
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity > Microsoft: Hackers abusing AI at every stage of cyberattacks

Mar
Microsoft: Hackers abusing AI at every stage of cyberattacks
Data breach

Microsoft says chance actors are extra and extra the exhaust of artificial intelligence in their operations to ride assaults, scale malicious project, and decrease technical barriers trusty through all elements of a cyberattack.
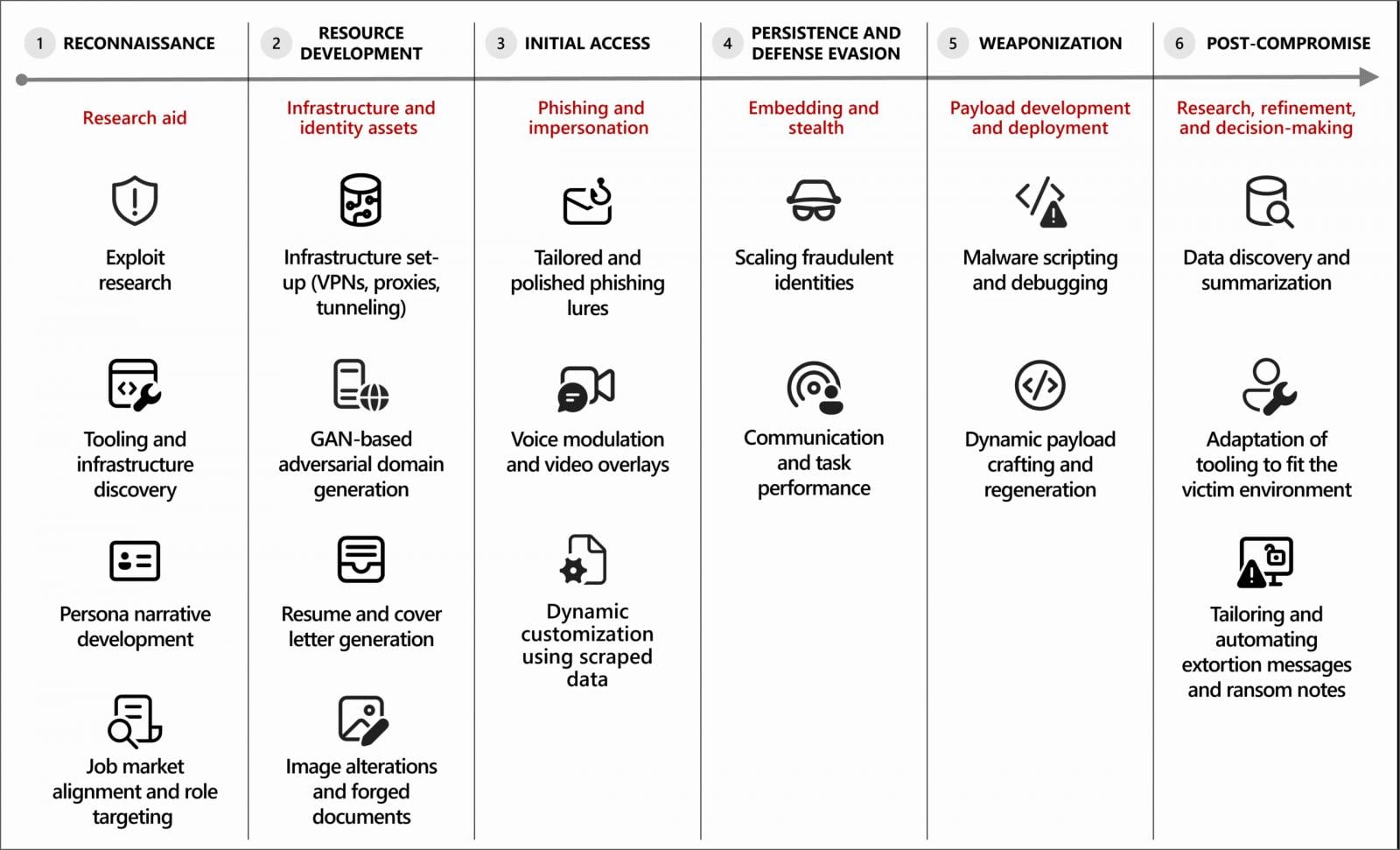
In maintaining with a novel Microsoft Probability Intelligence file, attackers are the exhaust of generative AI tools for a mountainous sequence of responsibilities, alongside side reconnaissance, phishing, infrastructure pattern, malware introduction, and put up-compromise project.
