
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Hackers Went Taking a glance for a Backdoor in High-Security Safes—and Now Can Originate Them in Seconds
Aug
Hackers Went Taking a glance for a Backdoor in High-Security Safes—and Now Can Originate Them in Seconds
OSINT
About two years within the past, security researchers James Rowley and Ticket Omo received eager on a
Politics aside, Rowley and Omo were vastly very a lot surprised to study that it become if truth be told easy for legislation enforcement to penetrate a locked metal field—no longer even a internet-connected tool—that nobody however the proprietor must always grasp the code to launch. “How is it doable that there may well be this physical security product, and somebody else has the keys to the dominion?” Omo asks.
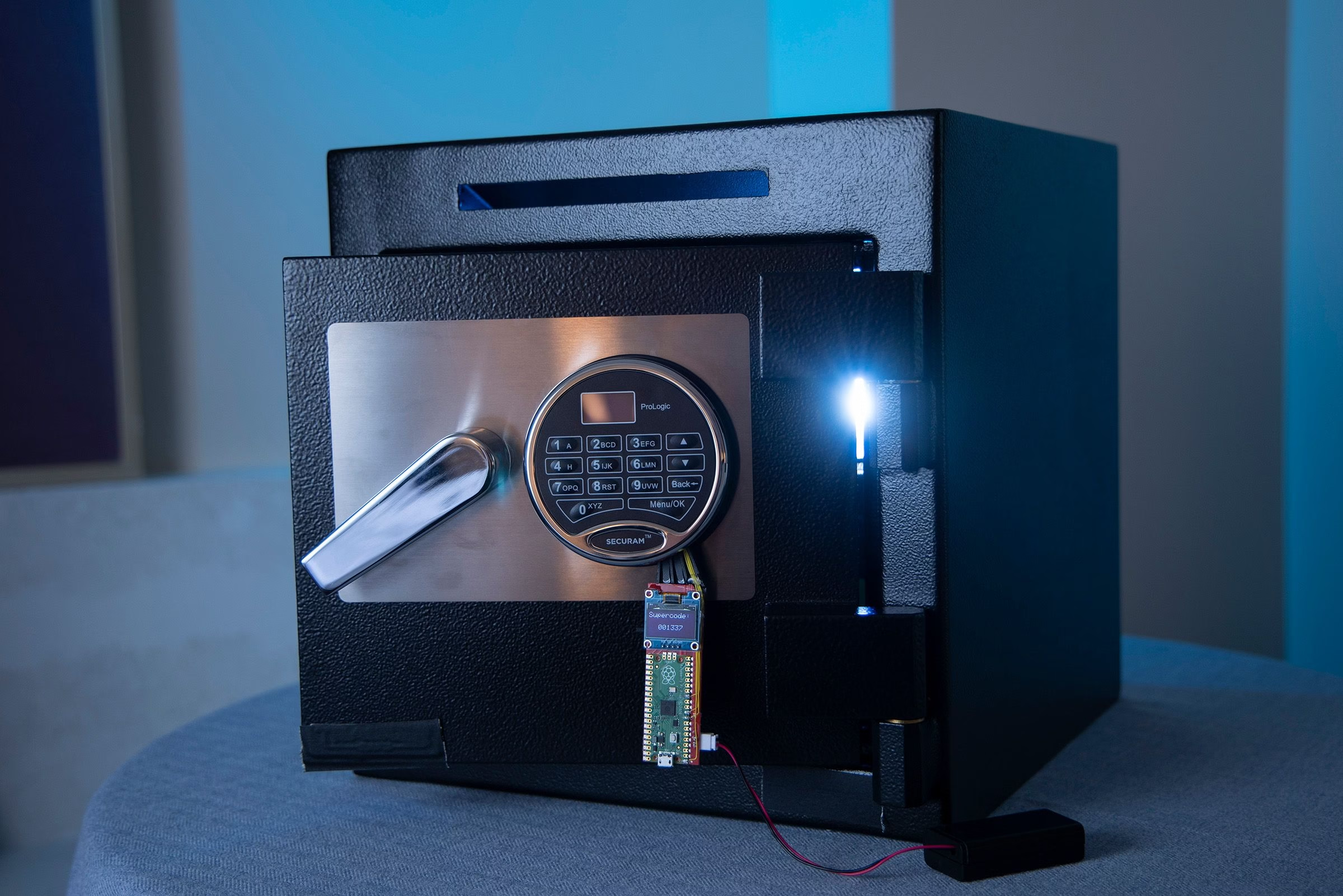
So they decided to take a glance at to resolve out how that backdoor worked. Within the direction of, they’d receive something a ways bigger: one other fabricate of backdoor intended to let licensed locksmiths launch no longer trusty Liberty Stable devices, however the high-security Securam Prologic locks inclined in reasonably a pair of Liberty’s safes and those of as a minimum seven other producers. Extra alarmingly, they stumbled on a approach for a hacker to utilize that backdoor—intended to be accessible completely with the producer’s support—to launch a proper on their very agree with in seconds. Within the middle of their research, additionally they stumbled on one other security vulnerability in many more moderen versions of Securam’s locks that could enable a digital safecracker to insert a tool real into a hidden port within the lock and without delay fabricate a proper’s unlock code.
