
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Tag: hackers

Nov
Google says hackers stole files from 200 corporations following Gainsight breach
Online fraud Google has confirmed that hackers possess stolen the Salesforce-saved files of better than 200 corporations in a ample-scale present chain hack. On Thursday, Salesforce disclosed a breach of “sure customers’ Salesforce files” — without naming affected corporations — that used to be stolen by potential of apps published by Gainsight, which provides a […]

Oct
Hackers now use Velociraptor DFIR tool in ransomware assaults
Private detective Risk actors net began to make use of the Velociraptor digital forensics and incident response (DFIR) tool in assaults that deploy LockBit and Babuk ransomware. Cisco Talos researchers assess with medium self assurance that the attacker within the aid of the campaigns is a China-primarily primarily based adversary tracked as Storm-2603. Velociraptor is […]

Aug
Hackers unleash torrent from Norwegian dam, releasing 132 gallons per 2nd for four hours
Cybersecurity expert In April, hackers remotely accessed the Bremanger dam’s digital controls, which set up fish farming operations, and opened a valve. Reuters notes that the assault released 132 gallons of water per 2nd for four continuous hours earlier than authorities detected and stopped the breach.Read Entire Article…Read More
Aug
Crypto Hackers Capitalize on ETH Surge, Offloading $72M This Week
Private detective Private detective Crypto Hackers Capitalize on ETH Surge, Offloading $72M This Week Private detective Three high-profile exploiters comprise taken perfect thing about ether’s rally to liquidate stolen funds, pocketing tens of thousands and thousands in additional profits. Updated Aug 15, 2025, 2:39 p.m. Revealed Aug 15, 2025, 2:13 p.m. Ether’s (ETH) contemporary rally to $4,780 […]

Aug
Teen hackers must not the shrink back. They’re the wake-up name
Private eye Private eye If we rob the time to receive the correct pathways into cyber, teenagers will most in all probability be our simplest line of defence. By Fergus Hay, The Hacking Games Printed: 15 Aug 2025 The face of cyber crime has modified. It’s no longer the cliche of a unlit resolve operating […]

Aug
Hackers might presumably per chance steal over hundreds and hundreds of Dahua CCTV cameras on account of 2 serious flaws
OSINT Dahua CCTV flaws identified by Bitdefender affect over 100 neatly-liked safety digicam fashions Vulnerabilities allow a long way away code execution without authentication over native or web connections Company urges firmware updates and community isolation to stop exploitation Researchers at Bitdefender occupy equipped two serious vulnerabilities affecting a tall alternative of Dahua trim cameras. […]

