
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Hackers fooled Cognizant abet desk, says Clorox in $380M cyberattack lawsuit

Jul
Hackers fooled Cognizant abet desk, says Clorox in $380M cyberattack lawsuit
Cyber investigation

Clorox is suing IT huge Cognizant for inferior negligence, alleging it enabled a huge August 2023 cyberattack by resetting an employee’s password for a hacker without first verifying their identification.
The incident used to be first made public in September 2023, reportedly utilized by hackers connected to Scattered Spider, who utilized a social engineering assault to breach the firm.
The lawsuit says Cognizant supplied IT services to Clorox, alongside side service desk enhance and identification management, which used to be the purpose of compromise that led to a devastating and pricey cyberattack for the firm.
Clorox is a famous user goods firm, most realistic identified for family cleansing products, bleach, disinfectants, and internal most care objects. Cognizant is a world IT services and consulting firm, providing cloud services, system construction, and cybersecurity.
According to the complaint, from 2013 to 2023, Cognizant used to be reduced in measurement by Clorox to address its IT operations.
“Cognizant provided the service desk (“Provider Desk”) that Clorox employees could contact when they needed password recovery or reset assistance,” reads the complaint shared with BleepingComputer.
“Cognizant’s operation of the Service Desk came with a simple, common-sense requirement: never reset anyone’s credentials without properly authenticating them first. Clorox made this easy for Cognizant by providing them with straight-forward procedures to follow whenever providing credential recovery or reset assistance.”
On the opposite hand, the complaint alleges that on August 11, 2023, recordings show veil that a cybercriminal called Cognizant’s Provider Desk just a few times, pretending to be a Clorox representative requesting password and multi-part authentication resets.
“At no point during any of the calls did the Agent verify that the caller was in fact Employee 1. At no point did the Agent follow Clorox’s credential support procedures—either the pre-2023 procedure or the January 2023 update—before changing the password for the cybercriminal. The Agent further reset Employee 1’s MFA credentials multiple times without any identity verification at all. And at no point did the Agent send the required emails to the employee or the employee’s manager to alert them of the password reset. “Clorox claims within the complaint.
This form of social engineering assault has change into the hallmark of Scattered Spider assaults, recently feeble in UK retail assaults on Marks & Spencer and Co-op.
After allegedly failing to take a look at the caller’s accurate identification, Cognizant reset the credentials and multi-part authentication (MFA) for the hacker, granting them entry to Clorox’s IT network.
