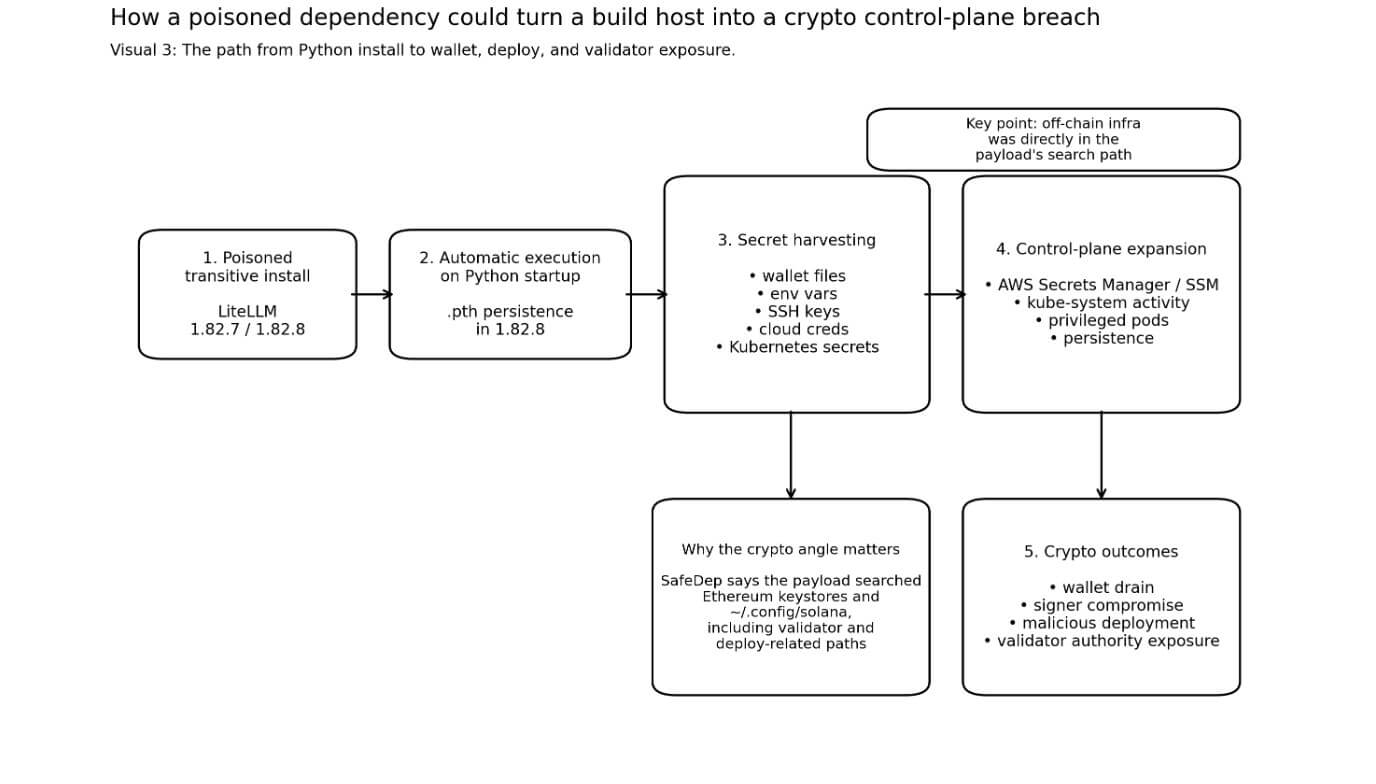
A poisoned release of LiteLLM modified into a routine Python set up real into a crypto-aware secret stealer that searched for wallets, Solana validator field fabric, and cloud credentials at any time when Python started.
