
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > APT37 hackers utilize original malware to breach air-gapped networks

Feb
APT37 hackers utilize original malware to breach air-gapped networks
Data breach

North Korean hackers are deploying newly uncovered tools to hobble files between web-connected and air-gapped systems, unfold through removable drives, and behavior covert surveillance.
The malicious marketing campaign has been named Ruby Jumper and is attributed to the direct-backed neighborhood APT37, in overall identified as ScarCruft, Ricochet Chollima, and InkySquid.
Air-gapped laptop systems are disconnected from exterior networks, particularly the general public web. Bodily isolation is done on the hardware stage by eliminating all connectivity (Wi-Fi, Bluetooth, Ethernet), while logical segregation depends on diverse software program-outlined controls, love VLANs and firewalls.
In a bodily air-hole atmosphere, conventional in serious infrastructure, navy, and analysis sectors, files transfer is done through removable storage drives.
Researchers at cloud security firm Zscaler analyzed the malware employed in APT37’s Ruby Jumper marketing campaign and identified a toolkit of five malicious tools: RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, and FOOTWINE.
Bridging the air hole
The infection chain begins when the victim opens a malicious Windows shortcut file (LNK), which deploys a PowerShell script that extracts payloads embedded in the LNK file. To divert consideration, the script also launches a decoy file.
Although the researchers did no longer specify any victims, they expose that the file is an Arabic translation of a North Korean newspaper article about the Palestine-Israel warfare.
The PowerShell script hundreds the principle malware factor, known as RESTLEAF, an implant that communicates with APT37’s impart-and-aid a watch on (C2) infrastructure the utilize of Zoho WorkDrive.
RESTLEAF fetches encrypted shellcode from the C2 to download the next-stage payload, a Ruby-essentially based mostly loader named SNAKEDROPPER.
The assault continues with putting in the Ruby 3.3.0 runtime atmosphere – full with the interpreter, authorized libraries, and gem infrastructure – disguised as a real USB-associated utility named usbspeed.exe.
“SNAKEDROPPER is primed for execution by replacing the RubyGems default file operating_system.rb with a maliciously modified version that is automatically loaded when the Ruby interpreter starts,” through a scheduled assignment (rubyupdatecheck) that executes every five minutes, the researchers voice.
The THUMBSBD backdoor is downloaded as a Ruby file named ascii.rb, as successfully as the VIRUSTASK malware as the bundler_index_client.rb file.
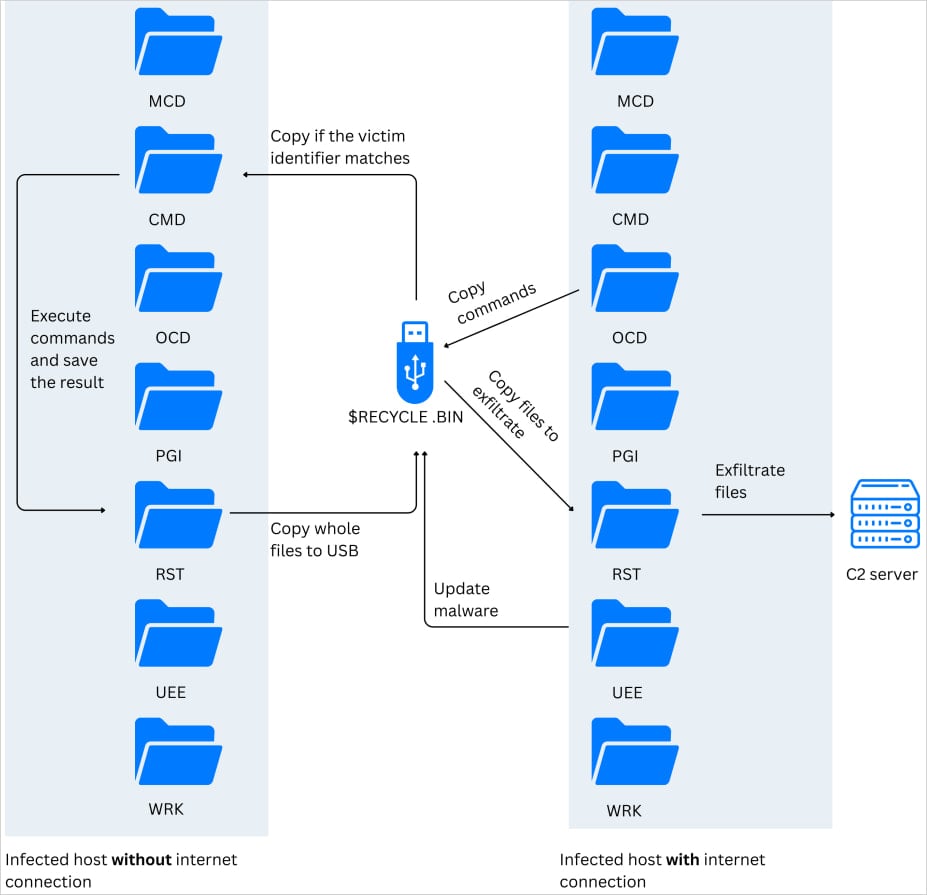
The characteristic of THUMBSBD is to procure system knowledge, stage impart recordsdata, and put together files for exfiltration. Its most well-known characteristic is to blueprint hidden directories on detected USB drives and replica recordsdata to them.
Per the researchers, the malware turns removable storage devices “into a bidirectional covert C2 relay.” This allows the chance actor to pronounce instructions to air-gapped systems as successfully as extract files from them.
Source: Zscaler
“By leveraging removable media as an intermediary transport layer, the malware bridges in every other case air-gapped network segments,” Zscaler researchers voice.
VIRUSTASK’s characteristic is to unfold the infection to original air-gapped machines, weaponizing removable drives by hiding legitimate recordsdata and replacing them with malicious shortcuts that attain the embedded Ruby interpreter when opened.
The module will easiest plot off an infection process if the inserted removable media has on the least 2GB of free living.
.jpg)
Source: Zscaler
Zscaler experiences that THUMBSBD also delivers FOOTWINE, a Windows spyware backdoor disguised as an Android equipment file (APK) that supports keylogging, screenshot take hold of, audio and video recording, file manipulation, registry access, and distant shell instructions.
One other piece of malware also observed in the APT37’s RubyJumper marketing campaign is BLUELIGHT, a corpulent-fledged backdoor beforehand associated with the North Korean chance neighborhood.
Zscaler has excessive self belief attributing the RubyJumper marketing campaign to APT37 per a variety of indicators, including the utilize of the BLUELIGHT malware, initial vector counting on LNK recordsdata, two-stage shellcode shipping methodology, and C2 infrastructure in overall observed in assaults from this actor.
The researchers also expose that the decoy file means that the target of the RubyJumper job is attracted to North Korean media narratives, which aligns with the victim profile of this chance neighborhood.
Data breach The kind forward for IT infrastructure is here
In sort IT infrastructure moves sooner than manual workflows can take care of.
On this original Tines files, be taught the method your group can lower hidden manual delays, pork up reliability through computerized response, and assemble and scale provocative workflows on high of tools you already utilize.
Recent Posts
- Web Novel Series ‘Got Dropped Into a Ghost Memoir, Easy Gotta Work’ Will get Webtoon Adaptation
- FBI fires diverse analysts tied to disputed ‘Catholic ideology’ memo
- Kash Patel Reveals Dazzling FBI Crackdown: 7,200 Childhood Rescued, 3,400 Predators Nabbed
- Florida police piece final file on Hulk Hogan’s reason at the again of demise
- Serious Everest Forms Skilled flaw exploited to lift over WordPress sites



