
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Hackers abuse .arpa DNS and ipv6 to evade phishing defenses

Mar
Hackers abuse .arpa DNS and ipv6 to evade phishing defenses
OSINT
Threat actors are abusing the particular-employ “.arpa” domain and IPv6 reverse DNS in phishing campaigns that extra without issue evade domain popularity checks and e-mail security gateways.
The .arpa domain is a thoroughly different high-stage domain reserved for net infrastructure in space of in vogue websites. It is a ways light for reverse DNS lookups, which enable programs to draw an IP handle support to a hostname.
IPv4 reverse lookups employ the in-addr.arpa domain, whereas IPv6 uses ip6.arpa. In these lookups, DNS queries a hostname derived from the IP handle, written in reverse issue and appended to without a doubt the type of domains.
To illustrate, www.google.com has the IP addresses 192.178.50.36 (IPv4) and 2607:f8b0:4008:802::2004 (IPv6). Querying Google’s IP of 192.178.50.36 throughout the dig instrument resolves to an in-addr.arpa hostname and within the extinguish a in vogue hostname:
; <<>> DiG 9.18.39-0ubuntu0.24.04.2-Ubuntu <<>> -x 192.178.50.36
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 59754
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;36.50.178.192.in-addr.arpa. IN PTR
;; ANSWER SECTION:
36.50.178.192.in-addr.arpa. 1386 IN PTR lcmiaa-aa-in-f4.1e100.net.
;; Query time: 7 msec
;; SERVER: 127.0.0.1#53(127.0.0.1) (UDP)
;; WHEN: Fri Mar 06 13:57:31 EST 2026
;; MSG SIZE rcvd: 94Querying Google's IPv6 handle of 2607:f8b0:4008:802::2004 reveals that it first resolves to an IPv6.arpa hostname after which a hostname, as shown below.
; <<>> DiG 9.18.39-0ubuntu0.24.04.2-Ubuntu <<>> -x 2607:f8b0:4008:802::2004
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 31116
;; flags: qr rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. IN PTR
;; ANSWER SECTION:
4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. 78544 IN PTR tzmiaa-af-in-x04.1e100.net.
4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. 78544 IN PTR mia07s48-in-x04.1e100.net.
;; Query time: 10 msec
;; SERVER: 127.0.0.1#53(127.0.0.1) (UDP)
;; WHEN: Fri Mar 06 13:58:43 EST 2026
;; MSG SIZE rcvd: 171OSINT Phishing campaign abuses in .arpa domains
A phishing campaign seen by Infoblox uses the ip6.arpa reverse DNS TLD, which assuredly maps IPv6 addresses support to hostnames the employ of PTR recordsdata.
Nevertheless, attackers stumbled on that if they reserve their hang IPv6 handle space, they will abuse the reverse DNS zone for the IP vary by configuring further DNS recordsdata for phishing websites.
In in vogue DNS functionality, reverse DNS domains are light for PTR recordsdata, which enable programs to opt the hostname related to a queried IP handle.
Nevertheless, attackers stumbled on that after they gained put watch over over the DNS zone for an IPv6 vary, some DNS management platforms allowed them to configure thoroughly different yarn forms that can also simply furthermore be abused for phishing attacks.
