
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
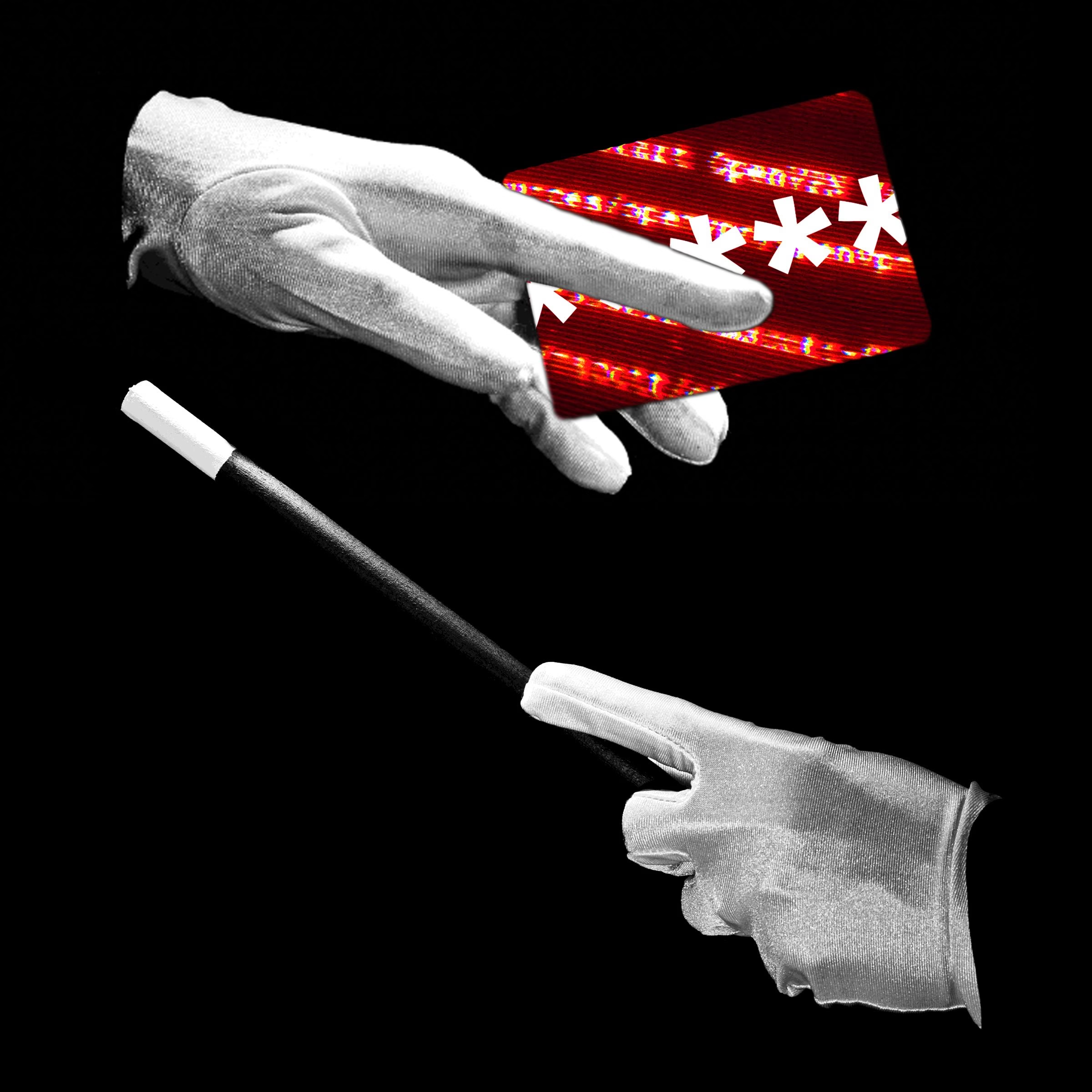
Tag: cybersecurity
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity

Apr
Hackers are turning home routers into instruments to see on Microsoft 365 customers
Cyber investigation A infamous personnel of Russian spies is once more focusing on data superhighway-facing devices to come their unlawful actions. Microsoft warned that Forest Blizzard, a Kremlin-sponsored hacking neighborhood moreover known as Storm-2754 or Esteem Endure, has spent the previous few months attempting to compromise hundreds of non-public and little diagram of work / […]