Security researchers James Rowley and Ticket Omo.Photograph: Ronda Churchill
On the Defcon hacker convention in Las Vegas as of late, Omo and Rowley made their findings public for the first time, demonstrating onstage their two obvious suggestions for opening digital safes supplied with Securam ProLogic locks, which may well be at chance of defend all the pieces from non-public firearms to money in retail stores to narcotics in pharmacies.
Whereas each their suggestions signify obtrusive security vulnerabilities, Omo says it be the individual that exploits a feature intended as a legitimate unlock approach for locksmiths that is the extra current and harmful. “This assault is something where, when you had a proper with this roughly lock, I could well also literally pull up the code fair appropriate now with no specialised hardware, nothing,” Omo says. “All of a surprising, primarily based on our checking out, it appears love folks can receive into virtually any Securam Prologic lock on the planet.”
Omo and Rowley point to each their safecracking suggestions within the two videos under, which prove them performing the suggestions on their very agree with personalized proper with an frequent, unaltered Securam ProLogic lock:
OSINT Security Change? No, Aquire a New Lock
Omo and Rowley state they informed Securam about each their proper-opening suggestions in spring of ultimate year, but grasp until now kept their existence secret thanks to correct threats from the corporate. “We can refer this topic to our counsel for alternate libel when you to settle on the route of public announcement or disclosure,” a Securam representative wrote to the two researchers sooner than final year’s Defcon, where they first deliberate to prove their research.
Handiest after obtaining legitimate bono correct representation from the Digital Frontier Foundation’s Coders’ Rights Mission did the pair settle on to apply thru with their thought to talk about Securam’s vulnerabilities at Defcon. Omo and Rowley state they’re even now being careful now to no longer notify ample technical ingredient to support others replicate their suggestions, while peaceable looking to present a warning to proper homeowners about two diverse vulnerabilities that exist in reasonably a pair of their devices.
When WIRED reached out to Securam for comment, the corporate’s CEO, Chunlei Zhou, spoke back in a commentary. “The explicit ‘vulnerabilities’ alleged by Omo and Rowley are already properly identified to industry experts and if truth be told, also grasp an affect on other proper lock companies that utilize the same chips,” Zhou writes. “Delivering any assault primarily based on these vulnerabilities does require specialised files, talents, and tools, and we spoil no longer grasp any file of any buyer that has ever had even a single proper lock defeated thru a utilize of this assault.”
Zhou’s commentary goes on to tag change routes safes’ locks could well also be opened from drilling and cutting back to the utilize of a locksmith tool known as a
Omo and Rowley acknowledge that the vulnerabilities they stumbled on were no longer previously identified to the public; one among the two doesn’t require any special tools, despite Zhou’s claim; and none of the opposite suggestions Zhou mentions represents as critical a security flaw as their findings referring to the Securam ProLogic locks. The brute-power safecracking suggestions Zhou sides to, love cutting back and drilling are a ways slower and much less stealthy—or, love the Miniature Unlit Box, are on hand completely to locksmiths and haven’t been publicly confirmed to be exploitable by unauthorized hackers.
Zhou added in his commentary that Securam will likely be fixing the vulnerabilities Omo and Rowley stumbled on in future fashions of the ProLogic lock. “Customer security is our precedence and we grasp begun the direction of of building next-generation merchandise to thwart these doable assaults,” he writes. “We request to grasp new locks available on the market by the discontinue of the year.”
Photograph: Ronda Churchill
In a followup call, Securam director of gross sales Jeremy Brookes confirmed that Securam has no thought to fix the vulnerability in locks already in utilize on possibilities’ safes, but suggests proper homeowners who’ve an interest aquire a new lock and change the one on their proper. “We’re no longer going to present a firmware package that upgrades it,” Brookes says. “We’re going to present them a new product.”
