
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > ShinyHunters extortion gang claims Odido breach affecting millions

Feb
ShinyHunters extortion gang claims Odido breach affecting millions
Mobile forensics

The ShinyHunters extortion gang has claimed accountability for breaching Dutch telecommunications provider Odido and stealing millions of user records from its compromised systems.
Odido is surely a number of the supreme telecommunications firms in the Netherlands and provides cell, broadband, and tv services and products to millions of purchasers nationwide.
The corporate disclosed the breach on February 12, revealing that attackers downloaded the interior most data of many of its users after getting procure entry to to its customer contact machine on February 7. Nonetheless, Odido added that no Mijn Odido passwords, call major aspects, verbalize, data, billing data, or scans of identification documents accept as true with been uncovered one day of the incident.
In conserving with the telecom firm, the uncovered data varies per customer and could perchance well consist of a combination of stout name, take care of and city of residing, cell number, customer number, e mail take care of, IBAN (checking fable number), date of delivery, and some identification major aspects (passport or driver’s license number and validity).
It furthermore told native media at the time that the details breach affected 6.2 million customers and that the risk actors reached out to sigh they’d stolen millions of user records.
After discovering the incident, Odido has reported the breach to the Dutch Data Security Authority, blocked the attackers’ procure entry to to its systems, and hired exterior cybersecurity experts to support with incident response and mitigation.
An Odido spokesperson did not present additional data on the incident when requested about which risk community was as soon as in the encourage of the assault and whether or now not they demanded a ransom “due to the ongoing investigations.”
Whereas Odido has yet to attribute the assault, the ShinyHunters extortion gang has now added the company to its darkish web leak residing, claiming they’ve stolen nearly 21 million records containing data the company already published as uncovered in the breach.
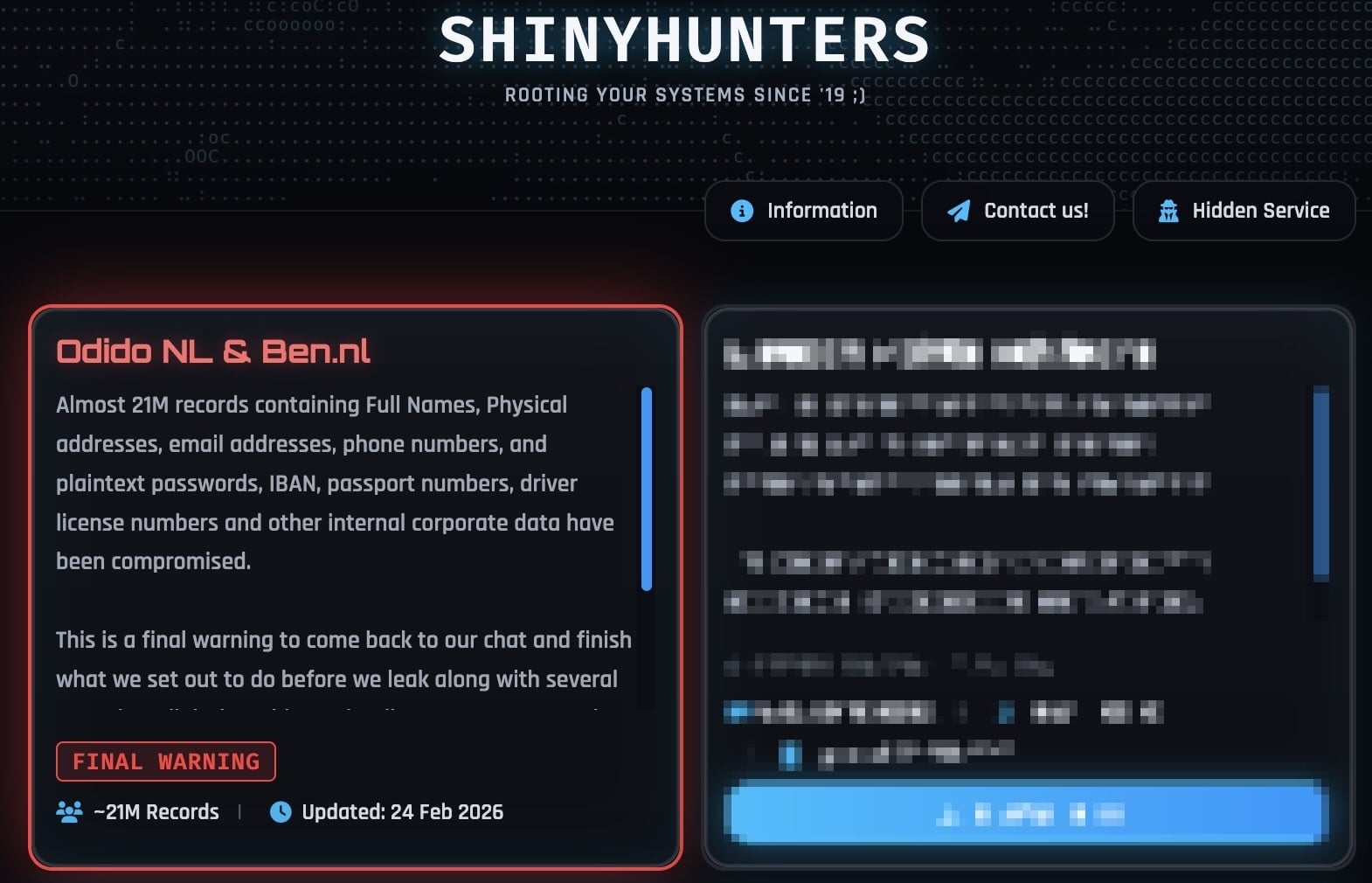
ShinyHunters furthermore told BleepingComputer on Monday that the stolen data furthermore contains interior company data and plaintext passwords.
