![‘Will Trent’ Big name Breaks Silence After [Spoiler] Is Killed in Handsome Twist](https://forensicss.com/wp-content/uploads/2026/04/11020-will-trent-big-name-breaks-silence-after-spoiler-is-killed-in-handsome-twist-90x90.avif)
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Facebook login thieves now the use of browser-in-browser trick

Jan
Facebook login thieves now the use of browser-in-browser trick
Cyber investigation
Hackers over the past six months have relied increasingly on the browser-in-the-browser (BitB) diagram to trick users into offering Facebook story credentials.
The BitB phishing methodology used to be developed by security researcher mr.d0x in 2022. Cybercriminals later adopted it in assaults targeting diversified on-line companies and products, including Facebook and Steam.
Trellix researchers monitoring malicious process reveal that likelihood actors preserve end Facebook accounts to unfold scams, harvest internal most knowledge, or commit id fraud. With extra than three billion engrossing users, the social network is silent a top target for fraudsters.
In a BitB assault, users who search the advice of with attacker-managed webpages are provided with a faux browser pop-up containing a login produce.
The pop-up is utilized the use of an iframe that imitates the authentication interface of legit platforms and can be personalized with a window title and URL that form the deception extra inviting to detect.
In step with Trellix, most up to date phishing campaigns targeting Facebook users impersonate regulation firms claiming copyright infringement, threatening impending story suspension, or Meta security notifications about unauthorized logins.
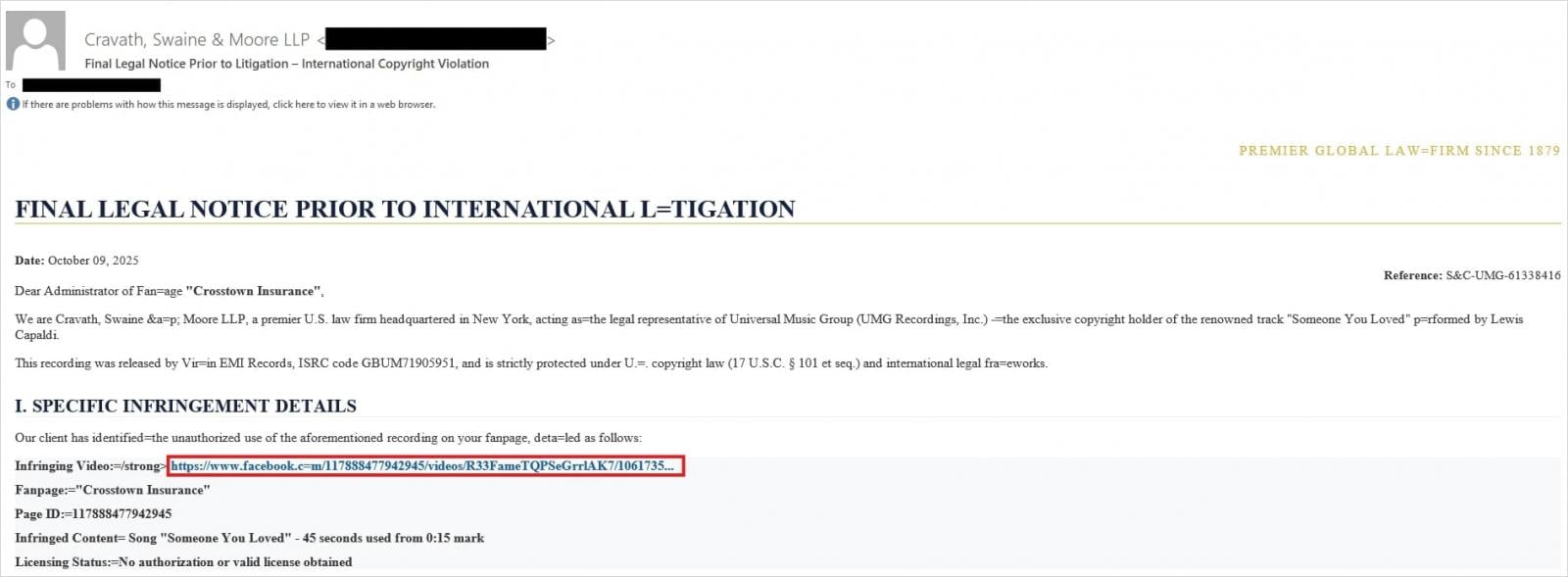
Offer: Trellix
To withhold a long way from detection and to amplify the sense of legitimacy, cybercriminals added shortened URLs and fake Meta CAPTCHA pages.
In the final stage of the assault, victims are prompted to log in by coming into their Facebook credentials in a faux pop-up window.