To sort issues worse, Clorox alleges that the threat actors feeble the similar playbook to reset the password and MFA for one more employee who worked in IT security, which used to be completed without verification all over again. This reportedly gave the attackers privileged entry to the network, which they feeble to spread to extra devices.
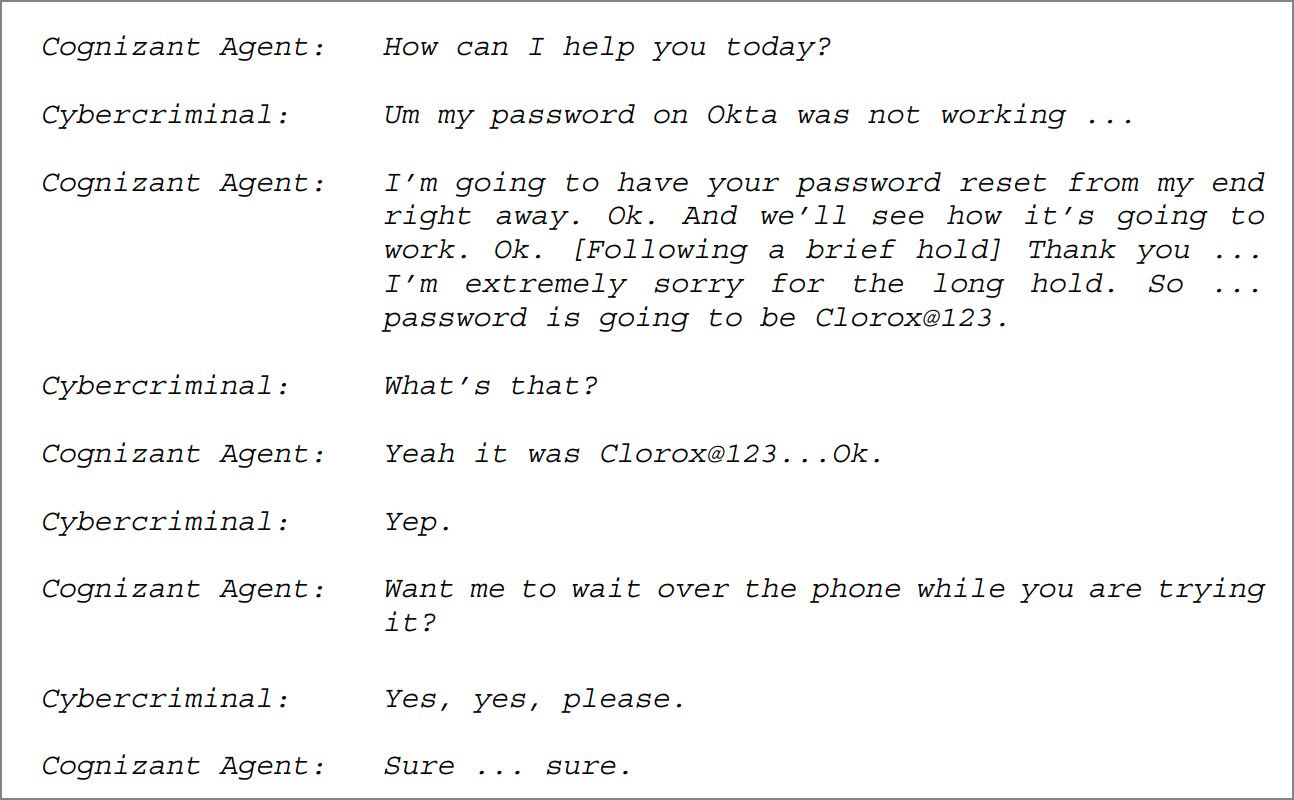
Supply: Clorox complaint against Cognizant
Clorox states that Cognizant’s actions terrified its company network, halted manufacturing, and led to fashioned product shortages and alternate interruption.
To boot to this, Clorox described Cognizant’s response and restoration enhance as overly incompetent, leading to delays within the utility of containment measures, failure to total down compromised accounts, and sending underqualified personnel on premises.
“The resulting Cyberattack was debilitating. It paralyzed Clorox’s corporate network and crippled business operations,” describes the suitable complaint.
“And to make matters worse, when Clorox called on Cognizant to provide incident response and disaster recovery support services, Cognizant botched its response and compounded the damage it had already caused.”
Clorox’s complaint alleges breach of contract due to the Cognizant’s failure to meet ITSA duties, breach of upright faith and comely dealing, inferior negligence, and intentional misrepresentation of workers coaching on the buyer’s credential reset procedures.
For these actions, which resulted in an excellent deal of of millions of dollars in lost gross sales due to the alternate disruption, to boot to reputational fracture with long-time duration consequences, Clorox is trying to search out $49 million in recount remediation damages and $380,000,000 in total damages.
[Update 7/24 03:00 AM EST] – A Cognizant spokesperson sent BleepingComputer the under commentary:
“It is shocking that a corporation the size of Clorox had such an inept internal cybersecurity system to mitigate this attack. Clorox has tried to blame us for these failures, but the reality is that Clorox hired Cognizant for a narrow scope of help desk services which Cognizant reasonably performed. Cognizant did not manage cybersecurity for Clorox.” – Cognizant
Cyber investigation Cloud Detection & Response for Dummies
Own emerging threats in accurate time – sooner than they impact your alternate.
Be taught how cloud detection and response (CDR) gives security groups the edge they want in this just appropriate, no-nonsense manual.
Recent Posts
- Bluetooth devices with Google Speedily Pair are at risk of recent hack
- Broker who supplied malware to the FBI space for sentencing
- High college senior going through extra than 300 prison fees in alleged sextortion map focusing on minors: reports
- 12 Delivery air Energy Tools You Can also objective accrued Appreciate In Your Garage Sooner than Spring Will get Right here
- How the FBI tracked down a Maryland man allegedly in the support of a secret-filming YouTube channel



