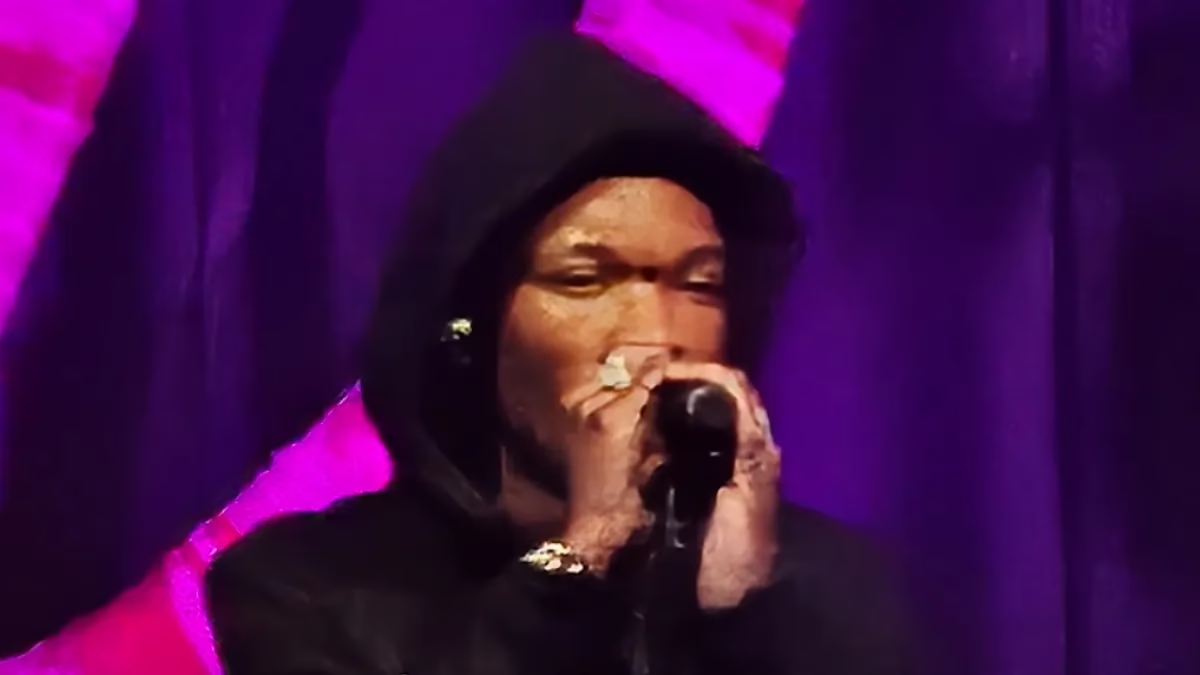
Laufey, Damiano David, Kali Uchis Pull D4vd Collabs as Autopsy and Lurid Investigation Predominant components Emerge
OSINT Photo Credit: D4vd by AskeeaeWiki / CC by 4.0 OSINT Quite a lot of artists who had collaborations with singer D4vd have pulled their tracks as the autopsy results within the demise of Celeste Rivas Hernandez emerge. D4vd’s solo tracks and hits, on the other hand, stay on streaming platforms love Spotify. Celeste Rivas […]

Apr
FCA Conducts First Coordinated Raids on Illegal P2P Crypto Trading in the UK
Private detective FundedNext Overview 2026: Prop Agency Rules, Payouts & Field Items FundedNext Overview 2026: Prop Agency Rules, Payouts & Field Items FundedNext Overview 2026: Prop Agency Rules, Payouts & Field Items FundedNext Overview 2026: Prop Agency Rules, Payouts & Field Items FundedNext Overview 2026: Prop Agency Rules, Payouts & Field Items FundedNext Overview 2026: […]

Apr
Recent Checkmarx present-chain breach impacts KICS analysis software
Cybercrime Hackers accept as true with compromised Docker photography, VSCode and Start VSX extensions for the Checkmarx KICS analysis software to harvest sensitive data from developer environments. KICS, brief for Preserving Infrastructure as Code Accurate, is a free, open-supply scanner that helps developers title security vulnerabilities in supply code, dependencies, and configuration data. The software […]

Apr
Key Democrat seeks inspector overall probe into FAA chief’s airline inventory divestment
Cybersecurity expert Sen. Maria Cantwell and other lawmakers settle on an investigation into whether or not the agency’s administrator “profited from deliberately violating his ethics settlement.”…Learn More

Apr
Chinese hackers the utilization of compromised networks to survey on Western companies, says 5 Eyes
Digital forensics Digital forensics Companies informed to preserve shut countermeasures as Chinese hacking teams exhaust networks of contaminated home and office devices ‘at scale’ to evade security monitoring systems By Bill Goodwin, Investigations Editor Revealed: 23 Apr 2026 12:15 China-linked hackers are the utilization of networks of inclined cyber net-linked devices, in conjunction with home […]

Apr
Apple rolls out iOS 26.4.2 to repair a flaw that allowed the FBI to access push notifications
Internet investigation Apple’s latest iOS replace fixes a flaw in its notification database that made it capability for legislation enforcement to ogle deleted push notifications on a particular person’s iPhone or iPad. The security flaw used to be a technique legislation enforcement businesses accumulate the FBI might perchance well possibly circumvent Apple’s strict stance towards […]
Recent Posts
- FBI Probes Theft of 15 Drones in NJ, Which Could maybe well Be Former in Chemical or Natural Weapon Assaults
- Roommate charged in deaths of two USF students
- Chicago sanatorium shooting leaves 2 officers injured, 1 seriously; suspect in custody: file
- Kevin Warsh’s Fed chair nomination advances as Powell investigation ends
- DoJ Drops Investigation of Fed Chair Powell
Recent Comments
Categories
Recent Posts



