
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Dutch govt warns of Signal, WhatsApp myth hijacking attacks

Mar
Dutch govt warns of Signal, WhatsApp myth hijacking attacks
Cybercrime

Russian relate-sponsored hackers were linked to an ongoing Signal and WhatsApp phishing campaign focused on govt officers, military personnel, and journalists to assemble access to delicate messages.
This narrative comes from the Netherlands Defence Intelligence and Security Carrier (MIVD) and the Netherlands Total Intelligence and Security Carrier (AIVD), who confirmed that Dutch govt workers were focused in the attacks.
The Dutch intelligence companies relate the operation depends on phishing and social-engineering methods that abuse loyal authentication ingredients to lift over accounts and covertly video show new messages.
Signal posted on social media that it’s privy to focused phishing attacks which delight in resulted in myth takeovers and warned users to stay vigilant.
“We are aware of recent reports regarding targeted phishing attacks that have resulted in account takeovers of some Signal users, including government officials and journalists,” Signal posted on BlueSky.
“We take this very seriously. To be clear: Signal’s encryption and infrastructure have not been compromised and remain robust. These attacks were executed via sophisticated phishing campaigns, designed to trick users into sharing information – SMS codes and/or Signal PIN – to gain access to users’ accounts.”
Signal says that after sending SMS codes, they continuously warn no longer to portion SMS codes or PINs with someone, along side Signal workers or products and companies.
Cybercrime Phishing messages impersonate Signal toughen
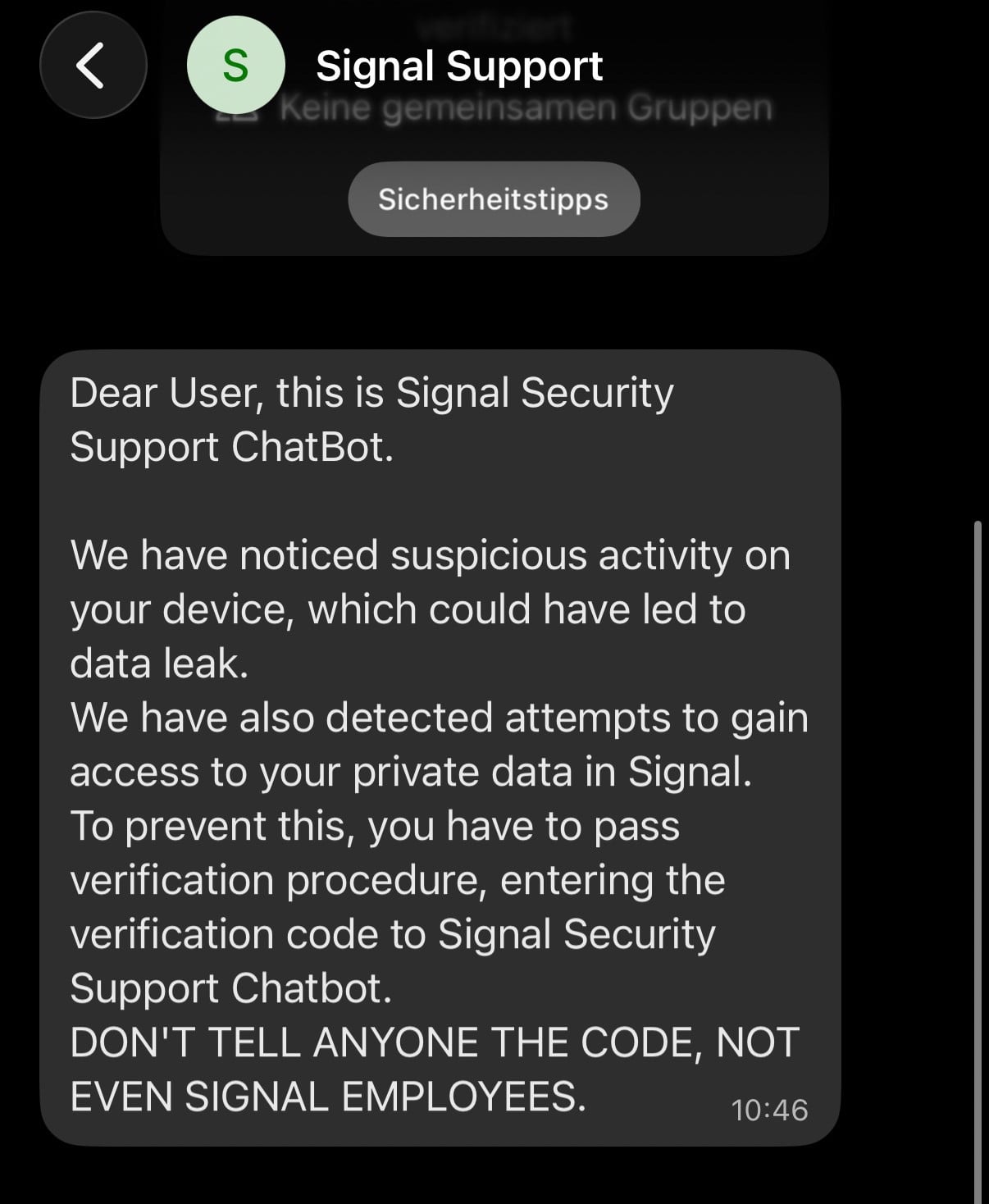
One amongst the most fundamental assault solutions involves impersonating a faux “Signal Security Support Chatbot” that warns the user that suspicious activity became detected on their myth.