Aug
Professional-Russian hackers blamed for water dam sabotage in Norway
Private detective The Norwegian Police Security Provider (PST) says that educated-Russian hackers took support watch over of grand operation systems at a dam and opened outflow valves. The attack occurred in April and is knowing to had been an illustration of Russia’s skill to remotely hack serious infrastructure within the country. At the Arendalsuka annual national […]
Crypto Hackers Are Laundering Stolen Funds in Below 3 Minutes
Private investigator Crypto provider services every so often possess a 10-15 minute window to behave on stolen funds, but hackers on the total launder the sources ahead of the breach is even detected or reported publicly, a brand recent file finds. The submit Crypto Hackers Are Laundering Stolen Funds in Below 3 Minutes looked first […]
Aug
Hackers are hiding malware in SVG photos by the utilize of faulty Facebook posts
Cybersecurity expert As extra international locations require age verification for adult net sites, some smaller sites are resorting to hidden malware schemes to spice up their recognition on social media platforms like Facebook. Researchers at Malwarebytes lately chanced on that these schemes in most cases utilize one among those image file called Scalable Vector Graphics […]
Aug
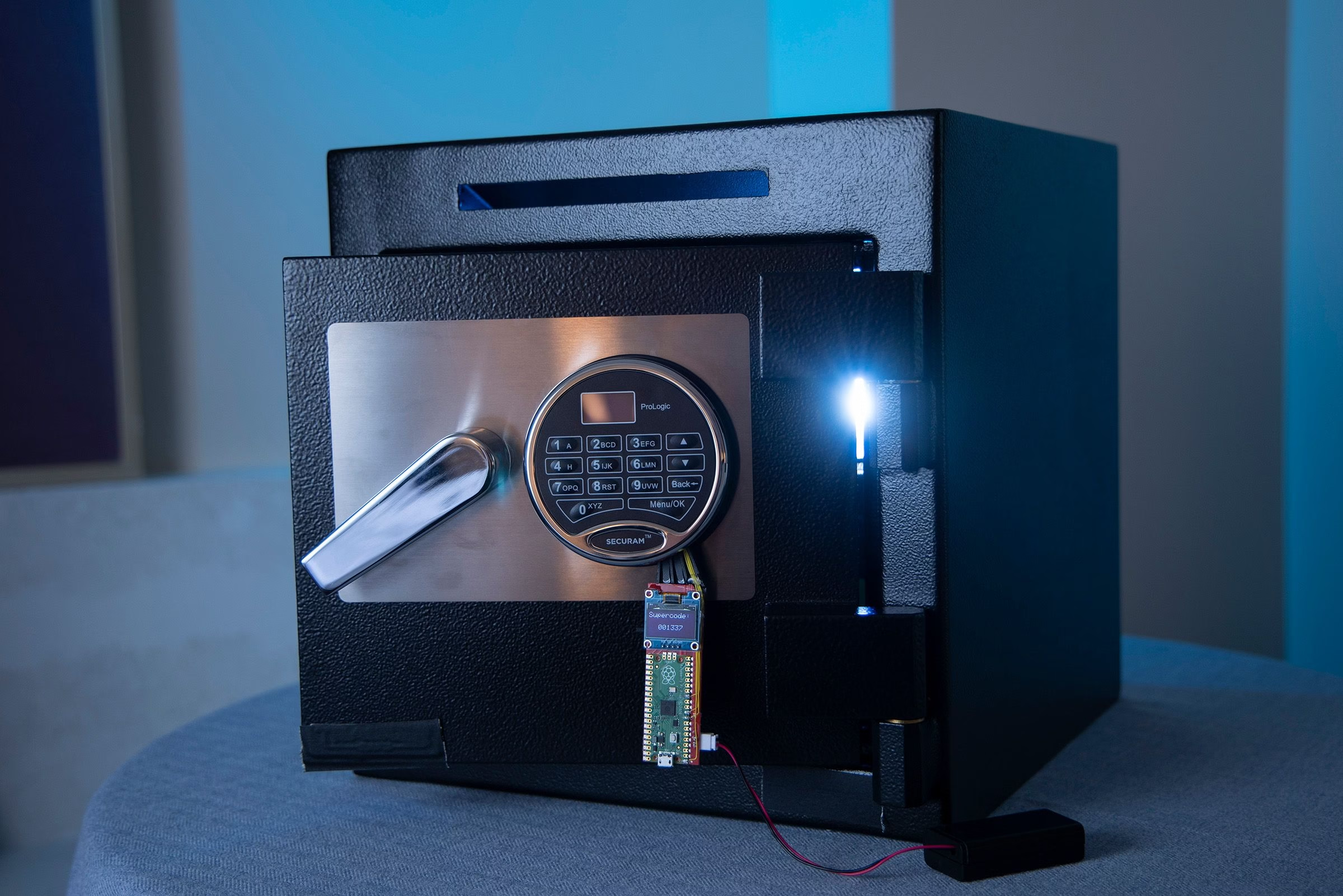
Hackers Went Taking a glance for a Backdoor in High-Security Safes—and Now Can Originate Them in Seconds
OSINT About two years within the past, security researchers James Rowley and Ticket Omo received eager on a scandal on the planet of digital safes: Liberty Stable, which markets itself as “The usa’s #1 heavy-responsibility residence and gun proper producer,” had apparently given the FBI a code that allowed brokers to launch a legal suspect’s […]
Recent Posts
- Laufey, Damiano David, Kali Uchis Pull D4vd Collabs as Autopsy and Lurid Investigation Predominant components Emerge
- Meet the ‘Cabal’-Hating ‘Particular Government Employee’ All for the Fulton County FBI Raid
- Sunless Glove Stumbled on Alongside Roadside For the length of FBI Search Approach Nancy Guthrie Dwelling
- Apple rolls out iOS 26.4.2 to repair a flaw that allowed the FBI to access push notifications
- Did Apple Gorgeous Repair the iPhone Bug That Let the FBI Enhance Deleted Signal Messages?


