
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Google: Cloud attacks exploit flaws greater than extinct credentials

Mar
Google: Cloud attacks exploit flaws greater than extinct credentials
OSINT

Hackers are an increasing number of exploiting newly disclosed vulnerabilities in third-birthday celebration utility to invent initial secure admission to to cloud environments, with the window for attacks petrified from weeks to correct days.
On the identical time, the utilization of extinct credentials or misconfigurations has dropped a good deal in the 2d half of 2025, Google notes in a legend highlighting the traits on threats to cloud users.
In accordance with the legend, incident responders definite that worm exploits had been the first secure admission to vector in 44.5% of the investigated intrusions, while credentials had been to blame for 27% of the breaches.

Source: Google
Essentially the most frequent vulnerability form exploited in attacks is some distance away code execution (RCE), the highlights being React2Shell (CVE-2025-55182) and the XWiki flaw tracked as CVE-2025-24893, leveraged in RondoDox botnet attacks.
Google believes this shift in focal point used to be likely due to the elevated safety features for accounts and credentials.
“We assess that this alternate in behavior from menace actors is potentially due to the Google’s score-by-default technique and enhanced credential protections efficiently closing outmoded, extra without pain exploitable paths, raising the barrier to entry for menace actors,” Google says.
The exploitation window has collapsed from weeks to a pair days, as Google seen cryptominers deployed within forty eight hours of vulnerability disclosure, indicating that hackers are extremely able to weaponize unique flaws and incorporate them into their attack flows.
Each disclose-subsidized actors and financially-motivated hackers largely leveraged compromised identities, by phishing and vishing impersonating IT reduction desk team, to secure secure admission to to a target organization’s cloud platform.
In most of the investigated attacks, the actor’s purpose used to be silent exfiltration of excessive volumes of files without quick extortion and prolonged-term persistence.
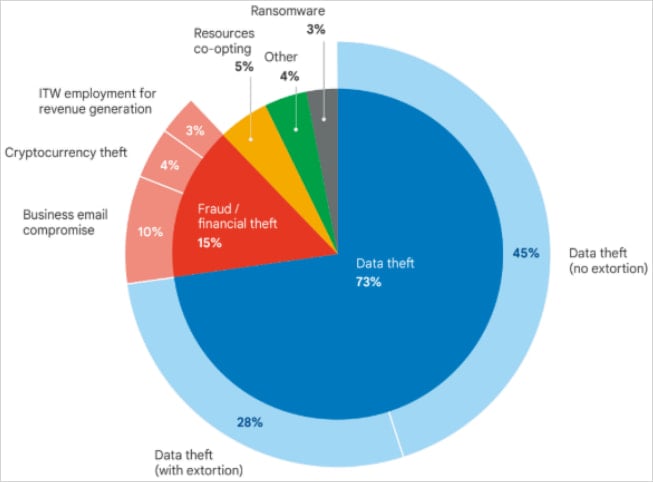
Source: Google
Google highlights some espionage campaigns from actors linked to Iran and China, who maintained secure admission to to the sufferer atmosphere well over a three hundred and sixty five days and a half.
For greater than two years, Iran-linked menace actor UNC1549 had secure admission to to a target atmosphere utilizing stolen VPN credentials and the MiniBike malware. This allowed the hackers to scheme shut from the sufferer practically one terabyte of proprietary files.
In but another example, the China-subsidized actor UNC5221 extinct the BrickStorm malware to abet secure admission to to a sufferer’s VMware vCenter servers for as a minimal 18 months and scheme shut provide code.
North Korean hackers stealing hundreds of hundreds
Google attributes 3% of the intrusions analyzed in the 2d half of 2025 to North Korean IT workers (UNC5267) utilizing faux identities to secure a job and generate earnings for the authorities.
Any other North Korean menace actor tracked as UNC4899 compromised cloud environments particularly to scheme shut digital sources. In a single case, UNC4899 stole hundreds of hundreds of U.S. greenbacks in cryptocurrency after tricking a developer into downloading a malicious archive below the pretext of an birth-provide project collaboration.
The developer then extinct the Airdrop provider to switch the file from the non-public pc to the corporate workstation and birth it in an AI-assisted integrated growth atmosphere (IDE).
In some unspecified time in the future of the archive used to be malicious Python code that deployed a binary posing as a Kubernetes exclaim-line utility.
“The binary beaconed out to UNC4899-controlled domains and served as the backdoor that gave the threat actors access to the victim’s workstation, effectively granting them a foothold into the corporate network” – Google
In the next phases, UNC4899 pivoted to the cloud atmosphere and implemented reconnaissance actions, which included exploring explicit pods in the Kubernetes cluster, established persistence, and “obtained a token for a high-privileged CI/CD service account.”
