
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Chinese language affirm hackers target telcos with quiet malware toolkit

Mar
Chinese language affirm hackers target telcos with quiet malware toolkit
Cybersecurity expert

A China-linked improved chronic threat actor tracked as UAT-9244 has been concentrated on telecommunication service suppliers in South The USA since 2024, compromising Windows, Linux, and community-edge gadgets.
In accordance to Cisco Talos researchers, the adversary is intently associated with the FamousSparrow and Tropic Trooper hacker teams, nonetheless is tracked as a separate exercise cluster.
This evaluation has excessive self assurance and is in accordance to identical tooling, tactics, techniques, and procedures (TTPs), and victimology seen in attacks attributed to the threat actors.
The researchers point out that while UAT-9244 shares the identical target profile as Salt Storm, they may perhaps perhaps unbiased no longer attach a solid connection between the two exercise clusters.
Unusual malware concentrated on telco networks
The researchers learned that the promoting campaign light three beforehand undocumented malware households: TernDoor, a Windows backdoor; PeerTime, a Linux backdoor that makes exercise of BitTorrent; and BruteEntry, a brute-force scanner that builds proxy infrastructure (ORBs).
TernDoor is deployed via DLL facet-loading, the utilization of the respectable executable wsprint.exe to load malicious code from BugSplatRc64.dll, which decrypts and executes the closing payload in memory (injected into msiexec.exe).
The malware contains an embedded Windows driver, WSPrint.sys, which is light to discontinuance, suspend, and resume processes.
Persistence is performed by design of scheduled tasks and Windows Registry adjustments, that are additionally light to masks the scheduled project.
Additionally, TernDoor can attain instructions by design of distant shell, escape arbitrary processes, be taught/write recordsdata, bag system knowledge, and self-uninstall.
PeerTime is an ELF Linux backdoor that targets quite loads of architectures (ARM, AARCH, PPC, MIPS), suggesting it used to be designed to compromise a plentiful range of embedded programs and community gadgets light in telecom environments.

Source: Cisco Talos
Cisco Talos documented two versions for PeerTime. One variant is written in C/C++ and the assorted is in accordance to Rust. The researchers additionally noticed Simplified Chinese language debug strings in the instrumentor binary, a trademark of its origin.
Its payload is decrypted and loaded in memory, and its job is renamed to appear respectable.
PeerTime, an ELF-basically based utterly mostly glance-to-glance (P2P) backdoor, makes exercise of the BitTorrent protocol for deliver-and-control (C2) communications, downloads and executes payloads from peers, and makes exercise of BusyBox to jot down the recordsdata on the host.
At last, there’s BruteEntry, which includes a Plod-basically based utterly mostly instrumentor binary and a brute-forcing part. Its position is to turn compromised gadgets into scanning nodes, identified as Operational Relay Bins (ORBs).
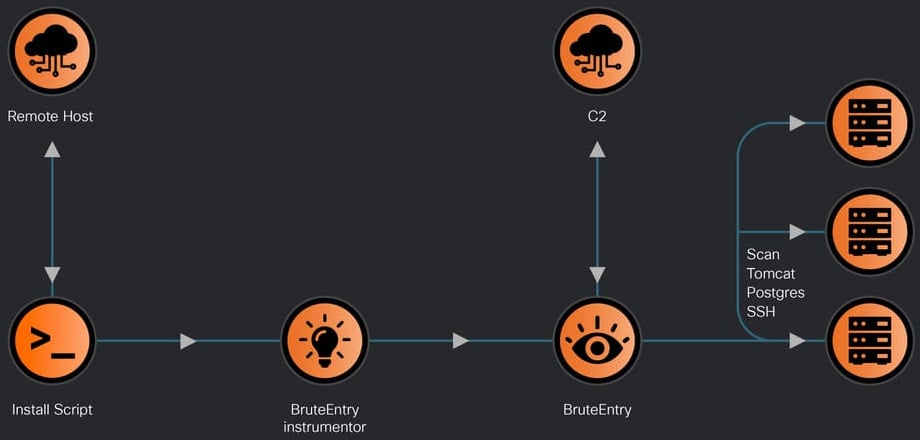
Source: Cisco Talos
The attacker makes exercise of the machines working BruteEntry to scan for stamp spanking quiet targets and brute-force gather admission to to SSH, Postgres, and Tomcat. Login strive outcomes are despatched serve to the C2 with project location and notes.
In a technical list this day, Cisco Talos researchers present info on the capabilities of the three objects of malware, how they’re deployed, and assemble persistence.
Cisco Talos researchers have listed indicators of compromise (IoCs) associated with the seen UAT-9244 exercise, which defenders can exercise to detect and block these attacks early.
Cybersecurity expert Crimson List 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Crimson List 2026 exhibits how quiet threats exercise math to detect sandboxes and masks in horrid gape.
Receive our analysis of 1.1 million malicious samples to whisper the head 10 techniques and observe if your security stack is blinded.
Recent Posts
- Battery thriller hangs over dominant Mercedes marketing campaign
- Experiences: NCAA rejects Texas Tech’s allure to reinstate Sorsby – ESPN
- DOJ put of enterprise says ‘just a few’ probes of California elections underway after Trump cries depraved
- U.S. lawyer opens investigations into California’s elections, sends prosecutor to LA vote heart
- Clippers star Kawhi Leonard, proprietor Steve Ballmer interviewed for position in Aspiration scandal