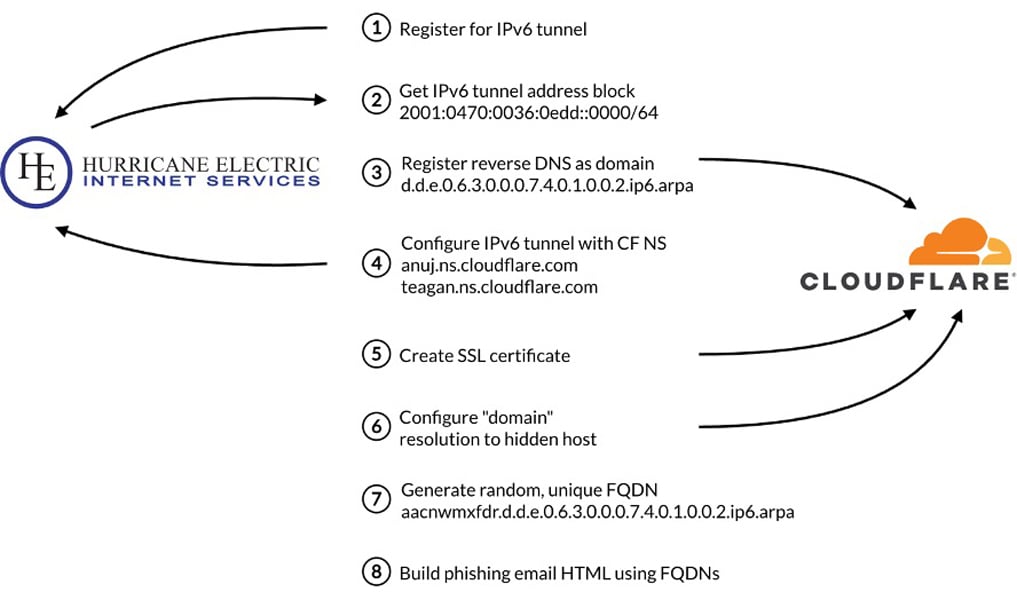
"We have seen threat actors abuse Hurricane Electric and Cloudflare to create these records—both of which have good reputations that actors leverage—and we confirmed that some other DNS providers also allow these configurations," explains Infoblox.
"Our tests were not exhaustive, but we notified the providers where we discovered a gap. Figure 2 depicts the process the threat actor used to create the domain used in the phishing emails."
To diagram up the infrastructure, the attackers first obtained a block of IPv6 addresses through IPv6 tunneling companies and products.
Offer: Infoblox
After gaining put watch over of the handle space, the attackers then generate reverse DNS hostnames from the IPv6 handle vary the employ of randomly generated subdomains which would be advanced to detect or block.
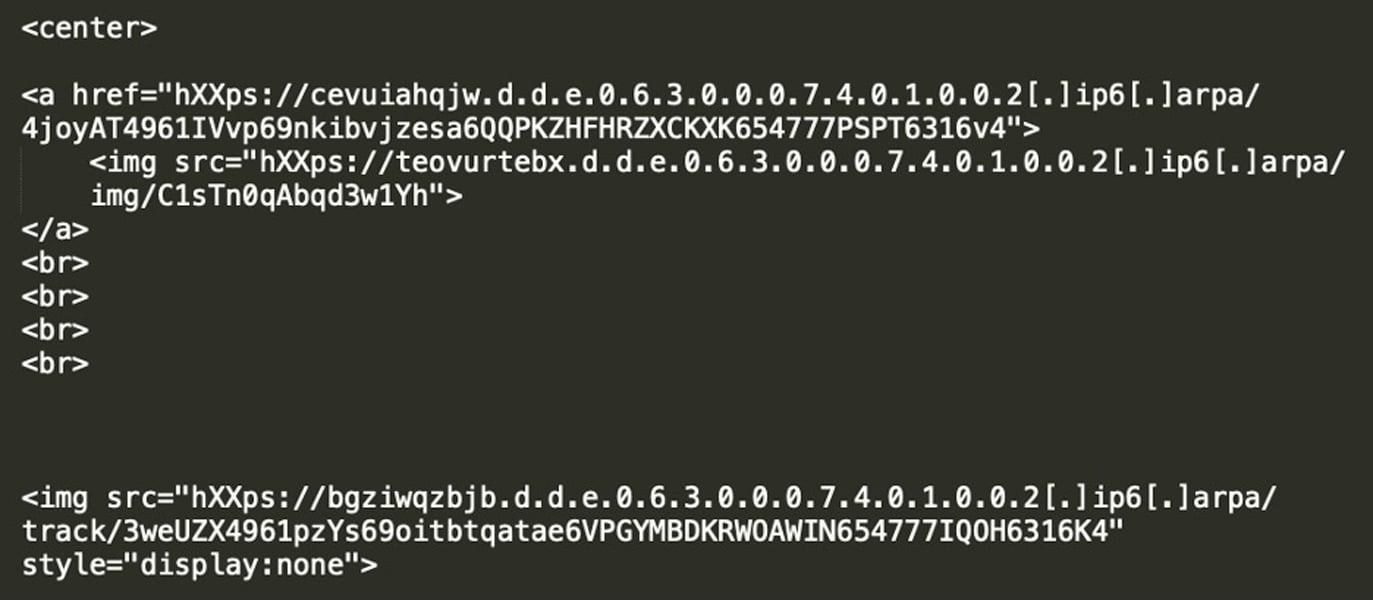
Relatively than configuring PTR recordsdata as expected, the attackers salvage A recordsdata that level these reverse DNS domains to infrastructure net hosting phishing websites.
