- Ledger’s Donjon crew exploited MediaTek phones, convalescing PINs and crypto pockets seed phrases
- Attackers can extract root cryptographic keys from switched-off Android devices via USB
- Trustonic’s Depended on Execution Ambiance fails to forestall assaults on one-quarter of Android devices
Ledger’s white-hat hacking crew,
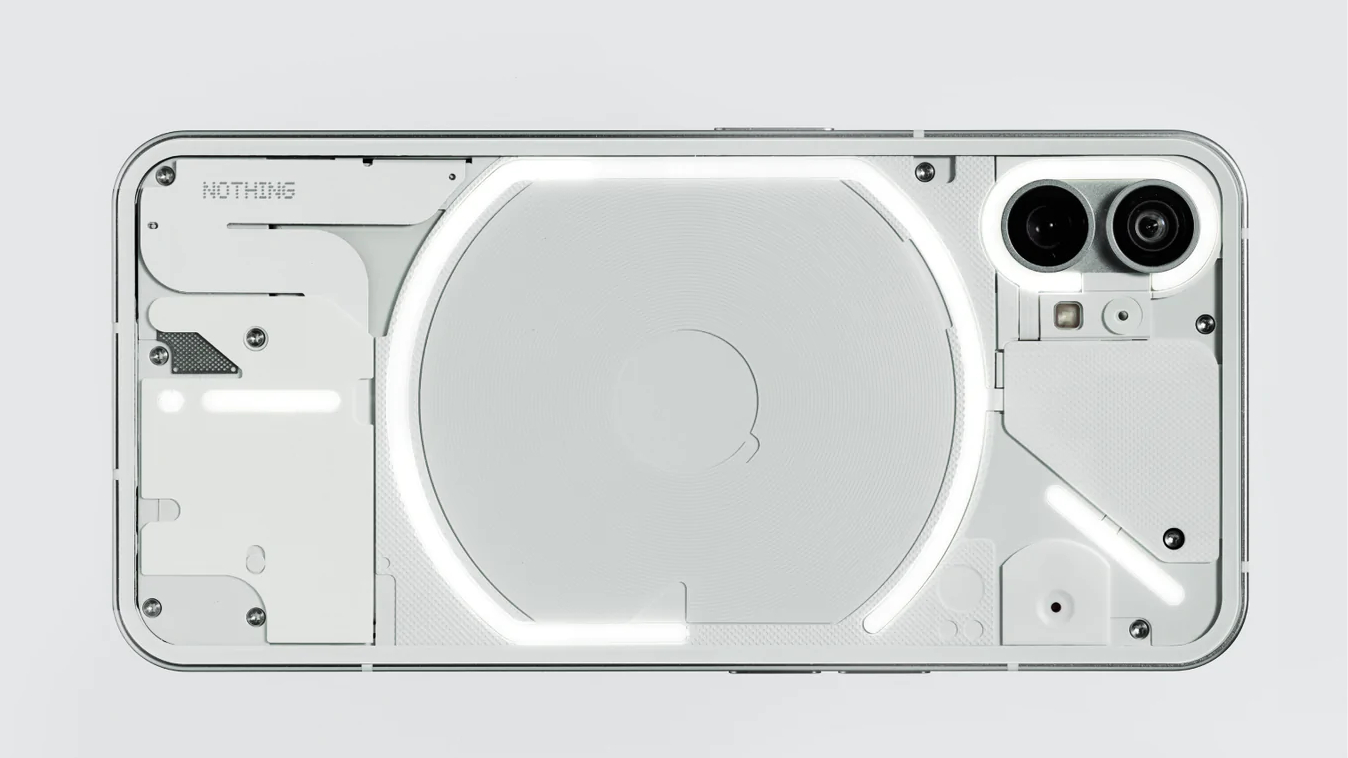
The use of a Nothing CMF Cell phone 1, the Donjon bypassed the Android
The flaw affects devices the utilization of Trustonic’s Depended on Execution Ambiance alongside MediaTek processors, chanced on in roughly one in four
Article continues below
Attackers can connect a powered-down cellular phone through USB and retrieve root cryptographic keys sooner than the operating plan loads.
As soon as got, these keys allow offline decryption of storage and brute-forcing of the software PIN, exposing software files, in conjunction with messages, photos, and pockets files.
Zero-click on assaults brand that Android
“This compare proves what we’ve prolonged warned: smartphones were never designed to be vaults. Whereas this may maybe be patched, and we assist all customers to update with essentially the latest security fixes,” talked about Charles Guillemet, Chief Skills Officer of Ledger.
“In case your crypto sits on a cellular phone, it’s easiest as exact as the weakest link in that cellular phone’s hardware, firmware, or software.”
The Donjon crew conducts frequent audits of Ledger’s devices and third-find collectively hardware, responsibly disclosing vulnerabilities to permit producers to recount fixes sooner than exploitation happens.
Ledger disclosed this vulnerability to MediaTek and Trustonic below the regular 90-day disclosure job, offering time for security patches to realize affected OEMs.
MediaTek confirmed it delivered updates to OEMs on January 5, 2026, and the vulnerability changed into publicly disclosed on March 2, 2026, as CVE-2025-20435.
Users must calm straight away install security updates to mitigate skill assaults, as firmware capable of being upgraded remains valuable for patching zero-day exploits successfully.
This exploit finds the dangers inherent in counting on cellular devices to retailer private files, in conjunction with crypto wallets and varied beautiful files.
All files saved on Android smartphones remains inclined to hardware-basically based mostly assaults, emphasizing that instantaneous patching is in actual fact the most efficient helpful protection against developed threats.
Users must be aware that even up-to-the-minute
Pleasing business or personal files must calm no longer be regarded as exact on cellular phones, and reliance on these devices on my own for storing resources is inherently abominable.
And naturally you may maybe maybe well maybe furthermore furthermore