The message then tells the user to total a “verification procedure” by sharing a verification code despatched to their phone.
“We have noticed suspicious activity on your device, which could have led to data leak. We have also detected attempts to gain access to your private data in Signal,” reads the Signal phishing message.
“To prevent this, you have to pass verification procedure, entering the verification code to Signal Security Support Chatbot.”
Offer: Signal
After the victim presents the SMS verification code and their Signal PIN, attackers can lift corpulent attach an eye on of the parable by registering it on their very have instrument.
According to the advisory, once attackers assemble access to an myth, they’ll furthermore substitute the phone amount associated to it to one below their attach an eye on. This permits them to access the victim’s contact list and incoming messages, along side messages despatched in community chats.
Attackers can also merely furthermore impersonate the victim by sending messages from the compromised myth.
As Signal shops chat historical previous in the neighborhood on the instrument, when victims re-register a brand new myth, they would perhaps pick up access to their passe messages, potentially leading them to thrill in nothing uncommon occurred.
“The victim is unable to access their account, although they are able to create a new Signal account using their existing telephone number, as the actor has already linked the compromised account to a new telephone number,” warns the Dutch intelligence companies.
“Because Signal stores the chat history locally on the phone, a victim can regain access to that history after re‑registering. As a result, the victim may assume that nothing is wrong. The Dutch services want to stress that this assumption could be incorrect.”
The advisory furthermore says a second plot became observed abusing Signal’s and WhatsApp’s instrument linking functionality.
Attackers ship victims a malicious QR code or link that looks to be to be an invite to enroll in a chat community or connect with one other user. When the victim scans the code or opens the link, it hyperlinks the attacker’s instrument to the victim’s myth as a replace.
Every Signal and WhatsApp offer a linked instrument feature that enables users to connect devices, equivalent to computers or medications, to their accounts so that they’ll ship and receive messages from more than one devices. Here’s usually done by scanning a QR code generated by the most fundamental mobile instrument, which authorizes the brand new instrument to access and synchronize the parable’s messages.
Once connected, the attacker good points access to the victim’s messages and would perhaps well well be ready to learn chat historical previous, video show conversations in right time, and ship messages in the victim’s establish.
Unlike myth takeovers, victims usually attach access to their accounts, which is keen to catch a breach more difficult to detect.
The Dutch intelligence companies expose users no longer to portion delicate or classified files by messaging apps except namely licensed.
They furthermore point out checking the list of devices linked to Signal and WhatsApp accounts and without extend laying aside unknown devices.
The same precautions in opposition to electronic mail phishing attacks prepare to messaging apps, which encompass ignoring unsolicited invitations, hyperlinks, or QR codes except they delight in verified their legitimacy by one other relied on communication channel.
These forms of messaging app phishing campaigns are no longer new.
Last one year, Google reported that Russian risk actors focused Signal users by abusing ingredients equivalent to instrument linking to assemble access to victims’ communications.
In December, GenDigital detected a WhatsApp instrument-linking QR code phishing campaign focused on users in Czechia, even though it became no longer attributed to any dispute risk actor.
Cybercrime Red File 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red File 2026 finds how new threats exercise math to detect sandboxes and cowl in easy gaze.
Obtain our diagnosis of 1.1 million malicious samples to expose the tip 10 methods and gape in case your security stack is blinded.
Recent Posts
- Ethereum Pushes Sure Signing to Fight Expensive Crypto Scams
- West Pharmaceutical says hackers stole records, encrypted programs
- Iranian hackers focused major South Korean electronics maker
- CHARLIE MARCUS: The Canvas hack reveals that colleges must ditch Chromebooks and come again to particular finding out
- FBI, Secret Provider probe Wisconsin brewery proprietor over free beer offer after alleged Trump killing are attempting