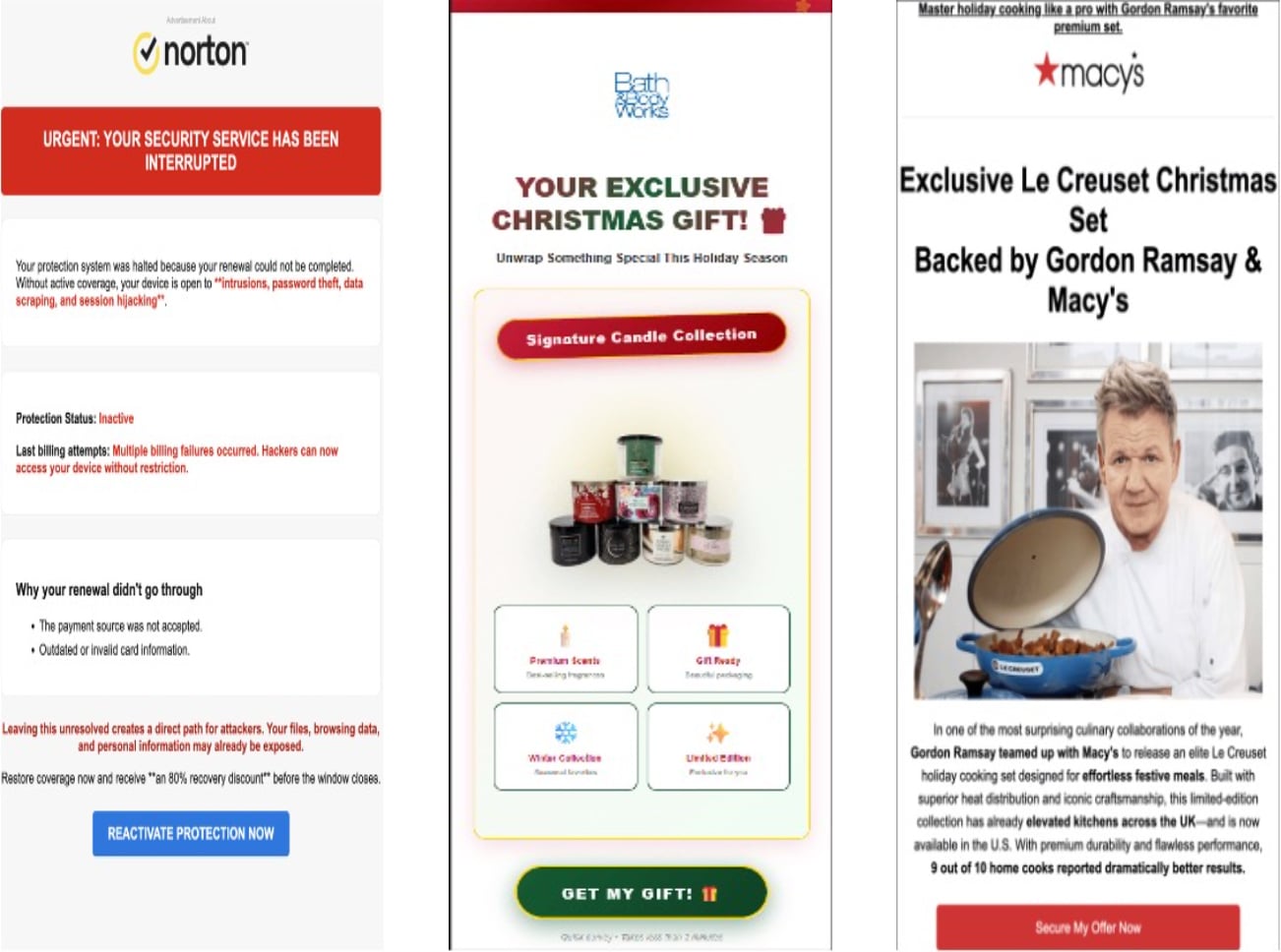
The phishing emails on this campaign employ lures that promise a prize, a survey reward, or an myth notification. The lures are embedded within the emails as images linked to a reverse IPv6 DNS yarn, corresponding to "d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa," in space of a in vogue hostname, so the goal would no longer survey a outlandish arpa hostname.
Offer: Infoblox
When a victim clicks the phishing e-mail image, the instrument resolves the attacker-managed reverse DNS name servers through a DNS provider.
Offer: Infoblox
In some cases, the authoritative name servers salvage been hosted by Cloudflare, and the reverse DNS domains resolved to Cloudflare IP addresses, hiding the placement of the backend phishing infrastructure.
After clicking the image, victims are redirected through a web page online visitors distribution plan (TDS) that determines whether or no longer they are a sound goal, many times in holding with instrument form, IP handle, web referers, and thoroughly different standards. If the visitor passes validation, they are redirected to a phishing space. Otherwise, they are despatched to a legitimate web page material.
Infoblox says the phishing hyperlinks are instant-lived, most efficient intelligent for just a few days. After the hyperlinks expire, they redirect customers to domain errors or thoroughly different legitimate websites.
The researchers factor in this is finished to make it more difficult for security researchers to analyze and examine the phishing campaign.
Furthermore, because the '.arpa' domain is reserved for net infrastructure, it would no longer consist of recordsdata assuredly show in registered domains, corresponding to WHOIS recordsdata, domain age, or contact recordsdata. This makes it more difficult for e-mail gateways and security instruments to detect malicious domains.
