
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity > Evolution of Ransomware: Multi-Extortion Ransomware Attacks

Apr
Evolution of Ransomware: Multi-Extortion Ransomware Attacks
Internet investigation

Internet investigation Ransomware’s Real-World Impression Throughout Industries
In February 2026, the College of Mississippi Scientific Heart (UMMC) fell victim to a ransomware attack. The incident took the Story digital neatly being file machine offline across 35 clinics and further than 200 telehealth web sites, forcing the cancellation of chemotherapy appointments and the postponement of non-emergency surgical procedures. Scientific team possess been required to revert to paper-basically based totally workflows, leaving limitless patients to undergo the implications.
UMMC is mighty from an isolated case. In response to contemporary info, 93% of U.S. healthcare organizations experienced at the very least one cyberattack in 2025, and 72% of respondents reported that at the very least one incident instantly disrupted patient care.
The manufacturing and monetary sectors are equally exposed. In February 2026, price processing network BridgePay suffered a ransomware attack that took its APIs, digital terminals, and price pages fully offline. Throughout all industries, publicly disclosed ransomware attacks surged 49% year-over-year in 2025, reaching 1,174 confirmed incidents.
As hospitals quit treatments, monetary institutions freeze transactions, and manufacturers shut down manufacturing traces, ransomware has firmly established itself as an rapid enterprise risk with tangible operational consequences.
Internet investigation The Evolution of Ransomware: Double Extortion
Early ransomware operated on a uncomplicated premise: infiltrate a machine, encrypt info, and ask price in change for the decryption key. As organizations began countering this tactic by restoring from backups barely than paying ransoms, menace actors responded by growing a extra profitable model — double extortion.
In a double extortion attack, adversaries first exfiltrate sensitive info — reminiscent of patient data and billing info — forward of encrypting the target machine. Victims are then compelled on two fronts: pay to obtain the decryption key, or face public publicity of the stolen info.
Backups alone are insufficient in distinction model. Since attackers already hold the tips, refusing to pay the ransom can consequence within the final public originate of sensitive info, exposing organizations to essential enterprise losses and regulatory consequences.
The menace panorama has endured to escalate, with triple extortion cases on the upward push — a tactic whereby attackers instantly contact a victim organization’s customers or companions to appear at extra force.
As of 2025, 124 crammed with life ransomware teams possess been known, 73 of that are newly emerged.
The proliferation of AI-powered instruments has diminished the barrier to entry for cybercrime, making ransomware capabilities extra and further accessible to much less sophisticated actors.
Internet investigation A Protection Architecture for Multi-Extortion Threats
The upward push of multi-extortion ransomware essentially adjustments the assumptions underlying inclined protection suggestions. Perimeter-basically based totally prevention alone isn’t any longer ample.
