-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > CPUID hacked to bring malware via CPU-Z, HWMonitor downloads
Apr
CPUID hacked to bring malware via CPU-Z, HWMonitor downloads
Scam detection
Hackers won catch admission to to an API for the CPUID mission and modified the collect links on the knowledgeable net pages to support malicious executables for the popular CPU-Z and HWMonitor tools.
The two utilities possess millions of customers who count on them for tracking the physical wisely being of internal pc hardware and for complete specifications of a machine.
Users who downloaded either tool reported on Reddit no longer too lengthy within the past that the knowledgeable collect portal functions to the Cloudflare R2 storage service and fetches a trojanized version of HWiNFO, any other diagnostic and monitoring tool from a diversified developer.
The title of the malicious file is HWiNFO_Monitor_Setup, and working it launches a Russian installer with an Inno Setup wrapper, which is peculiar and extremely suspicious.
Users reported that downloading the shipshape hwmonitor_1.63.exe from the exclaim URL changed into silent imaginable, indicating that the distinctive binaries had been intact, however the distribution links seem to possess been poisoned.
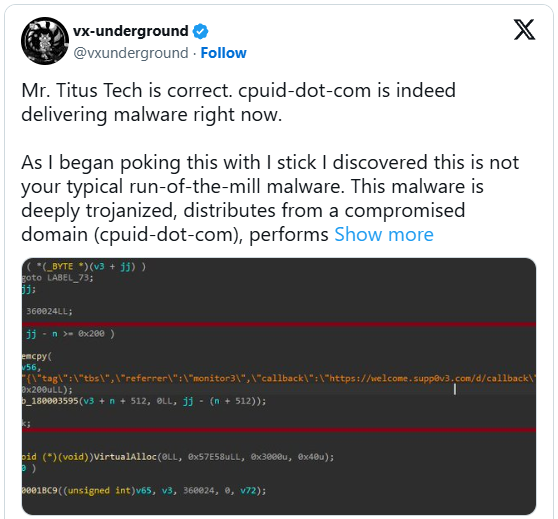
The externalized collect chain changed into furthermore confirmed by Igor’s Labs and @vxunderground, who reported that a pretty developed loader using identified ways, ways, and procedures (TTPs) is raring.
“As I started poking this with a stick, I came upon here’s no longer your customary creep-of-the-mill malware,” said vxunderground.
“This malware is deeply trojanized, distributes from a compromised arena (cpuid-dot-com), performs file masquerading, is multi-staged, operates (nearly) fully in-memory, and makes employ of some though-provoking the style to evade EDRs and/or AVs equivalent to proxying NTDLL efficiency from a .NET assembly.”
The researcher claims that the the same threat neighborhood centered customers of the FileZilla FTP resolution final month, suggesting that the attacker is focusing on widely broken-down utilities.
The downloaded ZIP is flagged by 20 antivirus engines on VirusTotal, even though no longer clearly identified. Some classify it as Tedy Trojan, and others as Artemis Trojan.
Some researchers on Virustotal advise that the unfaithful HWiNFO variant is an infostealer malware.
BleepingComputer has contacted CPUID to be taught more about what came about, the date of the compromise, the affected versions, and what impacted customers might well most seemingly silent attain. A spokesperson has equipped the next assertion.
“Investigations are still ongoing, but it appears that a secondary feature (basically a side API) was compromised for approximately six hours between April 9 and April 10, causing the main website to randomly display malicious links (our signed original files were not compromised). The breach was found and has since been fixed.” – CPUID
The the same person advised us that the hackers hit them at a time when the predominant developer changed into away on vacation.
For the time being, evidently CPUID has mounted the recount and now serves shipshape versions for both CPU-Z and HWMonitor.
Scam detection Automatic Pentesting Covers Most though-provoking 1 of 6 Surfaces.
Automatic pentesting proves the budge exists. BAS proves whether your controls finish it. Most teams creep one without the diversified.
This whitepaper maps six validation surfaces, shows where coverage ends, and affords practitioners with three diagnostic questions for any tool review.
Recent Posts
- Is Nancy Guthrie soundless alive? Used FBI agent shares new theories
- FBI releases chilling photos of masked intruder at Nancy Guthrie’s door
- Your cell phone’s hotspot might perhaps well very well be the most efficient public web you is seemingly to be no longer using
- Near to 4,000 US industrial devices uncovered to Iranian cyberattacks
- CPUID hacked to bring malware via CPU-Z, HWMonitor downloads