
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > cybersecurity > Canvas login portals hacked in mass ShinyHunters extortion marketing campaign

May
Canvas login portals hacked in mass ShinyHunters extortion marketing campaign
Scam detection

The ShinyHunters extortion gang has breached education abilities huge Instructure again, this time exploiting a vulnerability to deface Canvas login portals for a total bunch of colleges and universities.
The defacements, that were seen for roughly half-hour earlier than being taken offline, displayed a message from ShinyHunters claiming responsibility for the earlier Instructure breach and threatening to leak stolen info if a ransom is now not paid.
The message warns that Instructure and colleges earn till May perchance well perchance 12 to contact them to negotiate a ransom, or students’ info will almost definitely be leaked.
“ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some ‘security patches’,” reads the defacement.
“If any of the schools in the affected list are interested in preventing the release of their data, please consult with a cyber advisory firm and contact us privately at TOX to negotiate a settlement. You have till the end of the day by May 12 2026 before everything is leaked,” endured the message.
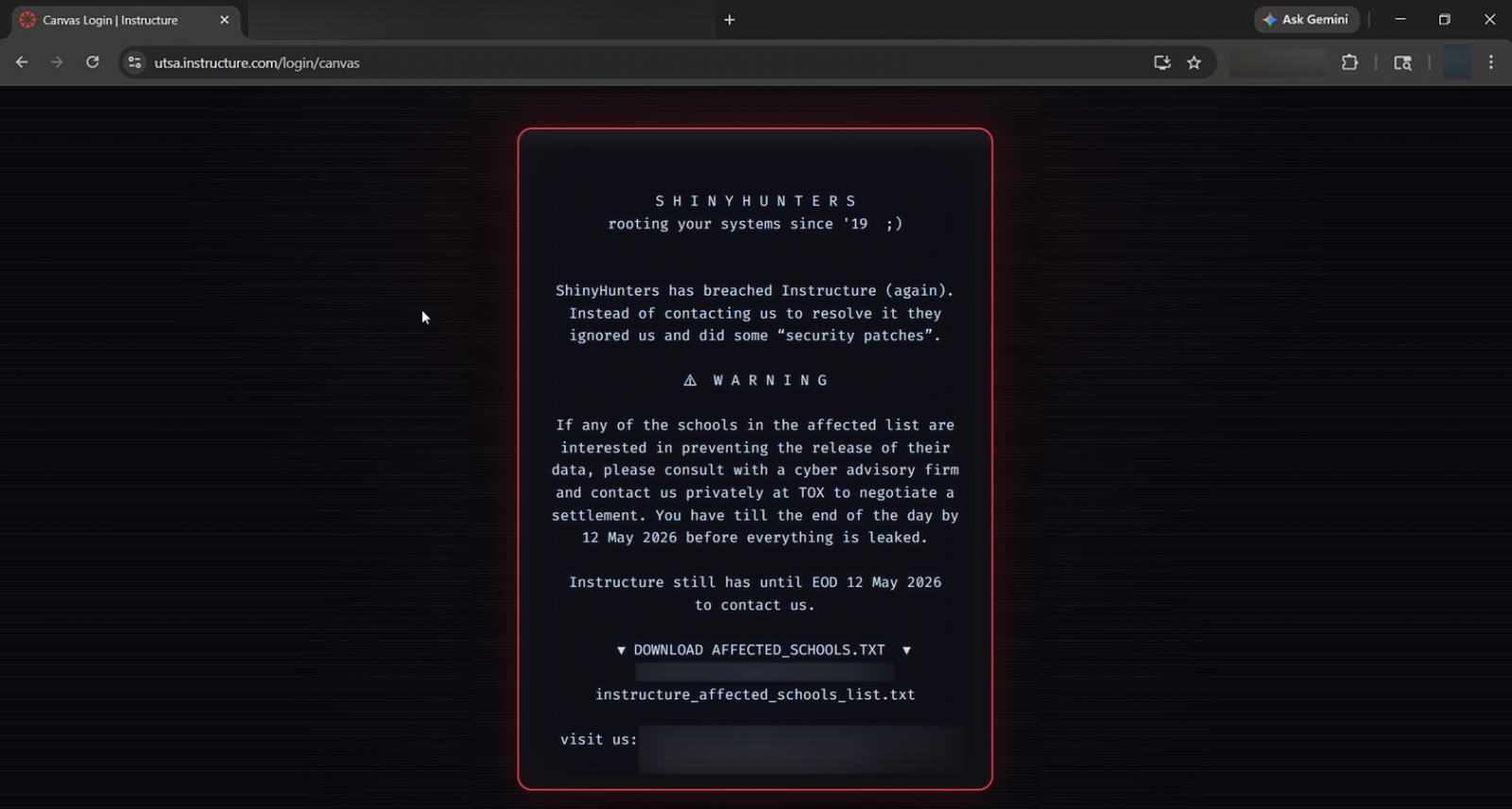
BleepingComputer has learned that threat actors defaced the Canvas login portals for roughly 330 tutorial institutions, replacing the identical outdated login pages with an extortion message. This defacement message also seemed within the Canvas app.
