-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Investigations > Chinese language say hackers exercise rootkit to camouflage ToneShell malware process

Dec
Chinese language say hackers exercise rootkit to camouflage ToneShell malware process
Mobile forensics

A fresh sample of the ToneShell backdoor, most frequently viewed in Chinese language cyberespionage campaigns, has been delivered via a kernel-mode loader in assaults towards authorities organizations.
The backdoor has been attributed to the Mustang Panda community, furthermore on occasion called HoneyMyte or Bronze President, that most frequently targets authorities companies, NGOs, ponder tanks, and diversified excessive-profile organizations worldwide.
Security researchers at Kaspersky analyzed a malicious file driver learned on computer systems in Asia and learned that it has been musty in campaigns since no now not up to February 2025 towards authorities organizations in Myanmar, Thailand, and diversified Asian worldwide locations.
Proof confirmed that the compromised entities had prior infections with older ToneShell variants, PlugX malware, or the ToneDisk USB worm, furthermore attributed to say-backed Chinese language hackers.
Glossy kernel-mode rootkit
In step with Kaspersky, the fresh ToneShell backdoor turned into once deployed by a mini-filter driver named ProjectConfiguration.sys and signed with a stolen or leaked certificates reliable between 2012 and 2015 and issued to Guangzhou Kingteller Expertise Co., Ltd.
Mini-filters are kernel-mode drivers that scuttle into the Windows file-machine I/O stack and can watch, alter, or block file operations. Security instrument, encryption tools, and backup utilities most frequently exercise them.
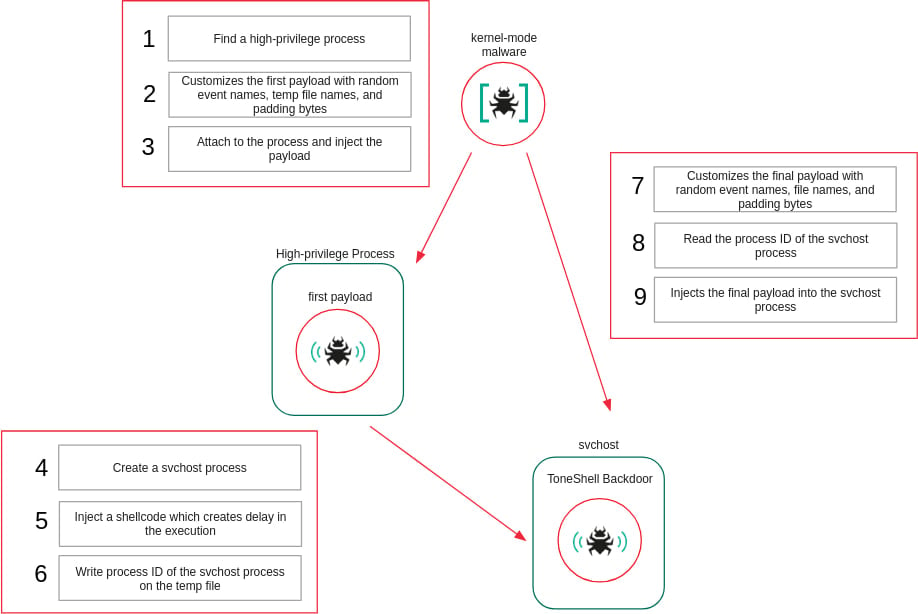
ProjectConfiguration.sys embeds two user-mode shellcodes in its .knowledge part, each performed as a separate user-mode thread to be injected into user-mode processes.
To evade static evaluation, the motive force resolves required kernel APIs at runtime by enumerating loaded kernel modules and matching operate hashes, rather then importing functions straight.
It registers as a mini-filter driver and intercepts file-machine operations associated to deletion and renaming. When such operations purpose the motive force itself, they are blocked by forcing the ask to fail.
The driver furthermore protects its carrier-associated registry keys by registering a registry callback and denying makes an try to affect or start them. To be obvious precedence over security products, it selects a mini-filter altitude above the antivirus-reserved fluctuate.
Additionally, the rootkit interferes with Microsoft Defender by enhancing the configuration of the WdFilter driver so it’s now not loaded into the I/O stack.
To protect injected user-mode payloads, the motive force maintains a checklist of safe course of IDs, denies take care of obtain admission to to those processes whereas the payloads are executing, and eliminates security once execution completes.
“This is the first time we’ve seen ToneShell delivered through a kernel-mode loader, giving it protection from user-mode monitoring and benefiting from the rootkit capabilities of the driver that hides its activity from security tools,” says Kaspersky.
Source: Kaspersky
Glossy ToneShell variant
The fresh variant of the ToneShell backdoor that Kaspersky analyzed functions changes and stealth enhancements. The malware now uses a brand fresh host identification diagram in step with a 4-byte host ID market as a replace of the 16-byte GUID musty beforehand, and furthermore applies community visitors obfuscation with pretend TLS headers.
In terms of the supported distant operations, the backdoor now helps the following commands:
- 0x1 — Originate a non eternal file for incoming knowledge
- 0x2 / 0x3 — Download file
- 0x4 — Murder download
- 0x7 — Build shell by plan of a pipe
- 0x8 — Receive operator picture
- 0x9 — Halt shell
- 0xA / 0xB — Upload file
- 0xC — Murder upload
- 0xD — Discontinuance connection
Kaspersky advises that memory forensics is key in uncovering ToneShell infections backed by the fresh kernel-mode injector.
The researchers have excessive self assurance in attributing the fresh ToneShell backdoor sample to the Mustang Panda cyberespionage community. They assess that the likelihood actor has evolved its ways, suggestions, and procedures to develop operational stealth and resilience.
The cybersecurity company gives in its file a instant checklist of indicators of compromise (IoCs) to help organizations detect Mustang Panda intrusions and protect towards them.
Mobile forensics Shatter down IAM silos bask in Bitpanda, KnowBe4, and PathAI
Broken IAM is not staunch an IT peril – the affect ripples across your total trade.
This purposeful e-book covers why venerable IAM practices fail to abet up with fashioned calls for, examples of what “good” IAM appears to be like to be like bask in, and a easy checklist for constructing a scalable technique.
Tags
- Chinese cybercrime digital-forensics email-fraud forensics|digital-forensics Investigation investigationphishing-attack malware online-scam private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker State
Recent Posts
- US Fatherland Safety Investigates Whether Bovino Made Disparaging Comments About Jewish Faith
- Missing Lady Last Seen Stressful To Bag Out Family’s Car Is Found Ineffective in Yard Days Later
- Rhode Island Priests Abused A total bunch of Adolescents Over A protracted time, Document Finds – The Unusual York Conditions
- FBI seizes LeakBase cybercrime forum, files of 142,000 members
- The TikTokers Discovering out the Epstein Recordsdata So You Don’t Like To




