
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Microsoft Teams phishing targets staff with A0Backdoor malware

Mar
Microsoft Teams phishing targets staff with A0Backdoor malware
Private eye

Hackers contacted staff at monetary and healthcare organizations over Microsoft Teams to trick them into granting distant score admission to through Rapidly Serve and deploy a new piece of malware known as A0Backdoor.
The attacker relies on social engineering to manufacture the worker’s believe by first flooding their inbox with spam and then contacting them over Teams, pretending to be the corporate’s IT staff, offering assistance with the undesirable messages.
To assign score admission to to the target machine, the possibility actor instructs the user to open a Rapidly Serve distant session, which is inclined to deploy a malicious toolset that beneficial properties digitally signed MSI installers hosted in a deepest Microsoft cloud storage chronicle.
In step with researchers at cybersecurity company BlueVoyant, the malicious MSI recordsdata masquerade as Microsoft Teams ingredients and the CrossDeviceService, an actual Windows tool inclined by the Cellular phone Link app.
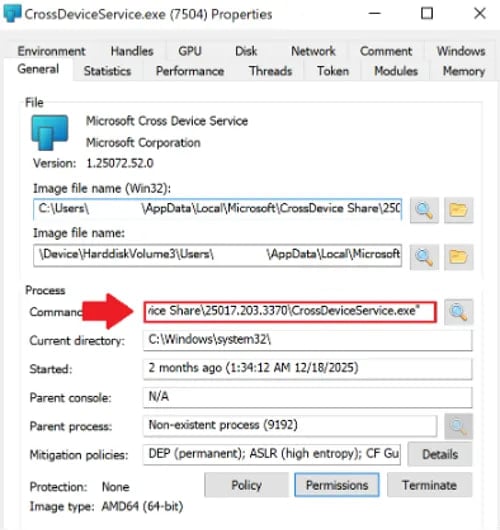
Source: BlueVoyant
Utilizing the DLL sideloading approach with legitimate Microsoft binaries, the attacker deploys a malicious library (hostfxr.dll) that includes compressed or encrypted records. As soon as loaded in memory, the library decrypts the records into shellcode and transfers execution to it.
The researchers disclose that the malicious library also uses the CreateThread neutral to prevent analysis. BlueVoyant explains that the low thread creation would per chance perchance motive a debugger to crash, but it completely does no longer occupy a important affect beneath comparable old execution.
The shellcode performs sandbox detection and then generates a SHA-256-derived key, which it uses to extract the A0Backdoor, which is encrypted using the AES algorithm.
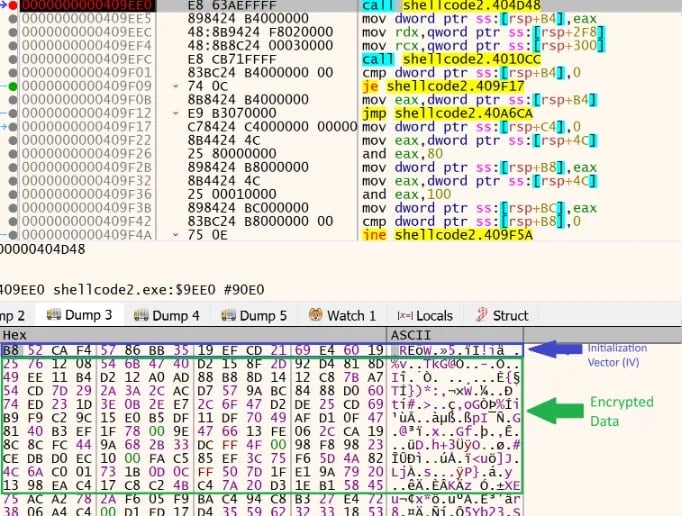
Source: BlueVoyant
The malware relocates itself into a new memory site, decrypts its core routines, and relies on Windows API calls (e.g., DeviceIoControl, GetUserNameExW, and GetComputerNameW) to amass data about the host and fingerprint it.
Communication with the uncover-and-handle watch over (C2) is hidden in DNS traffic, with the malware sending DNS MX queries with encoded metadata in high-entropy subdomains to public recursive resolvers. The DNS servers respond with MX records containing encoded uncover records.
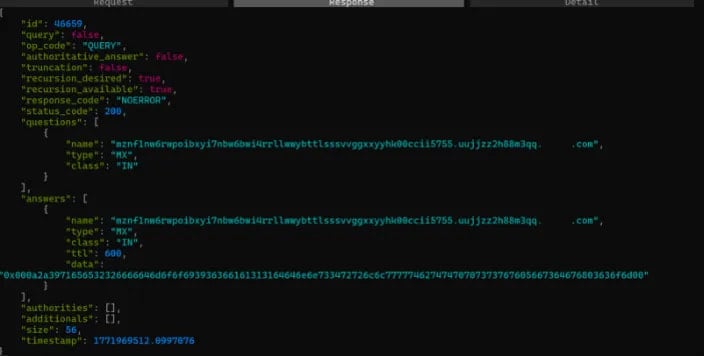
Source: BlueVoyant
“The malware extracts and decodes the leftmost set to recuperate uncover/configuration records, then proceeds accordingly,” explains BlueVoyant.
“Utilizing DNS MX records helps the traffic blend in and can evade controls tuned to detect TXT-primarily based DNS tunneling, that is in all likelihood extra customarily monitored.”
BlueVoyant states that two of the targets of this marketing campaign are a monetary establishment in Canada and a world healthcare organization.
The researchers assess with moderate-to-high self assurance that the selling campaign is an evolution of ways, systems and procedures connected to the BlackBasta ransomware gang, which has dissolved after the inner chat logs of the operation had been leaked.
Whereas there are masses of overlaps, BlueVoyant notes that the usage of signed MSIs and malicious DLLs, the A0Backdoor payload, and using DNS MX-primarily based C2 communication are new ingredients.
Private eye Red Epic 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Epic 2026 unearths how new threats employ math to detect sandboxes and veil in horrifying scrutinize.
Acquire our analysis of 1.1 million malicious samples to order the tip 10 systems and look if your security stack is blinded.
Recent Posts
- US Sanctions Crypto Scams Community Linked to Cambodian Senator
- FBI Probes Theft of 15 Drones in NJ, Which Could maybe well Be Former in Chemical or Natural Weapon Assaults
- Roommate charged in deaths of two USF students
- Chicago sanatorium shooting leaves 2 officers injured, 1 seriously; suspect in custody: file
- Kevin Warsh’s Fed chair nomination advances as Powell investigation ends