The researchers also seen the phishing campaign the employ of thoroughly different tactics, corresponding to hijacking dangling CNAME recordsdata and subdomain shadowing, permitting the attackers to push phishing swear material through subdomains linked to legitimate organizations.
"We found over 100 instances where the threat actor used hijacked CNAMEs of well-known government agencies, universities, telecommunication companies, media organizations, and retailers," defined Infoblox.
By weaponizing trusted reverse DNS substances light by security instruments, attackers can generate phishing URLs that bypass light detection ideas.
As repeatedly, essentially the most efficient method to keep away from phishing attacks adore these is to keep away from clicking on unexpected hyperlinks in emails and as a replacement focus on over with companies and products without prolong through their decent websites.
OSINT Red Document 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Document 2026 unearths how modern threats employ math to detect sandboxes and conceal in shocking glimpse.
Gain our evaluation of 1.1 million malicious samples to issue the stop 10 tactics and survey in case your security stack is blinded.
Recent Posts
- Web Novel Series ‘Got Dropped Into a Ghost Memoir, Easy Gotta Work’ Will get Webtoon Adaptation
- FBI fires diverse analysts tied to disputed ‘Catholic ideology’ memo
- Kash Patel Reveals Dazzling FBI Crackdown: 7,200 Childhood Rescued, 3,400 Predators Nabbed
- Florida police piece final file on Hulk Hogan’s reason at the again of demise
- Serious Everest Forms Skilled flaw exploited to lift over WordPress sites



