
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Serious Citrix NetScaler memory flaw actively exploited in attacks

Mar
Serious Citrix NetScaler memory flaw actively exploited in attacks
Online fraud

Hackers are exploiting a severe severity vulnerability, tracked as CVE-2026-3055, in Citrix NetScaler ADC and NetScaler Gateway appliances to invent sensitive data.
Citrix first and famous disclosed CVE-2026-3055 in a security bulletin on March 23, alongside a high-severity escape condition flaw tracked as CVE-2026-4368. The venture impacts versions of the two products old to 14.1-60.58, versions older than 13.1-62.23, and these older than 13.1-37.262.
The seller underlined that the flaw simplest affected appliances configured as a SAML identification provider (IDP) and famous that movement is required correct for administrators working on-premise appliances.
In response to the bulletin, just a few cybersecurity companies highlighted that CVE-2026-3055 has a indispensable possibility, noting technical resemblance to the broadly exploited ‘CitrixBleed’ and CitrixBleed2’ from 2023 and 2025, respectively.
watchTowr, an organization that offers adversarial simulation and continuous testing companies, said on Saturday that it seen reconnaissance exercise focused on inclined cases and warned that in-the-wild exploitation became impending.
The following day, the researchers confirmed that possibility actors began leveraging the flaw since now not lower than March 27.to extract authentication administration session IDs, doubtless enabling a chunky takeover of NetScaler appliances.
“In-the-wild exploitation has begun, with proof from our honeypot community showing exploitation from identified possibility actor source IPs as of March twenty seventh,” reports watchTowr.
watchTowr’s diagnosis implies that CVE-2026-3055 indubitably covers now not lower than two obvious memory overread bugs, now not one. The first impacts the ‘/saml/login’ endpoint coping with SAML authentication, while the 2nd one impacts the ‘/wsfed/passive’ endpoint dilapidated for WS-Federation passive authentication.
The researchers demonstrated that the safety flaw may per chance doubtless even be leveraged to “sensitive information – including authenticated administrative session IDs.”
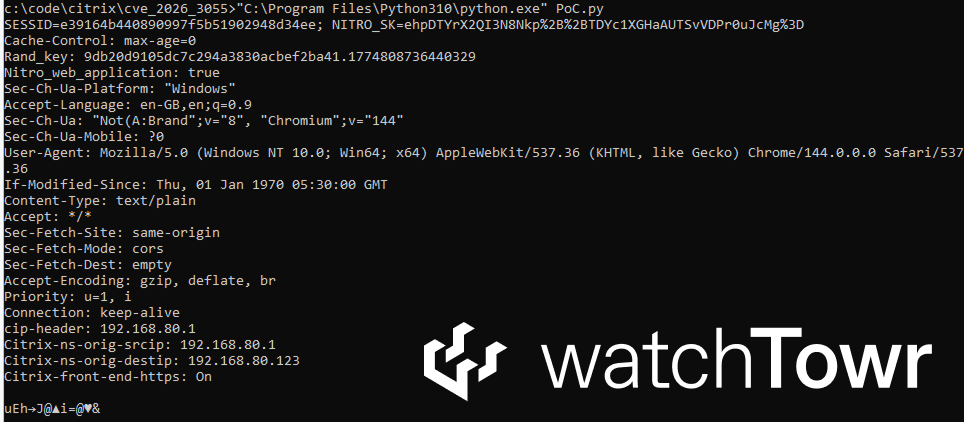
Source: watchTowr
The researchers call Citrix’s incomplete disclosure of the safety venture within the safety bulletin “disingenuous.” They furthermore shared a Python script to relief defenders establish inclined hosts in their environments.
As of publishing, Citrix’s bulletin doesn’t trace CVE-2026-3055 being exploited. BleepingComputer has contacted the company for a comment on the reported possibility actor exercise focused on unpatched appliances, but now we possess now not received a response.
As of March 28, The ShadowServer Basis sees 29,000 NetScaler and 2,250 Gateway cases uncovered online, though it is far unclear what percentage of these are inclined to CVE-2026-3055.
Online fraud Automatic Pentesting Covers Honest undoubtedly one of 6 Surfaces.
Automatic pentesting proves the path exists. BAS proves whether or now not your controls stop it. Most groups bustle one without the assorted.
This whitepaper maps six validation surfaces, reveals where protection ends, and offers practitioners with three diagnostic questions for any tool evaluation.
Recent Posts
- Disabled ACR to your TV? I prepare a router-primarily based VPN for extra protection
- Storage step forward promises get info recovery even after hackers infect your computer
- Most important Kirki flaw exploited to hijack WordPress admin accounts
- The 1 Easy Trick Hackers Broken-the final manner down to Trick Meta’s AI Bot and Take Over Instagram Accounts
- FBI file finds funding scams surged 87% in two years