The defacement became as soon as allegedly triggered by a vulnerability in Instructure’s systems that allowed the threat actor to change the login portals. Instructure has since taken Canvas offline while they reply to the most modern cyberattack.
Final week, Instructure disclosed that it became as soon as investigating a cyberattack after threat actors claimed to earn stolen 280 million pupil and workers records tied to eight,809 colleges, universities, and education platforms the usage of its Canvas finding out administration system.
The ShinyHunters gang later suggested BleepingComputer that the stolen info included consumer records, private messages, enrollment info, and other info allegedly gathered thru Canvas info export aspects and APIs.
Instructure confirmed that info became as soon as stolen one day of the assault nevertheless that they are continuing to analyze the incident.
BleepingComputer has persistently contacted Instructure with questions about the assault, at the side of currently’s, and whether they conception on notifying students and workers about the records breach. Nonetheless, our emails have up to now remained unanswered.
Canvas is one of many most widely frail finding out administration systems in greater education and K-12 environments, serving to schools jam up coursework, assignments, grading, and communique between students and college.
Scam detection Who is ShinyHunters
The name ShinyHunters has lengthy been associated with a mountainous change of threat actors who earn done info breaches since 2018.
This year, threat actors the usage of the ShinyHunters name became amongst the most prolific groups conducting info theft and extortion assaults against firms worldwide.
Primarily focusing on Salesforce and other cloud SaaS environments, the threat actors are linked to a rising change of breaches engaging firms equivalent to Google, Cisco, PornHub, and online dating huge Match Community.
The extortion gang recurrently breaches third-event integration firms and uses stolen authentication tokens to fetch entry to linked SaaS environments and dangle buyer info.
The threat actors are also known for conducting tell phishing (vishing) assaults focusing on Okta, Microsoft, and Google single signal-on (SSO) accounts, impersonating IT toughen workers to trick workers into entering credentials and multi-factor authentication (MFA) codes on phishing web sites.
As BleepingComputer first reported, the ShinyHunters group has also just currently adopted software program code vishing assaults to earn Microsoft Entra authentication tokens.
After stealing credentials and authentication codes, the threat actors hijack SSO accounts to breach linked venture companies equivalent to Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, and Dropbox.
While members of the ShinyHunters gang are in fee for a mountainous change of assaults, they’re also known to feature as an extortion-as-a-provider group, conducting extortion on behalf of different threat actors in alternate for a portion of ransom funds.
There were a mountainous change of arrests linked to the ShinyHunters name, at the side of suspects linked to the Snowflake info-theft assaults, breaches at PowerSchool, and the operation of the Breached v2 hacking dialogue board.
But no subject these arrests, firms proceed to receive extortion emails signed with the message, “We’re ShinyHunters.”
Scam detection
Ninety 9% of What Mythos Found Is Peaceable Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Self sustaining Validation Summit (May perchance well perchance 12 & 14), sight how independent, context-effectively off validation finds what’s exploitable, proves controls sustain, and closes the remediation loop.
Tags
- Canvas cybercrime cybercrimehacker cybersecurity email-fraud forensics|digital-forensics Investigation login malware malwarephishing-attack online-scam private-detective scam|fraud private-eye cyber|cybersecurity private-eye phishing|phishing-attack private-investigator private-investigator hacking|hacker
Recent Posts
- Layerzero Discloses RPC Poisoning Incident Linked to $292M KelpDAO Hack
- Your Yarbo lawnmower is a backdoor into your Wi-Fi community
- Indian nationwide dies, four acquire burn injuries after dhow catches fire and capsizes approach Strait of Hormuz: Listing
- Hackable Robot Lawn Mower Unlocks a Contemporary Nightmare
- On This Day, May perhaps presumably perchance well also 9: President Donald Trump fires FBI Director James Comey



