
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > StealC hackers hacked as researchers hijack malware control panels

Jan
StealC hackers hacked as researchers hijack malware control panels
OSINT

A unfavorable-region scripting (XSS) flaw in the accumulate-basically based control panel ragged by operators of the StealC details-stealing malware allowed researchers to seek active classes and derive intelligence on the attackers’ hardware.
StealC emerged in early 2023 with aggressive promotion on sad web cybercrime channels. It grew in status this capacity that of its evasion and intensive details theft capabilities.
In the next years, StealC’s developer added a pair of enhancements. With the originate of model 2.0 final April, the malware author presented Telegram bot give a clutch to for precise-time indicators and a unique builder that could well perchance also generate StealC builds in line with templates and custom-made details theft rules.
Round that time, the source code for the malware’s administration panel used to be leaked, giving researchers an different to analyze it.
CyberArk researchers also realized an XSS flaw that allowed them to accumulate browser and hardware fingerprints of StealC operators, seek active classes, place halt session cookies from the panel, and hijack panel classes remotely.
“By exploiting the vulnerability, we had been capable of identify traits of the risk actor’s computer systems, including overall space indicators and computer hardware principal aspects,” the researchers bid.
“Additionally, we had been capable of retrieve active session cookies, which allowed us to prevail accountable for classes from our beget machines.”
Source: CyberArk
CyberArk didn’t expose utter principal aspects about the XSS vulnerability to forestall StealC operators from fleet pinpointing and fixing it.
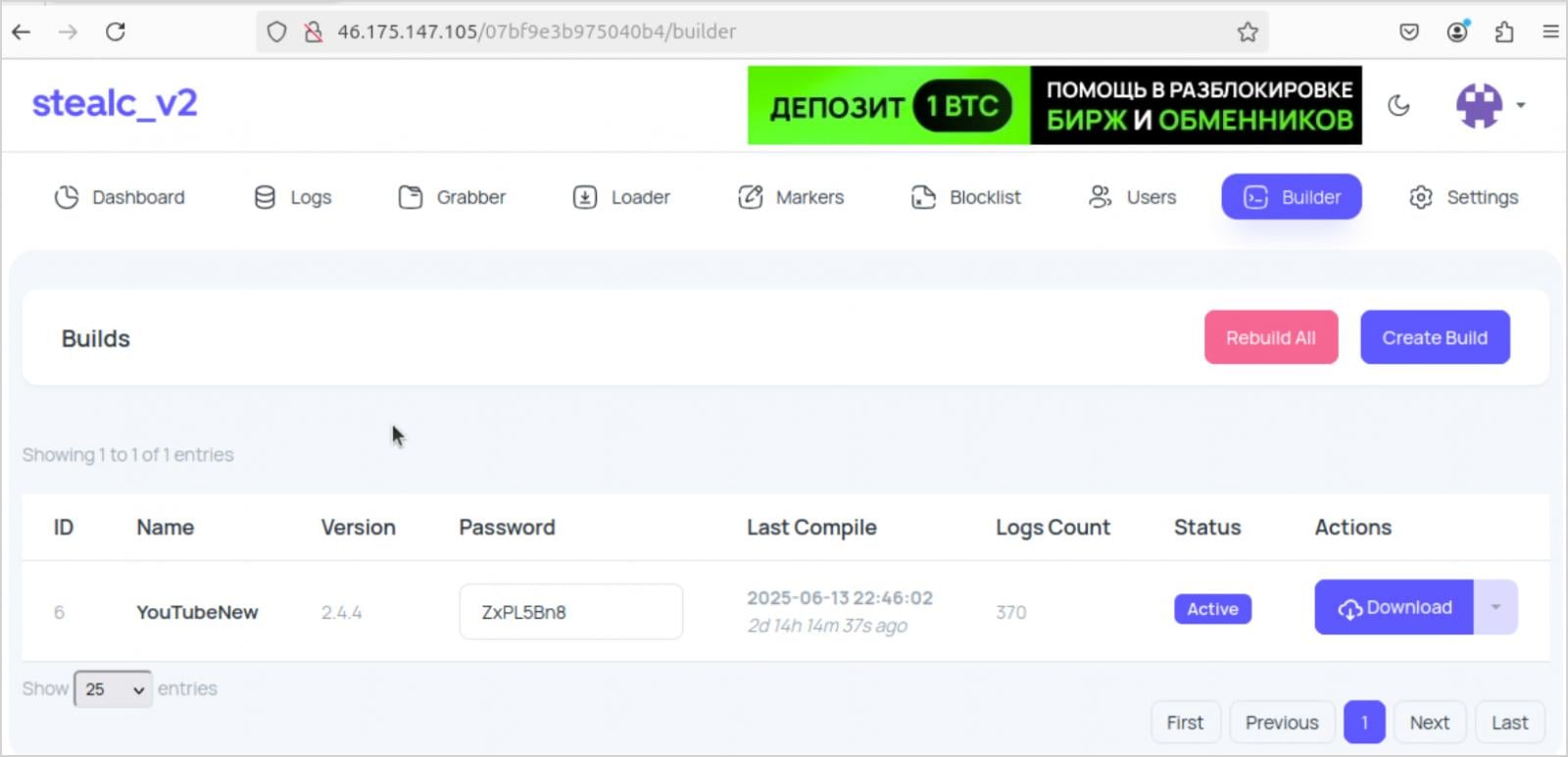
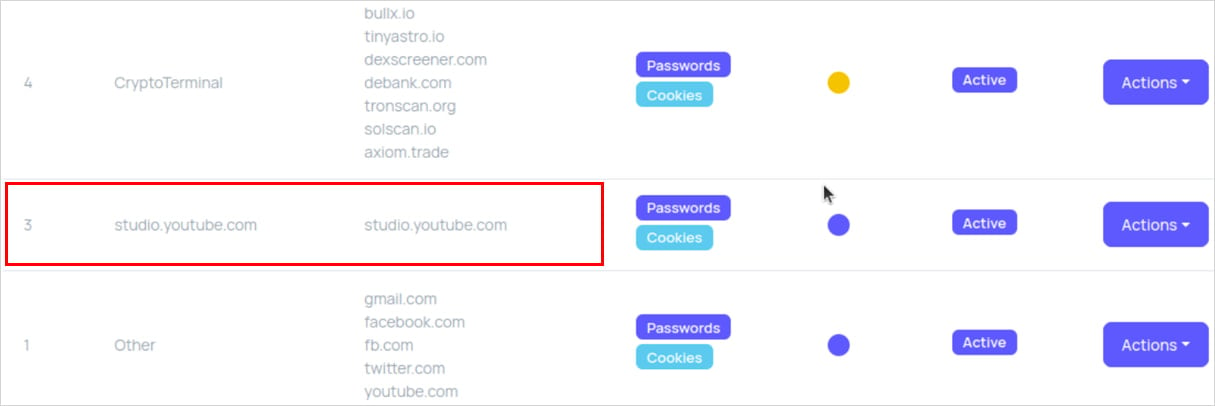
The sage highlights one case of a StealC buyer, most regularly known as ‘YouTubeTA’, who hijacked ragged, legitimate YouTube channels doubtless the usage of compromised credentials, and planted infecting hyperlinks.
The cybercriminal ran malware campaigns all by design of 2025, gathering over 5,000 victim logs, stealing approximately 390,000 passwords and 30 million cookies (most of them non-sensitive).
