
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > APT28 hackers deploy customized variant of Covenant initiating-provide instrument

Mar
APT28 hackers deploy customized variant of Covenant initiating-provide instrument
Cyber investigation

The Russian utter-subsidized APT28 threat group is the usage of a custom variant of the initiating-provide Covenant post-exploitation framework for prolonged-term espionage operations.
Also tracked as Fancy Accept as true with, Wooded space Blizzard, Strontium, and Sednit, the APT28 hacker group is identified for increasing high-discontinue implants and breaching primary entities, such because the German Parliament, more than one French organizations, authorities networks in Poland, and European NATO member countries.
Researchers at cybersecurity company ESET noticed that since April 2024, the Russian group has started the usage of in assaults two implants named BeardShell and Covenant.
“This dual-implant approach enabled long-term surveillance of Ukrainian military personnel,” ESET notes in a yarn currently.
The 2 pieces of malware were aged only within the near previous to dwelling central executive our bodies of Ukraine in assaults that exploited the CVE-2026-21509 vulnerability in Microsoft Utter of enterprise by map of malicious DOC files.
The researchers uncovered these malware households after discovering SlimAgent, a keylogging implant deployed in a Ukrainian authorities blueprint able to keystroke take hang of, clipboard collection, and screenshot take hang of.
BeardShell is a contemporary implant that leverages the legit cloud storage carrier Icedrive for declare-and-administration (C2) dialog. It can develop PowerShell commands in a .NET runtime ambiance and became once aged alongside with SlimAgent, constant with a yarn from CERT-UA in June 2025.
ESET stumbled on that BeardShell also uses a selected obfuscation methodology beforehand seen in Xtunnel, a community-pivoting instrument that APT28 aged within the 2010s.
Within the hot assaults, the Russian threat group paired BeardShell with a heavily modified version of the initiating-provide Covenant .NET post-exploitation framework.
The modifications they introduced consist of deterministic implant identifiers tied to host traits, modified execution waft to evade behavioral detection, and contemporary cloud-based mostly dialog protocols.
Since July 2025, the threat actor has aged the Filen cloud provider with Covenant. Previously, the attacker aged Koofr and pCloud services and products.
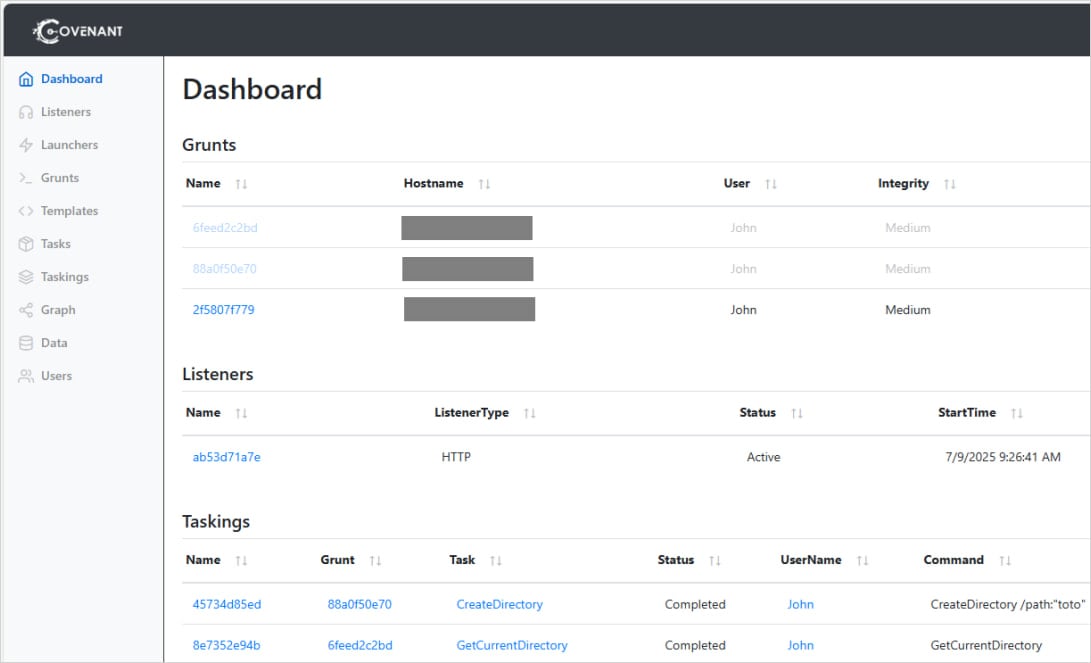
Provide: ESET
ESET says Covenant is aged as basically the most fundamental implant, and BearShell serves because the fallback instrument.
“Since 2023, Sednit developers private made a different of modifications and experiments with Covenant to construct it as their fundamental espionage implant, keeping BeardShell essentially as a fallback in case Covenant encounters operational disorders, such because the takedown of its cloud-based mostly infrastructure.” – ESET
ESET believes that APT28’s developed malware fashion crew returned to exercise in 2024, giving the threat group contemporary prolonged-term espionage capabilities. The technical similarities with 2010-technology malware recent continuity within the threat group’s fashion crew.
Cyber investigation Crimson File 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Crimson File 2026 shows how contemporary threats exercise math to detect sandboxes and screen in undeniable look.
Gain our diagnosis of 1.1 million malicious samples to reveal the highest 10 tactics and explore if your security stack is blinded.
Recent Posts
- US Sanctions Crypto Scams Community Linked to Cambodian Senator
- FBI Probes Theft of 15 Drones in NJ, Which Could maybe well Be Former in Chemical or Natural Weapon Assaults
- Roommate charged in deaths of two USF students
- Chicago sanatorium shooting leaves 2 officers injured, 1 seriously; suspect in custody: file
- Kevin Warsh’s Fed chair nomination advances as Powell investigation ends



