-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Hackers exploit Modular DS WordPress plugin flaw for admin procure admission to

Jan
Hackers exploit Modular DS WordPress plugin flaw for admin procure admission to
Mobile forensics

Hackers are actively exploiting a most severity flaw in the Modular DS WordPress plugin that allows them to avoid authentication remotely and procure admission to the vulnerable web pages with admin-level privileges.
The flaw, tracked as CVE-2026-23550, impacts versions 2.5.1 and older of Modular DS, a management plugin that allows managing a number of WordPress web pages from a single interface.
The plugin lets homeowners, builders, or web web residing hosting suppliers remotely video display web pages, invent updates, characteristic up customers, procure admission to server recordsdata, stir repairs duties, and log in. Modular DS has more than 40,000 installations.
In accordance with Patchstack researchers, CVE-2026-23550 is presently exploited in the wild, the first assaults being detected on January 13, around 02:00 UTC.
Patchstack confirmed the flaw and reached out to the supplier on the next day. Modular DS launched a repair in model 2.5.2, handiest a number of hours later.
The vulnerability is caused by a series of assemble and implementation flaws, including accepting requests as trusted when “speak request” mode is activated, with out a cryptographic test of their foundation. This habits exposes a number of soundless routes and prompts an automatic admin login fallback mechanism.
If no particular person ID is available in the request body, the plugin fetches an fresh admin or mammoth admin person, then logs in as that person automatically.
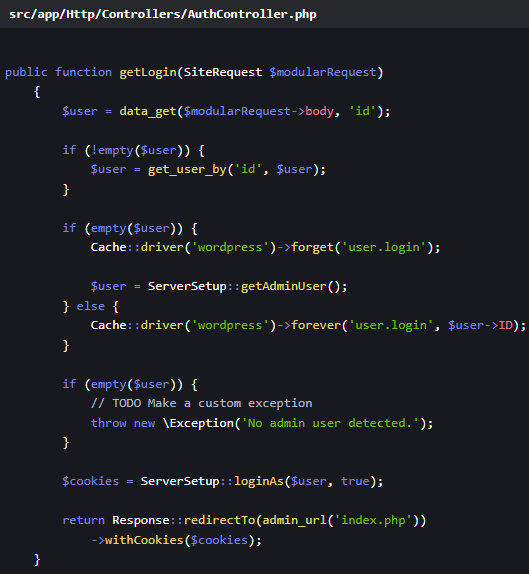
“In the controller src/app/Http/Controllers/AuthController.php, blueprint getLogin(SiteRequest $modularRequest), the code attempts to learn an particular person ID from the body of $modularRequest,” Patchstack explains.
“Since this code will seemingly be accessed by unauthenticated customers on account of of the flaw previously defined, it permits a straight privilege escalation,” the researchers mutter.
Provide: Patchstack
The patch in Modular DS model 2.5.2 eliminated URL-essentially based fully route matching. It is a ways now pushed solely by validated filter common sense, added a default 404 route, handiest recognizes ‘form’ values for route binding, and entails a stable failure mode for unrecognized requests.
Customers of Modular DS are suggested to upgrade to model 2.5.2 or later as rapidly as doable.
In a safety bulletin, the supplier advises customers to search out out about server procure admission to logs for suspicious requests, test admin customers for rogue additions, and regenerate all WordPress salts after updating to presumably the most most new edition.
Mobile forensics Secrets and techniques Security Cheat Sheet: From Sprawl to Have watch over
Whether or now not you might well perchance be cleaning up extinct keys or environment guardrails for AI-generated code, this manual helps your crew procure securely from the originate.
Rep the cheat sheet and take the guesswork out of secrets and techniques management.
Recent Posts
- US Fatherland Safety Investigates Whether Bovino Made Disparaging Comments About Jewish Faith
- TikTok guidelines out the usage of cease-to-cease message encryption
- Missing Lady Last Seen Stressful To Bag Out Family’s Car Is Found Ineffective in Yard Days Later
- Rhode Island Priests Abused A total bunch of Adolescents Over A protracted time, Document Finds – The Unusual York Conditions
- FBI seizes LeakBase cybercrime forum, files of 142,000 members