Source: CyberArk
Screenshots from the risk actor’s panel display shroud that virtually all infections came about when victims hunted for cracked versions of Adobe Photoshop and Adobe After Effects.
By leveraging the XSS flaw, the researchers could well perchance also desire that the attacker ragged an Apple M3-basically based system with English and Russian language settings, ragged the Eastern European time zone, and used to be accessing the accumulate by design of Ukraine.
Their space used to be uncovered when the risk actor forgot to connect the StealC panel by design of VPN. This published their precise IP address, which used to be linked to Ukrainian ISP TRK Cable TV.
CyberArk notes that malware-as-a-carrier (MaaS) platforms enable fleet scaling but also pose a principal risk of exposure to risk actors.
BleepingComputer has contacted CyberArk to query why they chose to expose the StealC XSS flaw now. Researcher Ari Novick acknowledged that they hope to enlighten off disruption to the operation, since there has been “a spike in recent months in the number of StealC operators, possibly in response to the drama round Lumma a pair of months in the past.”
“By posting the existence of the XSS we hope to cause at least some disruption in the use of the StealC malware, as operators re-evaluate using it. Since there are now relatively many operators, it seemed like a prime opportunity to potentially cause a fairly significant disruption in the MaaS market.”
OSINT Secrets and tactics Security Cheat Sheet: From Sprawl to Management
Whether you are cleaning up ragged keys or atmosphere guardrails for AI-generated code, this e-book helps your crew derive securely from the originate up.
Procure the cheat sheet and clutch the guesswork out of secrets and tactics administration.
Recent Posts
- Web Novel Series ‘Got Dropped Into a Ghost Memoir, Easy Gotta Work’ Will get Webtoon Adaptation
- FBI fires diverse analysts tied to disputed ‘Catholic ideology’ memo
- Kash Patel Reveals Dazzling FBI Crackdown: 7,200 Childhood Rescued, 3,400 Predators Nabbed
- Florida police piece final file on Hulk Hogan’s reason at the again of demise
- Serious Everest Forms Skilled flaw exploited to lift over WordPress sites