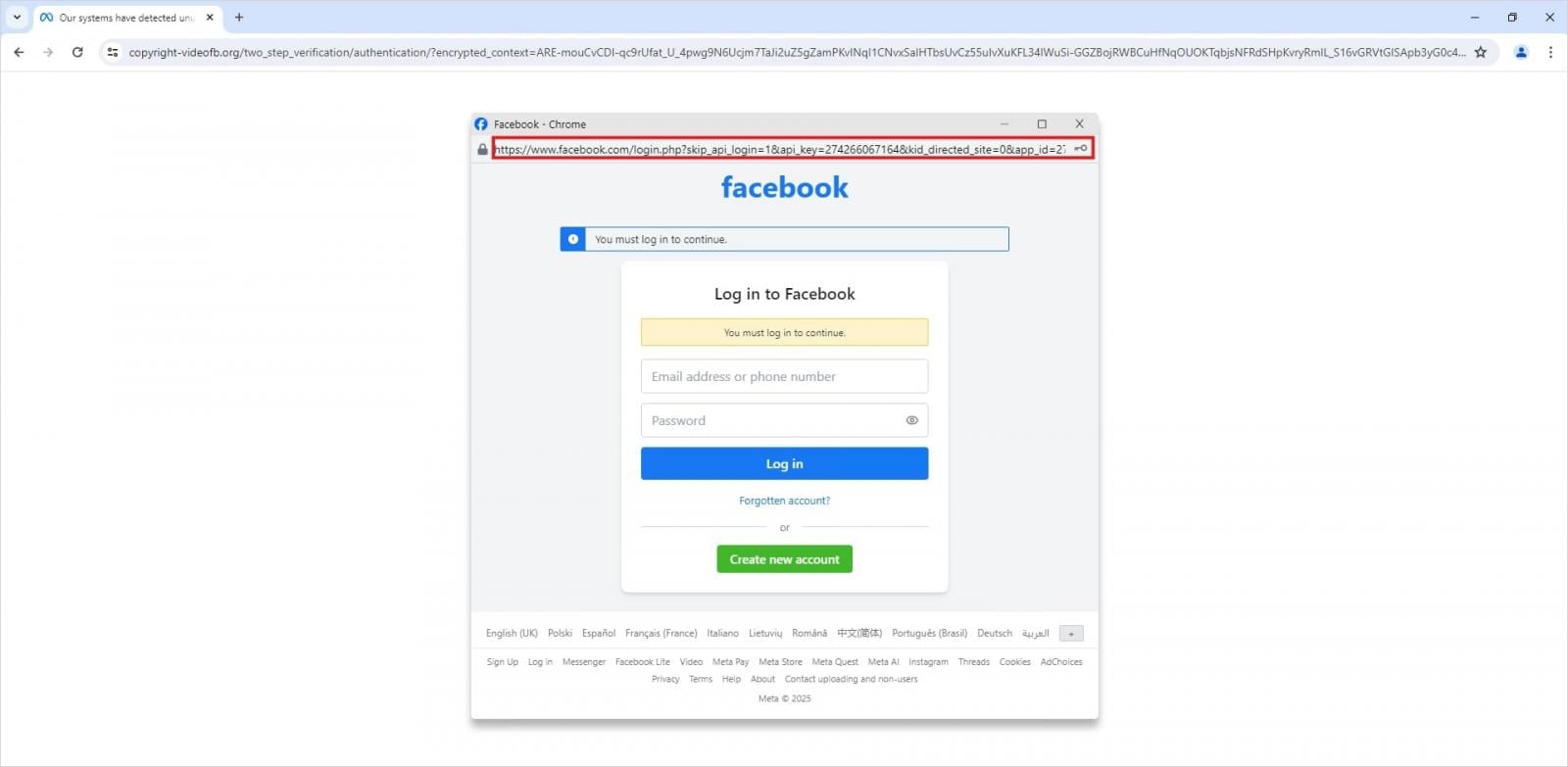
Offer: Trellix
In parallel, Trellix learned a high alternative of phishing pages hosted on legit cloud platforms like Netlify and Vercel, which mimic Meta’s Privateness Middle portal, redirecting users to pages disguised as appeal forms that aloof internal most knowledge.