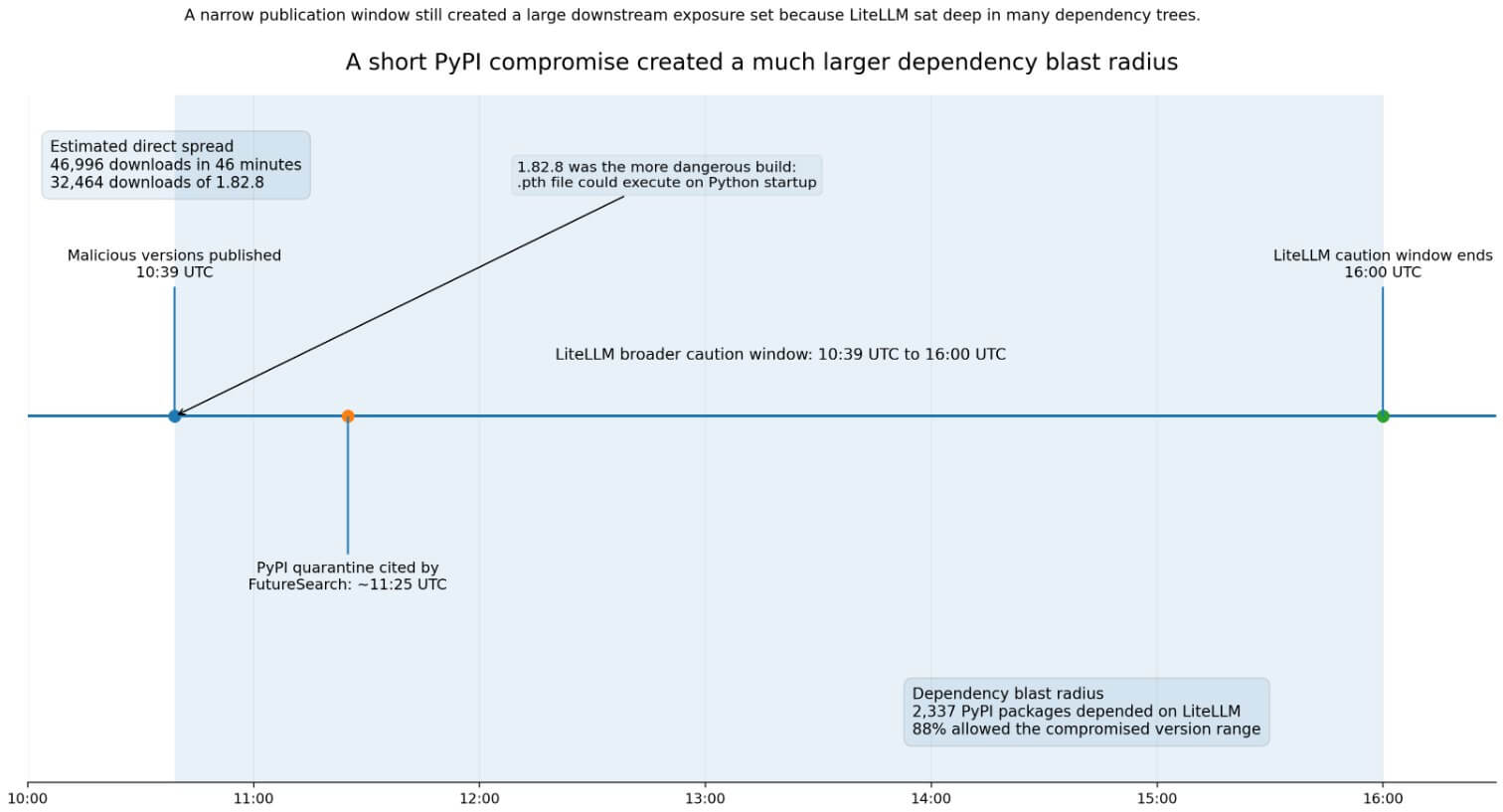
On Mar. 24, between 10:39 UTC and 16:00 UTC, an attacker who had won entry to a maintainer myth revealed two malicious versions of LiteLLM to PyPI: 1.82.7 and 1.82.8.
LiteLLM markets itself as a unified interface to bigger than 100 astronomical language model suppliers, a space that places it interior credential-successfully off developer environments by make. PyPI Stats recordsdata 96,083,740 downloads in the closing month on my own.
The two builds carried varied levels of risk. Model 1.82.7 required a appropriate away import of litellm.proxy to spark off its payload, whereas version 1.82.8 planted a .pth file (litellm_init.pth) in the Python set up.
Python’s hold documentation confirms that executable lines in .pth files bustle at every Python startup, so 1.82.8 executed with none import at all. Any machine that had it save in ran compromised code the moment Python subsequent launched.
FutureSearch estimates 46,996 downloads in 46 minutes, with 1.82.8 accounting for 32,464 of them.
Additionally, it counted 2,337 PyPI packages that depended on LiteLLM, with 88% allowing the compromised version vary on the time of the attack.
LiteLLM’s hold incident page warned that anyone whose dependency tree pulled in LiteLLM by an unpinned transitive constraint all over the window should always smooth address their atmosphere as doubtless uncovered.
The DSPy crew confirmed it had a LiteLLM constraint of “superior or equal to 1.64.0” and warned that unique installs all over the window may perchance well also possess resolved to the poisoned builds.
Cybersecurity expert Constructed to hunt crypto
SafeDep’s reverse engineering of the payload makes the crypto focusing on negate.
The malware searched for Bitcoin wallet configuration files and wallet*.dat files, Ethereum keystore directories, and Solana configuration files below ~/.config/solana.
SafeDep says the collector gave Solana special therapy, showing targeted searches for validator key pairs, vote myth keys, and Anchor deploy directories.
Solana’s developer documentation sets the default CLI keypair course at ~/.config/solana/identification.json. Anza’s validator documentation describes three authority files central to validator operation, and states that theft of the licensed withdrawer provides an attacker entire set up an eye on over validator operations and rewards.