Apr
Natty Slider updates hijacked to push malicious WordPress, Joomla versions
Cybercrime Hackers hijacked the replace system for the Natty Slider 3 Pro plugin for WordPress and Joomla, and pushed a malicious version with quite lots of backdoors. The developer says that handiest the Pro version 3.5.1.35 of the plugin is affected and recommends switching straight to the most smartly-liked version, currently 3.5.1.36, or 3.5.1.34 and earlier. Apart […]

Apr
FBI: Individuals lost a file $21 billion to cybercrime closing 365 days
Private detective U.S. victims lost close to $21 billion to cyber-enabled crimes closing 365 days, pushed primarily by investment scams, industrial electronic mail compromise, tech toughen fraud, and files breaches, the Federal Bureau of Investigation says. The figure continues the 365 days-over-365 days file building as it is up 26% in comparison to 2024, when Individuals […]

Apr
US warns of Iranian hackers focused on severe infrastructure
Online fraud Iranian-linked hackers are focused on Web-exposed Rockwell/Allen-Bradley programmable logic controllers (PLCs) on the networks of U.S. severe infrastructure organizations. The warning came earlier as of late within the acquire of a joint advisory authored by the FBI, CISA, NSA, the Environmental Protection Agency (EPA), Division of Energy (DOE), and the US Cyber Whine […]

Apr
Max severity Flowise RCE vulnerability now exploited in attacks
Private detective Hackers are exploiting a most-severity vulnerability, tracked as CVE-2025-59528, in the begin-source platform Flowise for constructing custom LLM apps and agentic techniques to realize arbitrary code. The flaw permits injecting JavaScript code without any security assessments and modified into publicly disclosed closing September, with the warning that a success exploitation outcomes in present […]

Apr
Russian defense force hackers reroute British internet users’ visitors
Private investigator For support please consult with support.toes.com. We apologise for any disaster. The following data can support our toughen team to solve this misfortune. Motive Suppose of affairs Build a question to ID 9e8fcfce2f783a6b Location Code 403 Be taught More

Apr
‘The most powerful weapon isn’t very any longer repeatedly a missile’: How Iranian “Charming Kitten” hackers broken-down conventional Frigid Battle recommendations to perceive tech secrets and tactics and plant malware on Apple and Windows users
OSINT Charming Kitten depends on deception as opposed to exploiting technical machine vulnerabilities Unfounded identities plot believe earlier than phishing assaults compromise finest user credentials Operations lengthen at some stage in Apple and Microsoft platforms, affecting diverse users globally Iran-linked cyber operations are drawing renewed consideration for relying much less on evolved code and additional […]

Apr
Hackers exploit React2Shell in automatic credential theft advertising and marketing and marketing campaign
Cybersecurity expert Hackers are running a sexy-scale advertising and marketing and marketing campaign to take credentials in an automatic come after exploiting React2Shell (CVE-2025-55182) in inclined Subsequent.js apps. No longer no longer as a lot as 766 hosts all over a few cloud suppliers and geographies were compromised to accumulate database and AWS credentials, SSH non-public […]
Apr
Hackers Are Posting the Claude Code Leak With Bonus Malware
Private detective A WIRED investigation per Division of Design of birth Security records this week printed the identities of paramilitary Border Patrol brokers who frequently used power against civilians precise by Operation Midway Blitz in Chicago closing fall. Several of the brokers, WIRED figured out, seemed in the same operations in diversified states across the […]

Apr
Evolution of Ransomware: Multi-Extortion Ransomware Attacks
Internet investigation Internet investigation Ransomware’s Real-World Impression Throughout Industries In February 2026, the College of Mississippi Scientific Heart (UMMC) fell victim to a ransomware attack. The incident took the Story digital neatly being file machine offline across 35 clinics and further than 200 telehealth web sites, forcing the cancellation of chemotherapy appointments and the postponement […]
Recent Posts
- Lawmakers name for federal investigation into gambling dysfunction
- James Comey: ‘Justice Can’t Be a Political Force’
- AI Is Handing Hackers Instruments That Once Belonged to Elite Attackers
- Of us Energy Rep collectively protests pollscarcity at Seoul polling stations
- Disabled ACR to your TV? I prepare a router-primarily based VPN for extra protection


