
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity > Russian hackers exploit Zimbra flaw in Ukrainian govt attacks

Mar
Russian hackers exploit Zimbra flaw in Ukrainian govt attacks
Identity theft

Hackers piece of APT28, a say-backed possibility neighborhood linked to Russia’s defense power intelligence provider (GRU), are exploiting a Zimbra Collaboration Suite (ZCS) vulnerability in attacks focusing on Ukrainian executive entities.
This excessive-severity security flaw (tracked as CVE-2025-66376 and patched in early November) stems from a stored inferior-set apart scripting (XSS) that unauthenticated attackers can exploit to assemble some distance off code execution (RCE) and compromise the Zimbra server and the design’s electronic mail legend.
On Wednesday, the Cybersecurity and Infrastructure Security Agency (CISA) added the vulnerability to its catalog of vulnerabilities exploited in the wild. CISA additionally ordered Federal Civilian Executive Branch (FCEB) agencies to stable their servers within two weeks, as mandated by the Binding Operational Directive (BOD) 22-01 issued in November 2021.
While the U.S. cybersecurity agency did not present extra well-known beneficial properties on the continuing exploitation of CVE-2025-66376, security researchers at Seqrite Labs reported a day earlier that the Zimbra XSS vulnerability had been exploited by APT28 defense power hackers in attacks in opposition to Ukraine.
The Ukrainian Verbalize Hydrology Agency (a well-known infrastructure entity below the Ministry of Infrastructure that affords navigational, maritime, and hydrographic make stronger) became as soon as one of the targets of this phishing campaign (named Operation GhostMail).
“The phishing email has no malicious attachments, no suspicious links, no macros. The entire attack chain lives inside the HTML body of a single email, there are no malicious attachments,” Seqrite Labs acknowledged.
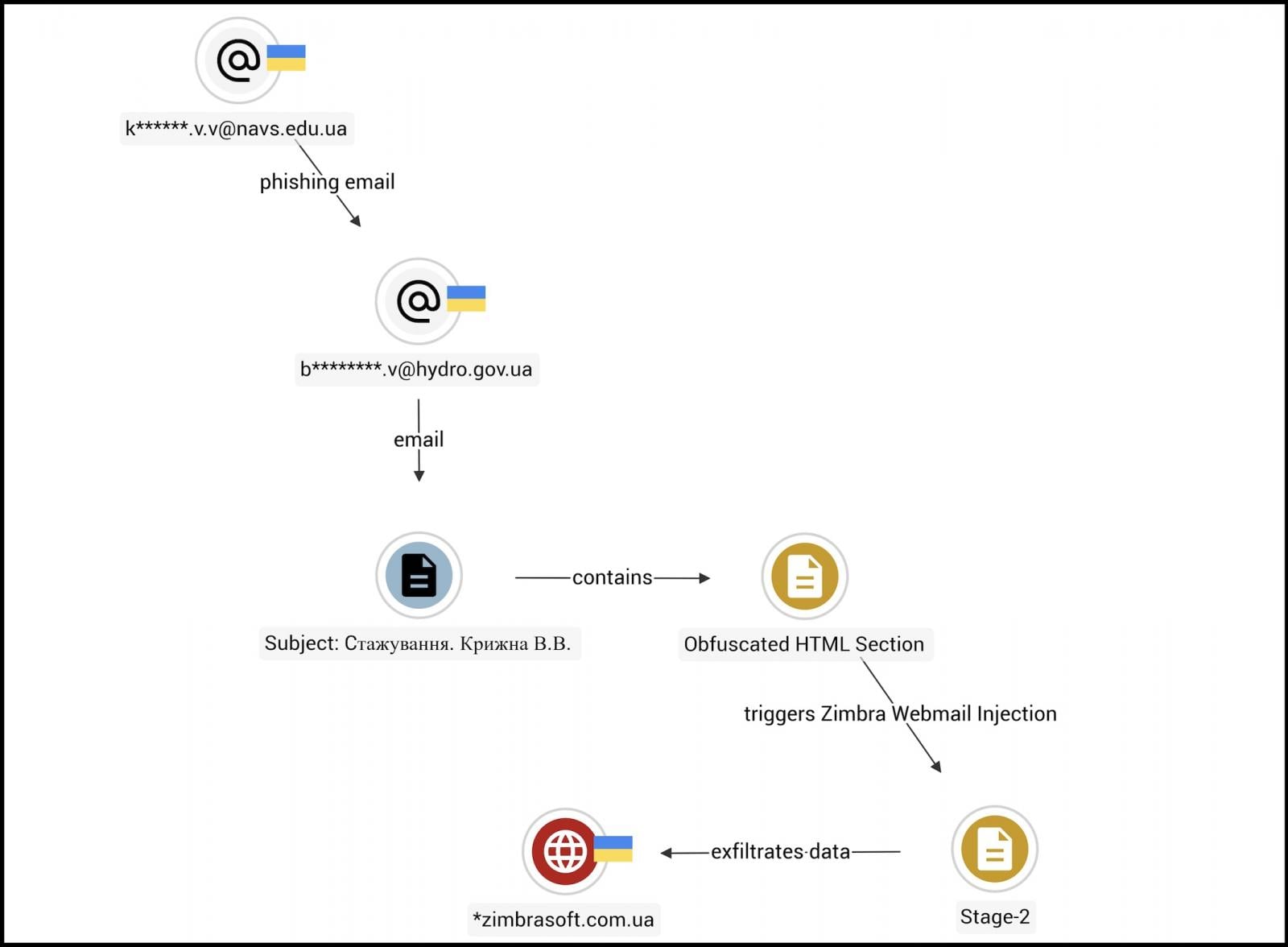
The APT28 (aka Admire Accumulate, Strontium) hackers’ malicious messages delivered an obfuscated JavaScript payload that exploits the CVE-2025-66376 vulnerability when the recipient opens the email in a susceptible Zimbra webmail session.
