
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Askul confirms theft of 740k buyer data in ransomware attack

Dec
Askul confirms theft of 740k buyer data in ransomware attack
Private eye

Jap e-commerce huge Askul Company has confirmed that RansomHouse hackers stole around 740,000 buyer data in the ransomware attack it suffered in October.
Askul is a wide change-to-change and change-to-user direct of job offers and logistics e-commerce firm owned by Yahoo! Japan Company.
The ransomware incident in October induced an IT system failure, forcing the firm to droop shipments to customers, including the retail huge Muji.
The investigations into the incident’s scope and impact personal now been concluded, and Askul says that the next forms of data has been compromised:
- Industry buyer carrier data: approx. 590,000 data
- Particular person buyer carrier data: approx. 132,000 data
- Industry partners (outsourcers, agents, suppliers): approx. 15,000 data
- Executives and workers (including personnel companies): approx. 2,700 data
Askul effectively-known that particular fundamental substances were withheld to forestall exploitation of the compromised data, and that affected customers and partners will seemingly be notified individually.
Moreover, the firm has knowledgeable the nation’s Non-public Recordsdata Protection Price regarding the tips exposure and established prolonged-duration of time monitoring to forestall misuse of the stolen data.
In the meantime, as of December 15, present shipping continues to be impacted, and the firm is aloof working to totally restore programs.
RansomHouse attack fundamental substances
The attack on Askul has been claimed by the RansomHouse extortion personnel. The gang before all the pieces disclosed the breach on October 30 and adopted up with two data leaks on November 10 and December 2.
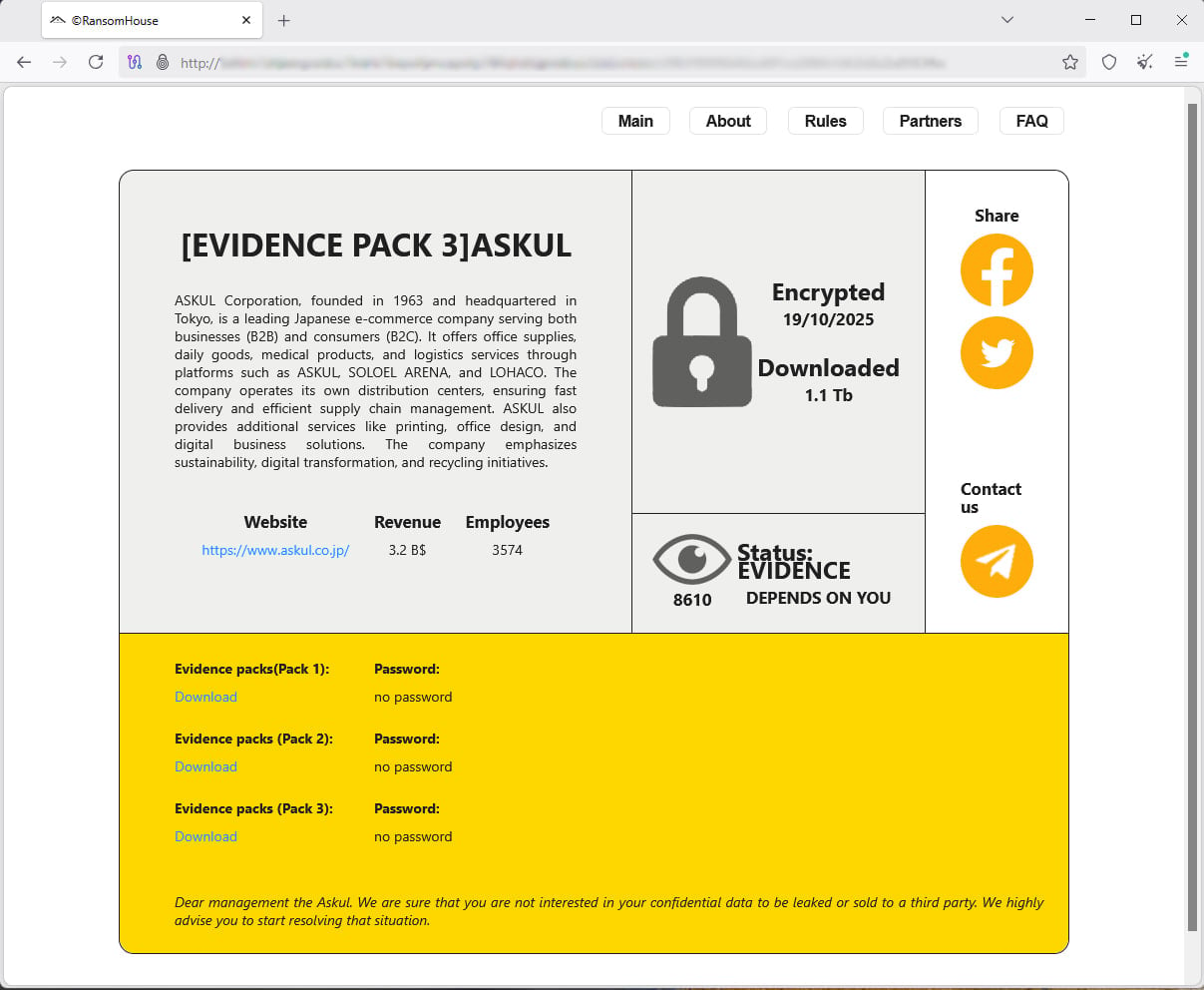
Source: BleepingComputer
Askul has shared some fundamental substances about how the threat actors breached its networks, estimating that they leveraged compromised authentication credentials for an outsourced partner’s administrator story, which lacked multi-component authentication (MFA) safety.
“After successfully achieving the initial intrusion, the attacker began reconnaissance of the network and attempted to collect authentication information to access multiple servers,” reads the computerized translation of Askul’s document.
“The attacker then disables vulnerability countermeasure software such as EDR, moves between multiple servers, and acquires the necessary privileges,” the firm mentioned.
Particularly, Askul acknowledged that multiple ransomware variants had been oldschool in the attack, some of which refrained from the EDR signatures that had been updated on the time.

Source: Askul
RansomHouse is identified for both stealing data and encrypting programs. Askul mentioned that the ransomware attack “resulted in data encryption and system failure.”
Askul stories that the ransomware payload used to be deployed concurrently all over multiple servers, whereas backup data had been wiped to forestall easy recovery.
In response, the firm physically disconnected contaminated networks and sever abet communications between data products and companies and logistics products and companies, isolated affected units, and updated EDR signatures.
Moreover, MFA used to be applied to all key programs, and all administrator accounts had their passwords reset.
The financial impact of the attack has not yet been estimated, and Askul has postponed its scheduled earnings document to enable extra time for an intensive financial review.
Private eye Destroy down IAM silos love Bitpanda, KnowBe4, and PathAI
Damaged IAM isn’t forever handsome an IT grief – the impact ripples all over all of your change.
This speedy-witted data covers why extinct IAM practices fail to protect with in style demands, examples of what “good” IAM looks love, and a easy pointers for constructing a scalable intention.
Tags
- Askul Confirms cybercrime cybersecurity email-fraud forensics|digital-forensics fraud Investigation malware online-scam online-scamphishing-attack private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker
Recent Posts
- Lawmakers name for federal investigation into gambling dysfunction
- James Comey: ‘Justice Can’t Be a Political Force’
- AI Is Handing Hackers Instruments That Once Belonged to Elite Attackers
- Of us Energy Rep collectively protests pollscarcity at Seoul polling stations
- Disabled ACR to your TV? I prepare a router-primarily based VPN for extra protection