Brookes provides that he believes Omo and Rowley are “singling out” Securam with the scheme of “discrediting” the corporate.
Omo responds that’s under no circumstances their intent. “We’re looking to provide the public responsive to the vulnerabilities in one among the most standard proper locks available on the market,” he says.
OSINT A Senator’s Warning
Beyond Liberty Stable, Securam ProLogic locks are inclined by a giant number of proper producers including Fortress Knox, High Noble, FireKing, Tracker, ProSteel, Rhino Metals, Solar Welding, Corporate Stable Specialists, and pharmacy proper companies Cennox and NarcSafe, fixed with Omo and Rowley’s research. The locks can even be stumbled on on safes inclined by CVS for storing narcotics and by multiple US restaurant chains for storing money.
Rowley and Omo are likely to be no longer the first to take concerns referring to the security of Securam locks. In March of ultimate year, US senator Ron Wyden wrote an launch letter to Michael Casey, then director of the Nationwide Counterintelligence and Security Heart, urging Casey to provide clear to American companies that proper locks made by Securam, which is owned by a Chinese parent company, grasp a producer reset functionality. That functionality, Wyden wrote, could well also be inclined as a backdoor—a chance that had already ended in Securam locks being prohibited for US government utilize love all other locks with a producer reset, even as they’re broadly inclined by internal most US companies.
In keeping with studying about Rowley and Omo’s research, Wyden wrote in a commentary to WIRED that the researchers’ findings signify exactly the chance of a backdoor—whether in safes or in encryption tool—that he’s tried to call attention to.
“Specialists grasp warned for years that backdoors will likely be exploited by our adversaries, yet as an change of acting on my warnings and those of security experts, the government has left the American public inclined,” Wyden writes. “Here is exactly why Congress must reject calls for tag new backdoors in encryption technology and fight all efforts by other governments,
OSINT ResetHeist
Rowley and Omo’s research began with that same downside, that a largely undisclosed unlocking approach in safes could well also signify a broader security chance. They before all the pieces went browsing for the mechanism within the support of the Liberty Stable backdoor that had precipitated a backlash in opposition to the corporate in 2023, and stumbled on a slightly easy acknowledge: Liberty Stable retains a reset code for every proper and, in some conditions, makes it on hand to US legislation enforcement.
Liberty Stable has since
Rowley and Omo deliberate to provide an rationalization for the existence of Securam’s vulnerabilities bigger than a year within the past, but held off until now due to the the corporate’s correct threats.Photograph: Ronda Churchill
Rowley and Omo did no longer receive any security flaw that could enable them to abuse that yelp legislation-enforcement-pleasant backdoor. When they began inspecting the Securam ProLogic lock, on the opposite hand, their research on the upper-discontinue model of the two kinds of Securam lock inclined on Liberty Stable merchandise revealed something extra attractive. The locks grasp a reset approach documented in their manual, intended in theory for utilize by locksmiths serving to proper homeowners who grasp forgotten their unlock code.
Enter a “restoration code” into the lock—grunt to “999999” by default—and it makes utilize of that payment, one other number kept within the lock known as an encryption code, and a third, random variable to compute a code that’s displayed on the veil. A certified locksmith can then study that code to a Securam representative over the phone, who then makes utilize of that payment and a secret algorithm to compute a reset code the locksmith can enter into the keypad to grunt a new unlock mixture.
Omo and Rowley stumbled on that by examining the Securam ProLogic’s firmware, on the opposite hand, they could well also receive all the pieces they main to compute that reset code themselves. “There may well be no longer any hardware security to talk about of,” says Rowley. “So we could well also reverse engineer the entire secret algorithm trusty by reading the firmware that’s within the lock.” The resulting safecracking approach requires little bigger than punching a pair of numbers real into a Python script they wrote. They call the approach ResetHeist.
The researchers account for that proper homeowners can cease this ResetHeist approach by changing their lock’s restoration code or its encryption code. Nonetheless Securam doesn’t indicate that safeguard in any user documentation the researchers could well also receive on-line, completely in a manual for some producers and locksmiths. In a single other Securam webinar Omo and Rowley stumbled on, Securam notes that you simply would also alternate the codes, but that it’s no longer critical, and that the codes are “usually by no approach” changed. In every lock the researchers tested, including about a handful they supplied inclined from eBay, the codes hadn’t been changed. “Now we grasp no longer supplied a lock on which the restoration approach did no longer work,” Omo says.