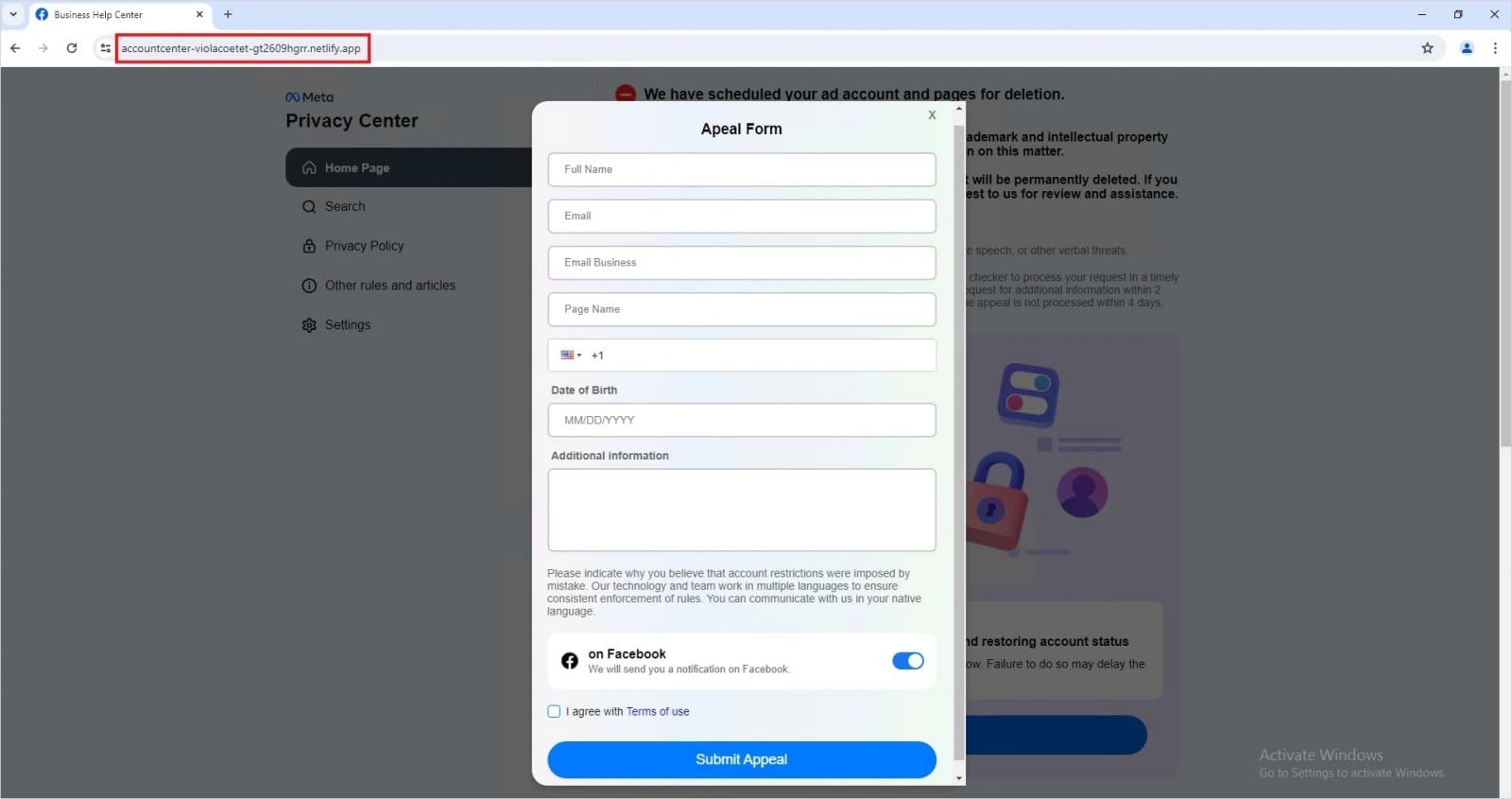
Offer: Trellix
These campaigns constitute a valuable evolution when when compared with typical Facebook phishing campaigns that security researchers in most cases behold.
“The key shift lies in the abuse of trusted infrastructure, utilizing legitimate cloud hosting services like Netlify and Vercel, and URL shorteners to bypass traditional security filters and lend a false sense of security to phishing pages,” reads the Trellix document.
“Most critically, the emergence of the Browser-in-the-Browser (BitB) technique represents a major escalation. By creating a custom-built, fake login pop-up window within the victim’s browser, this method capitalizes on user familiarity with authentication flows, making credential theft nearly impossible to detect visually.”
Cyber investigation How you would possibly provide protection to in opposition to BitM
When users salvage story-associated security alerts or infringement notifications, they favor to continuously navigate to the legitimate URL in a separate tab reasonably than following embedded links or buttons on the electronic mail itself.
When prompted to enter credentials in login pop-ups, take a look at if the window can switch exterior the browser window. iframes, that are valuable for the BitB trick, are associated to the underlying window and would per chance well no longer be pulled exterior it.
The final advice for holding entry to your on-line accounts is to flip on the two-ingredient authentication security characteristic. Though no longer infallible, this adds an further layer of security in opposition to story takeover makes an are trying even supposing credentials were compromised.
Cyber investigation 7 Safety Very top Practices for MCP
As MCP (Model Context Protocol) turns into the everyday for connecting LLMs to tools and knowledge, security teams are engrossing snappy to preserve these unique companies and products valid.
This free cheat sheet outlines 7 supreme practices you would possibly originate the use of as of late.
Recent Posts
- ‘Will Trent’ Big name Breaks Silence After [Spoiler] Is Killed in Handsome Twist
- UK Pastor Arrested, Imprisoned, Interrogated for Preaching in Public
- App host Vercel says it was hacked and customer records stolen
- Confronting gruesome allegations, FBI Director Kash Patel files original $250 million lawsuit
- We May possibly presumably perchance well Produce Worse Than Kash Patel Being a Drunken Buffoon