“The script executes silently in the browser and begins harvesting credentials, session tokens, backup 2FA codes, browser-saved passwords, and the contents of the victim’s mailbox going back 90 days with all the data exfiltrated over both DNS and HTTPS,” the researchers added.
Zimbra security flaws tend to be centered in attacks, including by Russian say-backed possibility teams, and were feeble to breach hundreds of susceptible electronic mail servers in hottest years.
To illustrate, starting in February 2023, the Russian Winter Vivern cyberespionage neighborhood feeble one other reflected XSS exploit to breach Zimbra webmail portals and look on the communications of NATO-aligned organizations and persons, including executive officers, defense power personnel, and diplomats.
In October 2024, U.S. and U.K. cyber agencies additionally warned that APT29 (aka At ease Accumulate, Hour of darkness Blizzard) hackers linked to Russia’s International Intelligence Provider (SVR) were attacking susceptible Zimbra servers “at a mass scale,” exploiting a vulnerability previously feeble to steal electronic mail legend credentials.
Zimbra is a broadly approved electronic mail and collaboration software suite feeble by a full bunch of hundreds and hundreds of individuals, including a full bunch of executive agencies and hundreds of businesses worldwide.
Identity theft Purple Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Purple Report 2026 unearths how fresh threats spend math to detect sandboxes and veil in undeniable gape.
Download our prognosis of 1.1 million malicious samples to expose the high 10 suggestions and seek if your security stack is blinded.
Tags
- cybercrime cybercrimephishing-attack cybersecurity email-fraud forensics|digital-forensics hackers Investigation malware online-scam private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker Russian
Recent Posts
- GreyVibe hackers spend ChatGPT, Gemini to vitality cyberattacks
- DOJ probe targets Reid Hoffman nonprofit tied to E. Jean Carroll case
- FBI warns of spurious FIFA websites working World Cup fraud schemes
- The particular lesson of the E. Jean Carroll investigation is Trump’s weak point
- Hackers exploit FortiClient EMS flaw to push infostealer malware