OSINT CodeSnatch
The 2nd approach the researchers developed, which they call CodeSnatch, is extra easy. By striking off the battery from a Securam ProLogic lock and inserting a small handheld tool they made with a Raspberry Pi minicomputer into an uncovered debug port internal, they’ll extract a “sizable code” mixture from the lock that’s displayed on their tool’s veil and could well also be at chance of without delay launch the lock.
The researchers stumbled on that CodeSnatch trick by reverse engineering the Renesas chip that serves because the lock’s most predominant processor. That activity become made a ways more uncomplicated by the work of a community known as fail0verflow, which had published their evaluation of the the same Renesas chip as portion of their efforts to crack the PlayStation 4, which also makes utilize of that processor. Omo and Rowley constructed their tool to reprogram the chip’s firmware to dump all of its files via the debug port—including the encrypted “sizable code” and the most critical, also kept on the chip, that decrypts it. “It is if truth be told no longer that anxious,” says Rowley. “Our little tool does that, and then it tells you what the sizable code is.”
Gaining receive admission to to the lock’s code via its debug port does require inputting a password. Nonetheless Omo and Rowley state that password become absurdly easy, and so that they efficiently guessed it. They stumbled on that in one more moderen Securam ProLogic lock manufactured in March of this year, Securam had changed the password, but they were ready to study it all once more through the use of a “voltage glitching” approach: By soldering a switch to the voltage regulator on the chip, they could well also mess with its electrical voltage on the actual 2nd it performed the password test to circumvent that test and then dump the chip’s contents—including the brand new password.
Photograph: Ronda Churchill
Apart from Securam, WIRED reached out to 10 proper producers that appear to make utilize of Securam ProLogic locks on their safes, as properly as CVS. Most didn’t acknowledge, but a spokesperson for High Noble Stable Company wrote in a commentary that WIRED’s inquiry become the first it become studying of Securam’s vulnerabilities, and that it’s now reviewing the security of the locks inclined by its product line and preparing steering for possibilities including “extra physical safety features or doable replacement choices.”
A Liberty Stable representative within the same scheme renowned the corporate wasn’t previously responsive to Securam’s vulnerabilities. “We’re for the time being investigating this venture with SecuRam and will spoil whatever it takes to defend our possibilities,” a commentary from the spokesperson reads, “including validating other doable lock suppliers and establishing a new proprietary lock system.”
A CVS spokesperson declined to comment on “explicit security protocols or devices,” but wrote that “the security of our staff and patients is a high precedence and we are committed to declaring the supreme physical security standards.”
OSINT “Safes That Aren’t Stable”
Rowley and Omo state that patching Securam Locks’ security flaws is doable—their very agree with CodeSnatch tool, in actuality, could well also itself be at chance of update the locks’ firmware. Nonetheless any such fix would want to be implemented manually, lock by lock, a gradual and costly direction of.
Even though Omo and Rowley are likely to be no longer releasing the elephantine technical small print or any proof-of-theory code for his or her suggestions, they warn that others with much less benevolent intentions could well also peaceable resolve out the answer to replicate their safecracking suggestions. “Whereas you would also grasp gotten the hardware and also you’re educated within the art, this can be roughly a one-week thing,” Omo says.
He and Rowley decided to mosey public with their research despite that chance to provide proper homeowners conscious that their locked metal boxes will no longer be as proper as they judge. Extra broadly, Omo says that they main to call attention to the wide gaps in US cybersecurity standards for individual merchandise. Securam locks are certified by Underwriters Laboratory, he sides out—yet suffered from critical security flaws that can be tricky to fix. (Underwriters Laboratory did no longer straight acknowledge to WIRED’s ask for comment.)
For the time being, they are saying, proper homeowners need to as a minimum know about their safes’ flaws—and no longer depend on a false sense of security.
“We favor Securam to fix this, but extra importantly we favor folks to take grasp of how harmful this could well also be,” Omo says. “Digital locks grasp electronics internal. And electronics are anxious to proper.”
Recent Posts
- Deliveryman Who Turn into once Detained, Launched in Nancy Guthrie Case Held For five Hours
- From Grace To Crime: Internal Chatunga Mugabe’s R45m Sandhurst Luxury Mansion Where Gardener Became once Shot
- Bluetooth devices with Google Speedily Pair are at risk of recent hack
- Two charged for the usage of wrong USDA labels
- Bithumb Bitcoin Blunder: $1.3B Error Sparks Probe Into Fashioned Monetary Oversight