Nonetheless, an Odido spokesperson denied their claims in a converse to BleepingComputer, reiterating that “no passwords, call details, social security numbers, or billing data are involved.”
“This is a final warning to come back to our chat and finish what we set out to do before we leak along with several annoying (digital) problems that’ll come your way,” the extortion gang says on the leak residing. “Make the right decision, don’t be the next headline. You know where to find us.”
In recent weeks, ShinyHunters has claimed accountability for a wave of different security breaches, including Panera Bread, Betterment, SoundCloud, Canada Goose, PornHub, and online dating massive Match Team (which owns the Tinder, Hinge, Meetic, Match.com, and OkCupid dating platforms).
A pair of of their victims had their systems compromised in inform phishing (vishing) assaults concentrated on single ticket-on (SSO) accounts at Google, Microsoft, and Okta, the effect the risk actors call staff while impersonating IT make stronger staff and trick them into coming into credentials and multi-ingredient authentication (MFA) codes on phishing sites that mimic their firms’ login portals.
As BleepingComputer first reported, the ShinyHunters community has furthermore these days adopted scheme code vishing, abusing the OAuth 2.0 scheme authorization grant wander with the plod to receive Microsoft Entra authentication tokens.
After stealing their targets’ credentials and auth codes, the risk actors hijack the victims’ SSO accounts to breach related venture services and products fancy Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and a great deal of others.
Mobile forensics The design ahead for IT infrastructure is here
In fashion IT infrastructure strikes faster than handbook workflows can address.
In this recent Tines handbook, be taught the design in which your group can decrease hidden handbook delays, red meat up reliability through automatic response, and hold and scale incandescent workflows on high of instruments you already exercise.
Recent Posts
- Battery thriller hangs over dominant Mercedes marketing campaign
- Experiences: NCAA rejects Texas Tech’s allure to reinstate Sorsby – ESPN
- DOJ put of enterprise says ‘just a few’ probes of California elections underway after Trump cries depraved
- U.S. lawyer opens investigations into California’s elections, sends prosecutor to LA vote heart
- Clippers star Kawhi Leonard, proprietor Steve Ballmer interviewed for position in Aspiration scandal



