-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Bitrefill blames North Korean Lazarus group for cyberattack

Mar
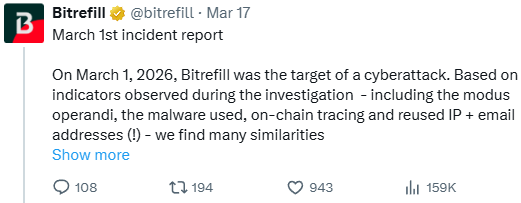
Bitrefill blames North Korean Lazarus group for cyberattack
Scam detection

Crypto-powered reward card retailer Bitrefill says that the assault it suffered initially of the month used to be likely perpetrated by North Korean hackers of the Bluenoroff group.
All around the investigation, the platform noticed indicators same to outdated assaults attributed to the North Korean threat actor, love ideas, malware, IP and e-mail addresses.
“In accordance with indicators noticed finally of the investigation – in conjunction with the modus operandi, the malware weak, on-chain tracing and reused IP + e-mail addresses (!) – we uncover many similarities between this assault and past cyberattacks by the DPRK Lazarus / Bluenoroff group in opposition to other companies in the crypto industries,” reads Bitrefill’s assertion.
Bitrefill is a mid-sized e-commerce platform that lets in folk to pay in cryptocurrency for reward playing cards at stores in 150 countries. The reward playing cards would possibly perhaps also also be weak to pay for anything else from clothing, food and groceries, successfully being and class products to bills, products and services, gas, transportation, and electronics.
The platform supports more than 600 mobile operators and thousands of manufacturers worldwide.
On March 1st, Bitrefill presented technical disorders affecting obtain entry to to its web draw and app. A day later, the company disclosed that it had known a security topic and took all products and services offline.
Even supposing person balances weren’t affected, the slack restoration of all products and services aloof continues to at present.
The breach used to be realized after Bitrefill noticed suspicious dealer buying patterns, exploitation of reward card stock and provide strains, and draining of some “sizzling” wallets.
The investigation the firm launched to resolve the trigger printed that the assault originated on a compromised worker’s computer.
The attackers stole legacy credentials and weak them to acquire entry to a snapshot with manufacturing secrets, later escalating obtain entry to to the bigger Bitrefill infrastructure, in conjunction with parts of the database and some cryptocurrency wallets.
About 18,500 aquire recordsdata containing customer e-mail addresses, IP addresses, and cryptocurrency charge addresses were uncovered in the breach. For 1,000 purchases, customer names were also uncovered.
Even supposing this recordsdata is saved in encrypted construct, Bitrefill notes that the attackers would possibly perhaps also win bought the decryption keys.
Bitrefill says this used to be the most excessive cyberattack it has suffered in its ten years of existence, nevertheless it survived with minimal losses, which will likely be lined from its capital.
Within the atomize, Bitrefill believes that attackers were after cryptocurrency and reward card inventory, not customer recordsdata.
BlueNoroff, typically typically known as APT38, is a cluster of the Lazarus group that has been active since as a minimal 2014. It in general targets monetary organizations, with a more latest focal point on the cryptocurrency industrial, the aim being crypto theft.
Bitrefill says this used to be the most excessive cyberattack it has suffered in the ten years of its existence, nevertheless it survived with minimal losses, which will likely be lined from its capital.
Meanwhile, it is expanding safety opinions and pen-testing, tightening obtain entry to controls, bettering logging and monitoring, and refining automated shutdown mechanisms.
At this time, most of its products and services win returned to long-established operational dwelling, and customers aren’t required to take any movement beyond treating incoming communications with additional warning.
Scam detection Crimson Chronicle 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Crimson Chronicle 2026 reveals how new threats exhaust math to detect sandboxes and cloak in undeniable survey.
Download our diagnosis of 1.1 million malicious samples to expose the cease 10 ideas and look if your safety stack is blinded.
Recent Posts
- Lawmakers name for federal investigation into gambling dysfunction
- James Comey: ‘Justice Can’t Be a Political Force’
- AI Is Handing Hackers Instruments That Once Belonged to Elite Attackers
- Of us Energy Rep collectively protests pollscarcity at Seoul polling stations
- Disabled ACR to your TV? I prepare a router-primarily based VPN for extra protection