In a variety of instances, AI is veteran to draft phishing emails, translate teach material, summarize stolen files, debug malware, and support with scripting or infrastructure configuration.
“Microsoft Threat Intelligence has observed that most malicious use of AI today centers on using language models for producing text, code, or media. Threat actors use generative AI to draft phishing lures, translate content, summarize stolen data, generate or debug malware, and scaffold scripts or infrastructure,” warns Microsoft.
“For these uses, AI functions as a force multiplier that reduces technical friction and accelerates execution, while human operators retain control over objectives, targeting, and deployment decisions.”
Offer: Microsoft
Data breach AI veteran to energy cyberattacks
Microsoft has observed a pair of chance groups incorporating AI into their cyberattacks, alongside side North Korean actors tracked as Jasper Sleet (Storm-0287) and Coral Sleet (Storm-1877), who exhaust the abilities as section of far off IT worker schemes.
In these operations, AI tools assist generate reasonable identities, resumes, and communications to fabricate employment at Western companies and defend win admission to once hired.
Jasper Sleet leverages generative AI platforms to streamline the enchancment of fraudulent digital personas. To illustrate, Jasper Sleet actors be pleased led to AI platforms to generate culturally acceptable establish lists and email address codecs to confirm explicit identification profiles. To illustrate, chance actors may maybe presumably exhaust the following kinds of prompts to leverage AI on this standing:
Instance suggested 1: “Manufacture an inventory of 100 Greek names.”
Instance suggested 2: “Manufacture an inventory of email address codecs the exhaust of the establish Jane Doe.“
Jasper Sleet also uses generative AI to evaluate job postings for instrument pattern and IT-connected roles on legitimate platforms, prompting the tools to extract and summarize required abilities. These outputs are then veteran to tailor spurious identities to explicit roles.
❖ Microsoft Probability Intelligence
The file also describes how AI is being veteran to support with malware pattern and infrastructure introduction, with chance actors the exhaust of AI coding tools to generate and refine malicious code, troubleshoot errors, or port malware parts to moderately about a programming languages.
Some malware experiments show cloak signs of AI-enabled malware that dynamically generate scripts or modify habits at runtime.
Microsoft also observed Coral Sleet the exhaust of AI to fleet generate spurious company sites, provision infrastructure, and check and troubleshoot their deployments.
When AI safeguards strive to end the exhaust of AI in these responsibilities, Microsoft says chance actors are the exhaust of jailbreaking ways to trick LLMs into generating malicious code or teach material.
As well to to generative AI exhaust, Microsoft researchers be pleased begun to acknowledge chance actors experiment with agentic AI to form responsibilities autonomously and adapt to results.
On the other hand, Microsoft says AI is at show cloak veteran primarily for decision-making rather then for self reliant assaults.
Because many IT worker campaigns depend on the abuse of legitimate win admission to, Microsoft advises organizations to house these schemes and same project as insider dangers.
Furthermore, as these AI-powered assaults mirror outdated cyberattacks, defenders need to level of curiosity on detecting extraordinary credential exhaust, hardening identification programs in opposition to phishing, and securing AI programs that also can turn out to be targets in future assaults.
Microsoft is now not alone in seeing chance actors extra and extra the exhaust of artificial intelligence to energy assaults and decrease barriers to entry.
Google now not too long ago reported that chance actors are abusing Gemini AI trusty through all phases of cyberattacks, mirroring what Amazon observed on this marketing and marketing campaign.
Amazon and the Cyber and Ramen safety weblog also now not too long ago reported on a chance actor the exhaust of a pair of generative AI providers and products as section of a marketing and marketing campaign that breached extra than 600 FortiGate firewalls.
Data breach Pink Anecdote 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Pink Anecdote 2026 shows how novel threats exhaust math to detect sandboxes and cloak in insensible look.
Download our prognosis of 1.1 million malicious samples to expose the cease 10 ways and recognize if your safety stack is blinded.
Tags
- cybercrime cybercrimephishing-attack cybersecurity email-fraud forensics|digital-forensics hackers Investigation malware Microsoft online-scam private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker
Recent Posts
- Hackers know your social security amount. Here’s be taught how to take care of safe
- 3/8/2026: Focusing on People; Secretary Hegseth
- NTSB member says he used to be fired without explanation by the Trump administration
- Vulnerable Olympic Snowboarder on FBIâs most-wished checklist arrested in Mexico
- Salt Typhoon hackers ‘virtually completely’ in Australia’s predominant infrastructure