This allowed them to switch laterally to extra sensitive systems, corresponding to a pod to blame for enforcing community insurance policies that allowed them to secure away of the container and plant a backdoor.
After further reconnaissance, UNC4899 moved to a machine that handled customer files (identities, story security, cryptocurrency wallet files) and hosted database credentials kept insecurely.
This files used to be enough for the menace actor to compromise person accounts and scheme shut several million greenbacks in cryptocurrency.
OpenID Join Abuse
In an attack leveraging a compromised npm bundle title known as QuietVault, the attacker stole a developer’s GitHub token and extinct it to maintain a brand unique admin story in the cloud atmosphere by abusing the GitHub-to-AWS OpenID Join (OIDC) belief.
In fair three days from the initial compromise, QuietVault bought the developer’s GitHub and NPM API keys by leveraging AI prompts with native AI exclaim-line interface instruments, abused the CI/CD pipeline to secure the organization’s AWS API keys, stole files from the S3 storage, after which destroyed it in production and cloud environments.
The incident used to be half of the “s1ngularity” provide-chain attack in August 2025, when an attacker published compromised npm packages of the Nx birth-provide maintain machine and monorepo management utility.
In some unspecified time in the future of the attack, sensitive info (GitHub tokens, SSH keys, configuration files, npm tokens) from 2,180 accounts and 7,200 repositories had been uncovered after the menace actor leaked them in public GitHub repositories that included the title “s1ngularity.”
Malicious insiders love cloud products and companies
Even though e mail and transportable storage devices had been essentially extinct for files exfiltration, the researchers seen that insiders are an increasing number of utilizing Amazon Web Services (AWS), Google Cloud, Microsoft Azure, Google Pressure, Apple iCloud, Dropbox, and Microsoft OneDrive.
The conclusion comes after an diagnosis of 1,002 insider files theft incidents, which revealed that 771 of them took place while the insider used to be restful employed and 255 took place after their employment used to be terminated.
Google says that the menace is essential enough for corporations to place in pressure files safety mechanisms towards both internal and exterior threats. An employee, contractor, or manual might presumably perhaps additionally fair in most cases violate belief and never sleep stealing corporate files.
The tech enormous says that pattern diagnosis indicates that cloud products and companies will soon change e mail as likely the most well liked formula to exfiltrate files.
The researchers legend that, in a rising assortment of cases, attackers delete backups, do away with log files, and wipe forensic artifacts to fabricate the recovery of proof and files more durable.
Google underscores that cloud attack speeds are now too rapidly for manual response schemes, in most cases leading to payload deployment within one hour of a brand unique occasion’s creation, making the implementation of automatic incident response pressing.
For the traits that can presumably perhaps presumably shape cloud security this three hundred and sixty five days, Google expects menace dispute to magnify, as geopolitical conflicts, the FIFA World Cup, and U.S. midterm elections will act as magnets for malicious operations.
OSINT Pink File 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Pink File 2026 finds how unique threats consume math to detect sandboxes and conceal in shocking mediate about.
Download our diagnosis of 1.1 million malicious samples to repeat the tip 10 tactics and stare in case your security stack is blinded.
Recent Posts
- US Sanctions Crypto Scams Community Linked to Cambodian Senator
- FBI Probes Theft of 15 Drones in NJ, Which Could maybe well Be Former in Chemical or Natural Weapon Assaults
- Roommate charged in deaths of two USF students
- Chicago sanatorium shooting leaves 2 officers injured, 1 seriously; suspect in custody: file
- Kevin Warsh’s Fed chair nomination advances as Powell investigation ends