Anza moreover warns that the withdrawal key should always smooth never take a seat on the validator machine itself.
SafeDep says the payload harvested SSH keys, atmosphere variables, cloud credentials, and Kubernetes secrets and tactics all over namespaces. When it stumbled on proper AWS credentials, it queried AWS Secrets and tactics Manager and the SSM Parameter Retailer for added knowledge.
It moreover created privileged node-setup-*pods in kube-scheme and save in persistence by sysmon.py and a systemd unit.
For crypto teams, the compounded risk runs in a negate route. An infostealer that collects a wallet file alongside the passphrase, deploy secret, CI token, or cluster credential from the identical host can convert a credential incident real into a wallet drain, a malicious contract deployment, or a signer compromise.
The malware assembled precisely that combination of artifacts.
wallet*.dat, wallet config files~/.ethereum/keystore~/.config/solana/id.json~/.ssh/*This attack is portion of a mighty wider campaign, as LiteLLM’s incident grunt links the compromise to the earlier Trivy incident, and Datadog and Snyk both listing LiteLLM as a later stage in a multi-day TeamPCP chain that moved by several developer ecosystems earlier to reaching PyPI.
The focusing on good judgment runs consistently all over the campaign: a secret-successfully off infrastructure tooling provides quicker entry to wallet-adjoining field fabric.
Cybersecurity expert Likely outcomes for this episode
The bull case rests on the rate of detection and the absence, to this level, of publicly confirmed crypto theft.
PyPI quarantined both versions by approximately 11:25 UTC on Mar. 24. LiteLLM eliminated the malicious builds, circled maintainer credentials, and engaged Mandiant. PyPI for the time being displays 1.82.6 as essentially the latest visible release.
If defenders circled secrets and tactics, audited for litellm_init.pth, and handled uncovered hosts as burned earlier to adversaries may perchance well also convert exfiltrated artifacts into active exploitation, then the damage stays contained to credential publicity.
The incident moreover quickens the adoption of practices already gaining ground. PyPI’s Relied on Publishing replaces long-lived handbook API tokens with short-lived OIDC-backed identification, approximately 45,000 projects had adopted it by November 2025.
CryptoSlate Day-to-day Brief
Day-to-day alerts, zero noise.
Market-transferring headlines and context delivered every morning in one tight read.
5-minute digest 100k+ readers
Free. No enlighten mail. Unsubscribe any time.
You’re subscribed. Welcome aboard.
LiteLLM’s incident fervent the abuse of release credentials, making it mighty harder to push aside the case for switching.
For crypto teams, the incident creates urgency for tighter goal separation: chilly validator withdrawers saved totally offline, isolated deployment signers, short-lived cloud credentials, and locked dependency graphs.
The DSPy crew’s quick pinning and LiteLLM’s hold put up-incident steering both level in direction of airtight builds because the remediation not unique.
The endure case turns on lumber. SafeDep documented a payload that exfiltrated secrets and tactics, spread interior Kubernetes clusters, and save in persistence earlier to detection. An operator who save in a poisoned dependency interior a function runner or cluster-linked atmosphere on Mar. 24 may perchance well also not seek data from the chubby scope of that publicity for weeks. Exfiltrated API keys, deploy credentials, and wallet files develop not expire on detection. Adversaries can set up them and act later. Sonatype puts malicious availability at “not not as a lot as two hours”; LiteLLM’s hold steering covers installs by 16:00 UTC; and FutureSearch’s quarantine timestamp is 11:25 UTC. Groups can’t depend entirely on timestamp filtering to search out out their publicity, as these figures develop not yield a clear all-sure. Essentially the most lethal grief in this category centers on shared operator environments. A crypto swap, validator operator, bridge crew, or RPC supplier that save in a poisoned transitive dependency interior a function runner would possess uncovered a complete set up an eye on airplane. Kubernetes secret dumps all over namespaces and privileged pod creation in the kube-scheme namespace are set up an eye on-airplane entry instruments designed for lateral circulation. If that lateral circulation reached an atmosphere where sizzling or semi-sizzling validator field fabric was existing on reachable machines, the consequences may perchance well also vary from particular particular person credential theft to compromise of validator authority. PyPI’s quarantine and LiteLLM’s incident response closed the active distribution window. Groups that save in or upgraded LiteLLM on Mar. 24, or that ran builds with unpinned transitive dependencies resolving to 1.82.7 or 1.82.8, should always smooth address their environments as totally compromised. Some actions encompass rotating all secrets and tactics accessible from uncovered machines, auditing for litellm_init.pth, revoking and reissuing cloud credentials, and verifying that no validator authority field fabric was accessible from these hosts. The LiteLLM incident paperwork a course of an attacker who knew precisely which off-chain files to ogle, had a provide mechanism with tens of hundreds of thousands of monthly downloads, and built persistence earlier to anyone pulled the builds from distribution. The off-chain machinery that strikes and safeguards crypto sat straight in the payload’s search course.