Organizations desire a security posture that protects info from being weaponized after a breach — rendering exfiltrated info unreadable, blockading ransomware from accessing info within the essential home, and enabling quick recovery even when an attack succeeds.
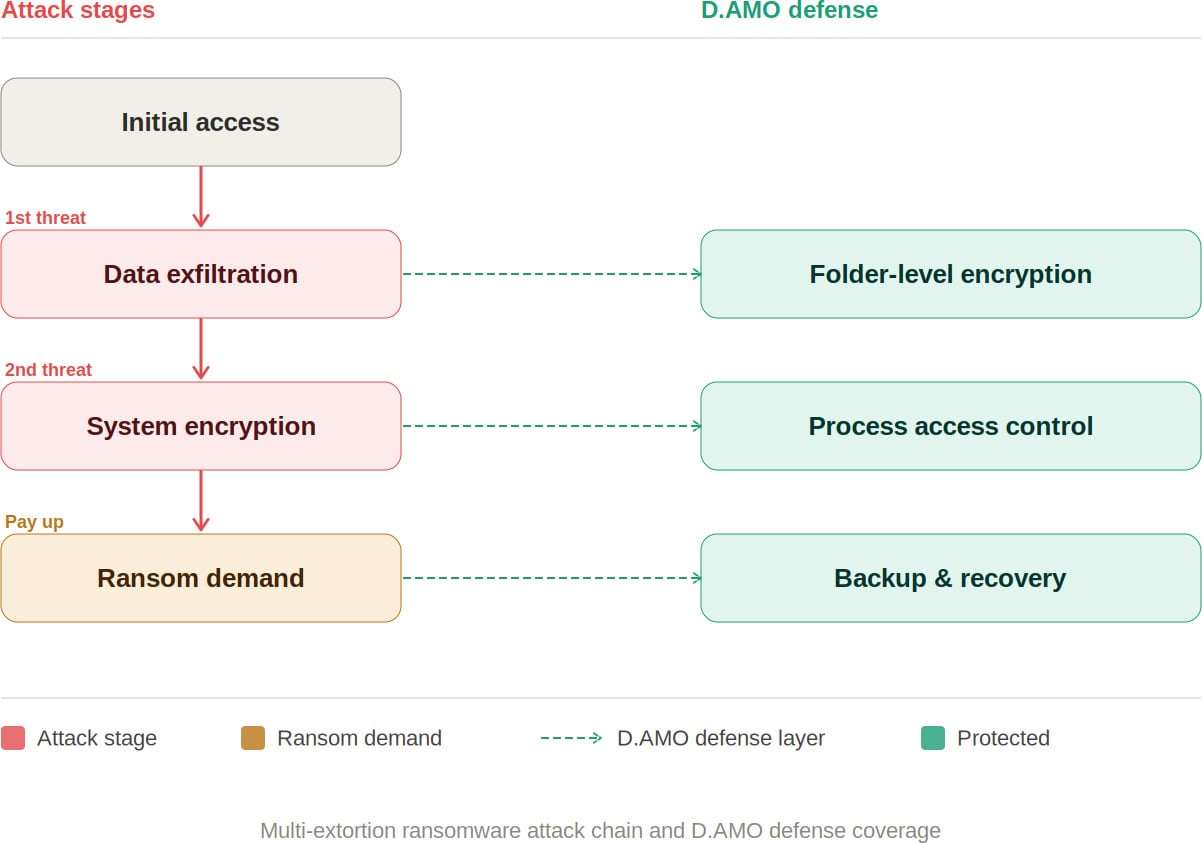
Internet investigation D.AMO: Blocking Every Stage of a Ransomware Attack
D.AMO, developed by Penta Safety, is an encryption-basically based totally info protection platform designed to tackle every allotment of a multi-extortion ransomware attack. It delivers integrated encryption, earn entry to management, and backup recovery across on-premises and cloud environments.
By applying file encryption and course of-basically based totally earn entry to management applied sciences, D.AMO protects serious info saved on servers and PCs — safeguarding sensitive knowledge against malicious applications by contrivance of sturdy earn entry to enforcement. D.AMO’s key capabilities are as follows:
Folder-Stage File Encryption
D.AMO KE encrypts all info within administrator-designated folders at the OS level. Deployable by contrivance of an installer with out provide code modification, it operates utilizing kernel-level encryption skills, enabling quick and stable encryption on existing systems with out a disruption to the user journey.
Encryption policies are utilized at the folder level, guaranteeing fixed protection with minimal operational overhead. Significantly, even when an attacker exfiltrates sensitive info, the facts live encrypted — neutralizing the tips publicity menace that is central to double extortion.
Salvage entry to Management
D.AMO KE enforces strict earn entry to management over processes and OS users, allowing entirely explicitly authorized earn entry to. Ransomware and various malicious applications are automatically blocked from accessing encrypted folders, combating unauthorized file manipulation.
All blocked task is recorded by contrivance of an audit log characteristic and would possibly maybe additionally be reviewed centrally by contrivance of D.AMO Management Heart.
Backup and Recovery
Even within the tournament of a a hit attack, organizations can resume operations by contrivance of an independently managed recovery machine. With D.AMO in home, the flexibility to revive from backup deal reduces dependence on decryption key negotiations with menace actors.
As multi-extortion ways change into the norm, neutralizing the tips attackers explore to employ has change into a strategic priority. Organizations need the flexibility to render exfiltrated info unreadable, quit ransomware from accessing info, and get better all of sudden when incidents happen.
D.AMO addresses every stage of a ransomware attack within a single integrated platform — combining encryption, course of-basically based totally earn entry to management, and backup recovery loyal into a unified line of protection.
Desire to learn extra? Accumulate the D.AMO Info Sheet.
Sponsored and written by Penta Safety.
Recent Posts
- Circle Defends Restricted Role in $285 Million Crypto Hack, Citing Correct Boundaries
- Your router would possibly perhaps presumably be conclude-of-lifestyles and apart from you develop no longer even are mindful about it
- Evolution of Ransomware: Multi-Extortion Ransomware Attacks
- Buying for Iran’s Disappeared Prisoners
- Justice Division worker who become once prosecuted over Jan. 6 Capitol assault resigns


